Select a Security Outsourcing Partner

- Most organizations do not have a clear understanding of their current security posture, their security goals, and the specific security services they require. Without a clear understanding of their needs, organizations may struggle to identify a partner that can meet their requirements.
- Breakdowns and lack of communication can be a significant obstacle, especially when clear lines of communication with partners, including regular check-ins, reporting, and incident response protocols, have not been clearly established.
- Ensuring that security partners’ systems and processes integrate seamlessly with existing systems can be a challenge for most organizations in addition to making sure that security partners have the necessary access and permissions to perform their services effectively.
- Adhering to security policies is rarely a priority to users as compliance often feels like an interference to daily workflow. For a lot of organizations, security policies are not having the desired effect.
Our Advice
Critical Insight
- You can outsource your responsibilities but not your accountability.
- Be aware that in most cases, the traditional approach is more profitable to MSSPs, and they may push you toward one, so make sure you get the service you want, not what they prescribe.
Impact and Result
- Determine which security responsibilities can be outsourced and which should be insourced and the right procedure to outsourcing to gain cost savings, improve resource allocation, and boost your overall security posture.
Select a Security Outsourcing Partner Research & Tools
Besides the small introduction, subscribers and consulting clients within this management domain have access to:
1. Select a Security Outsourcing Partner Storyboard – A guide to help you determine your requirements and select and manage your security outsourcing partner.
Our systematic approach will ensure that the correct procedure for selecting a security outsourcing partner is implemented. This blueprint will help you build and implement your security policy program by following our three-phase methodology: determine what to outsource, select the right MSSP, and manage your MSSP.
- Select a Security Outsourcing Partner – Phases 1-3
2. MSSP RFP Template – A customizable template to help you choose the right security service provider.
This modifiable template is designed to introduce consistency and outline key requirements during the request for proposal phase of selecting an MSSP.
- MSSP RFP Template
Infographic

Further reading
Select a Security Outsourcing Partner
Outsource the right functions to secure your business.
Analyst Perspective
Understanding your security needs and remaining accountable is the key to selecting the right partner.
The need for specialized security services is fast becoming a necessity to most organizations. However, resource challenges will always mean that organizations will still have to take practical measures to ensure that the time, quality, and service that they require from outsourcing partners have been carefully crafted and packaged to elicit the right services that cover all their needs and requirements.
Organizations must ensure that security partners are aligned not only with their needs and requirements, but also with the corporate culture. Rather than introducing hindrances to daily operations, security partners must support business goals and protect the organization’s interests at all times.
And as always, outsource only your responsibilities and do not outsource your accountability, as that will cost you in the long run.

Danny Hammond
Research Analyst
Security, Risk, Privacy & Compliance Practice
Info-Tech Research Group
Executive Summary
Your ChallengeA lack of high-skill labor increases the cost of internal security, making outsourcing more appealing. A lack of time and resources prevents your organization from being able to enable security internally. Due to a lack of key information on the subject, you are unsure which functions should be outsourced versus which functions should remain in-house. Having 24/7/365 monitoring in-house is not feasible for most firms. There is difficulty measuring the effectiveness of managed security service providers (MSSPs). |
Common ObstaclesInfoSec leaders will struggle to select the right outsourcing partner without knowing what the organization needs, such as:
InfoSec leaders must understand the business environment and their own internal security needs before they can select an outsourcing partner that fits. |
Info-Tech’s ApproachInfo-Tech’s Select a Security Outsourcing Partner takes a multi-faceted approach to the problem that incorporates foundational technical elements, compliance considerations, and supporting processes:
|
Info-Tech Insight
Mitigate security risks by developing an end-to-end process that ensures you are outsourcing your responsibilities and not your accountability.
Your Challenge
This research is designed to help organizations select an effective security outsourcing partner.
- A security outsourcing partner is a third-party service provider that offers security services on a contractual basis depending on client needs and requirements.
- An effective outsourcing partner can help an organization improve its security posture by providing access to more specialized security experts, tools, and technologies.
- One of the main challenges with selecting a security outsourcing partner is finding a partner that is a good fit for the organization's unique security needs and requirements.
- Security outsourcing partners typically have access to sensitive information and systems, so proper controls and safeguards must be in place to protect all sensitive assets.
- Without careful evaluation and due diligence to ensure that the partner is a good fit for the organization's security needs and requirements, it can be challenging to select an outsourcing partner.
Outsourcing is effective, but only if done right
- 83% of decision makers with in-house cybersecurity teams are considering outsourcing to an MSP (Syntax, 2021).
- 77% of IT leaders said cyberattacks were more frequent (Syntax, 2021).
- 51% of businesses suffered a data breach caused by a third party (Ponemon, 2021).
