Secure Operations in High-Risk Jurisdictions

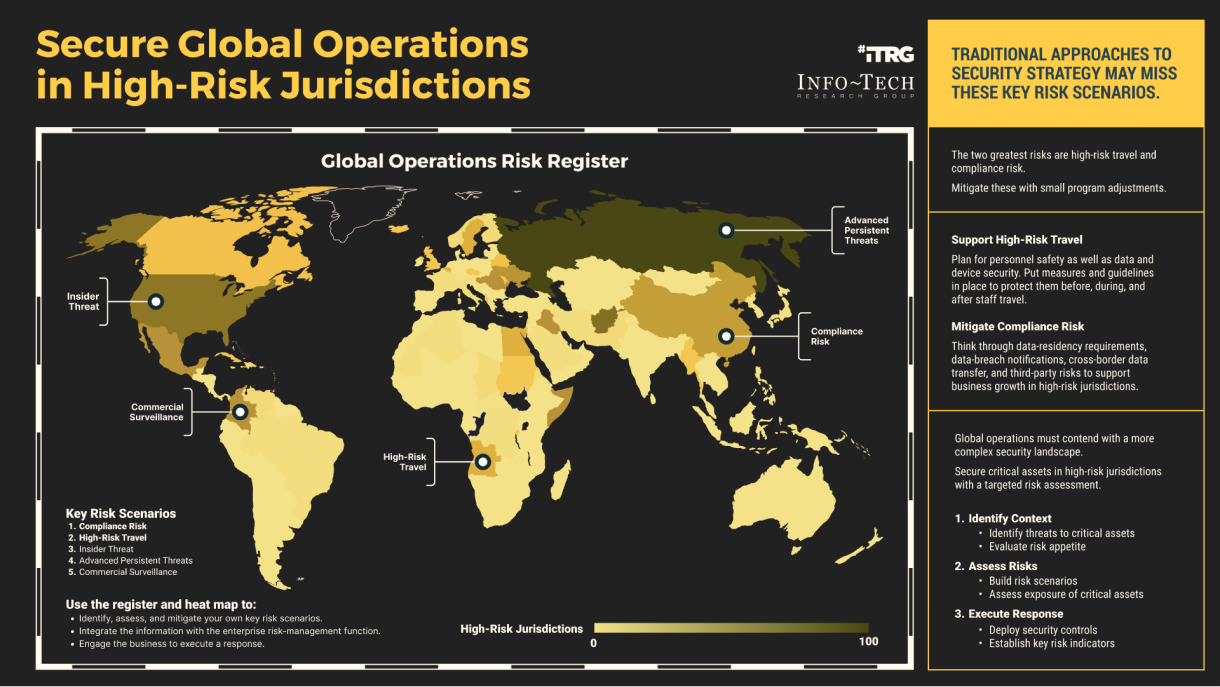
Business operations in high-risk areas of the world contend with complex threat environments and risk scenarios that often require a unique response. But traditional approaches to security strategy often miss these jurisdictional risks, leaving organizations vulnerable to threats that range from cybercrime and data breaches to fines and penalties.
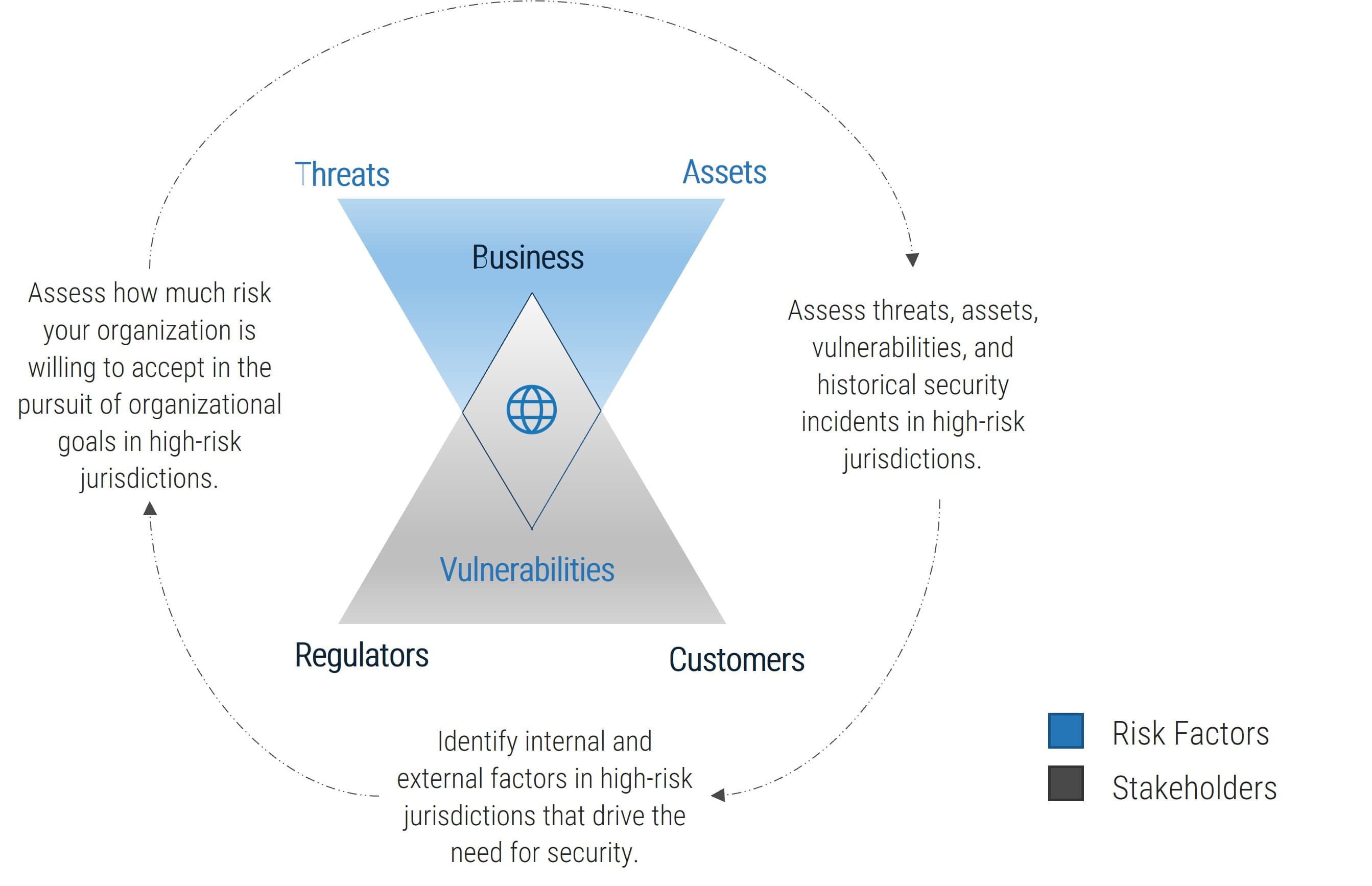
Security leaders need to identify high-risk jurisdictions, inventory critical assets, identify vulnerabilities, assess risks, and identify security controls necessary to mitigate those risks.
Secure operations and protect critical assets in high-risk regions
Across risks that include insider threats and commercial surveillance, the two greatest vulnerabilities that organizations face in high-risk parts of the world are travel and compliance. Organizations can make small adjustments to their security program to address these risks:
- Support high-risk travel: Put measures and guidelines in place to protect personnel, data, and devices before, during, and after employee travel.
- Mitigate compliance risk: Consider data residency requirements, data breach notification, cross-border data transfer, and third-party risks to support business growth.
Using these two prevalent risk scenarios in high-risk jurisdictions as examples, this research walks you through the steps to analyze the threat landscape, assess security risks, and execute a response to mitigate them.
Secure Operations in High-Risk Jurisdictions Research & Tools
Besides the small introduction, subscribers and consulting clients within this management domain have access to:
1. Secure Operations in High-Risk Jurisdictions – A step-by-step approach to mitigating jurisdictional security and privacy risks.
Traditional approaches to security strategy often miss jurisdictional risks. Use this storyboard to make small adjustments to your security program to mitigate security risks in high-risk jurisdictions.