Common Obstacles
The problem with selecting an outsourcing partner isn’t a lack of qualified partners, it’s the lack of clarity about an organization's specific security needs.
- Most organizations do not have a clear understanding of their current security posture, their security goals, and the specific security services they require. Without a clear understanding of their needs, organizations may struggle to identify a partner that can meet their requirements.
- Breakdowns and lack of communication can be a significant obstacle, especially when clear lines of communication with partners, including regular check-ins, reporting, and incident response protocols, have not been clearly established.
- Ensuring that security partner's systems and processes integrate seamlessly with existing systems can be a challenge for most organizations. This is in addition to making sure that security partners have the necessary access and permissions to perform their services effectively.
- Adhering to security policies is rarely a priority to users, as compliance often feels like an interference to daily workflow. For a lot of organizations, security policies are not having the desired effect.
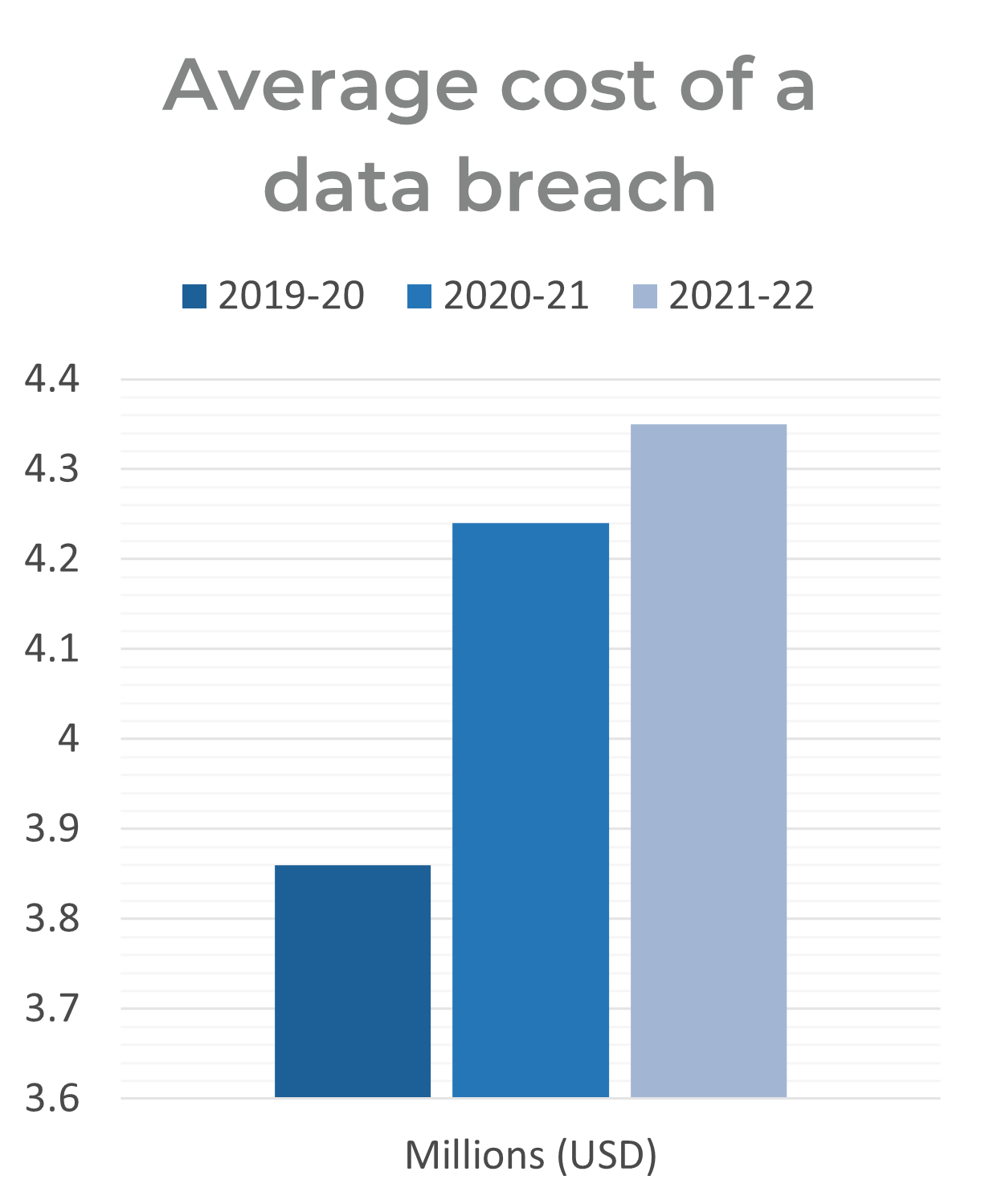
Source: IBM, 2022 Cost of a Data Breach; N=537.
Reaching an all-time high, the cost of a data breach averaged US$4.35 million in 2022. This figure represents a 2.6% increase from 2021, when the average cost of a breach was US$4.24 million. The average cost has climbed 12.7% since 2020.
Info-Tech’s methodology for selecting a security outsourcing partner
Determine your responsibilities
Determine what responsibilities you can outsource to a service partner. Analyze which responsibilities you should outsource versus keep in-house? Do you require a service partner based on identified responsibilities?
Scope your requirements
Refine the list of role-based requirements, variables, and features you will require. Use a well-known list of critical security controls as a framework to determine these activities and send out RFPs to pick the best candidate for your organization.
Manage your outsourcing program
Adopt a program to manage your third-party service security outsourcing. Trust your managed security service providers (MSSP) but verify their results to ensure you get the service level you were promised.
Select a Security Outsourcing Partner

Blueprint benefits
IT/InfoSec BenefitsReduces complexity within the MSSP selection process by highlighting all the key steps to a successful selection program. Introduces a roadmap to clearly educate about the do’s and don’ts of MSSP selection. Reduces costs and efforts related to managing MSSPs and other security partners. |
Business BenefitsAssists with selecting outsourcing partners that are essential to your organization’s objectives. Integrates outsourcing into corporate culture, leveraging organizational requirements while maximizing value of outsourcing. Reduces security outsourcing risk. |
Insight summary
Overarching insight: You can outsource your responsibilities but not your accountability.
Determine what to outsource: Assess your responsibilities to determine which ones you can outsource. It is vital that an understanding of how outsourcing will affect the organization, and what cost savings, if any, to expect from outsourcing is clear in order to generate a list of responsibilities that can/should be outsourced.
Select the right partner: Create a list of variables to evaluate the MSSPs and determine which features are important to you. Evaluate all potential MSSPs and determine which one is right for your organization
Manage your MSSP: Align the MSSP to your organization. Adopt a program to monitor the MSSP which includes a long-term strategy to manage the MSSP.
Identifying security needs and requirements = Effective outsourcing program: Understanding your own security needs and requirements is key. Ensure your RFP covers the entire scope of your requirements; work with your identified partner on updates and adaptation, where necessary; and always monitor alignment to business objectives.
Measure the value of this blueprint
Phase |
Purpose |
Measured Value |
| Determine what to outsource | Understand the value in outsourcing and determining what responsibilities can be outsourced. | Cost of determining what you can/should outsource:
|
| Select the right partner | Select an outsourcing partner that will have the right skill set and solution to identified requirements. | Cost of ranking and selecting your MSSPs:
|
| Manage your third-party service security outsourcing | Use Info-Tech’s methodology and best practices to manage the MSSP to get the best value. | Cost of creating and implementing a metrics program to manage the MSSP:
|
After each Info-Tech experience, we ask our members to quantify the real-time savings, monetary impact, and project improvements our research helped them achieve.
Overall Impact: 8.9 /10
Overall Average Cost Saved: $22,950
Overall Average Days Saved: 9
Info-Tech offers various levels of support to best suit your needs
DIY Toolkit
"Our team has already made this critical project a priority, and we have the time and capability, but some guidance along the way would be helpful."
Guided Implementation
"Our team knows that we need to fix a process, but we need assistance to determine where to focus. Some check-ins along the way would help keep us on track."
Workshop
"We need to hit the ground running and get this project kicked off immediately. Our team has the ability to take this over once we get a framework and strategy in place."
Consulting
"Our team does not have the time or the knowledge to take this project on. We need assistance through the entirety of this project."
Diagnostics and consistent frameworks are used throughout all four options.
Buying Options
Select a Security Outsourcing Partner
Client rating
Cost Savings
Days Saved
IT Risk Management · IT Leadership & Strategy implementation · Operational Management · Service Delivery · Organizational Management · Process Improvements · ITIL, CORM, Agile · Cost Control · Business Process Analysis · Technology Development · Project Implementation · International Coordination · In & Outsourcing · Customer Care · Multilingual: Dutch, English, French, German, Japanese · Entrepreneur
Tymans Group is a brand by Gert Taeymans BV
Gert Taeymans bv
Europe: Koning Albertstraat 136, 2070 Burcht, Belgium — VAT No: BE0685.974.694 — phone: +32 (0) 468.142.754
USA: 4023 KENNETT PIKE, SUITE 751, GREENVILLE, DE 19807 — Phone: 1-917-473-8669
Copyright 2017-2022 Gert Taeymans BV