- Secure Operations in High-Risk Jurisdictions – Phases 1-3
2. Jurisdictional Risk Register and Heat Map Tool – A tool to inventory, assess, and treat jurisdictional risks.
Use this tool to track jurisdictional risks, assess the exposure of critical assets, and identify mitigation controls. Use the geographic heatmap to communicate inherent jurisdictional risk with key stakeholders.
- Jurisdictional Risk Register and Heat Map Tool
3. Guidelines for Key Jurisdictional Risk Scenarios – Two structured templates to help you develop guidelines for two key jurisdictional risk scenarios: high-risk travel and compliance risk
Use these two templates to develop help you develop your own guidelines for key jurisdictional risk scenarios. The guidelines address high-risk travel and compliance risk.
- Digital Safety Guidelines for International Travel
- Guidelines for Compliance With Local Security and Privacy Laws Template
Infographic
Workshop: Secure Operations in High-Risk Jurisdictions
Workshops offer an easy way to accelerate your project. If you are unable to do the project yourself, and a Guided Implementation isn't enough, we offer low-cost delivery of our project workshops. We take you through every phase of your project and ensure that you have a roadmap in place to complete your project successfully.
1 Identify Context for Risk Assessment
The Purpose
Assess business requirements and evaluate security pressures to set the context for the security risk assessment.
Key Benefits Achieved
Understand the goals of the organization in high-risk jurisdictions.
Assess the threats to critical assets in these jurisdictions and capture stakeholder expectations for information security.
Activities
1.1 Determine assessment scope.
1.2 Determine business goals.
1.3 Determine compliance obligations.
1.4 Determine risk appetite.
1.5 Conduct pressure analysis.
Outputs
Business requirements
Security pressure analysis
2 Analyze Key Risk Scenarios for High-Risk Jurisdictions
The Purpose
Build key risk scenarios for high-risk jurisdictions.
Key Benefits Achieved
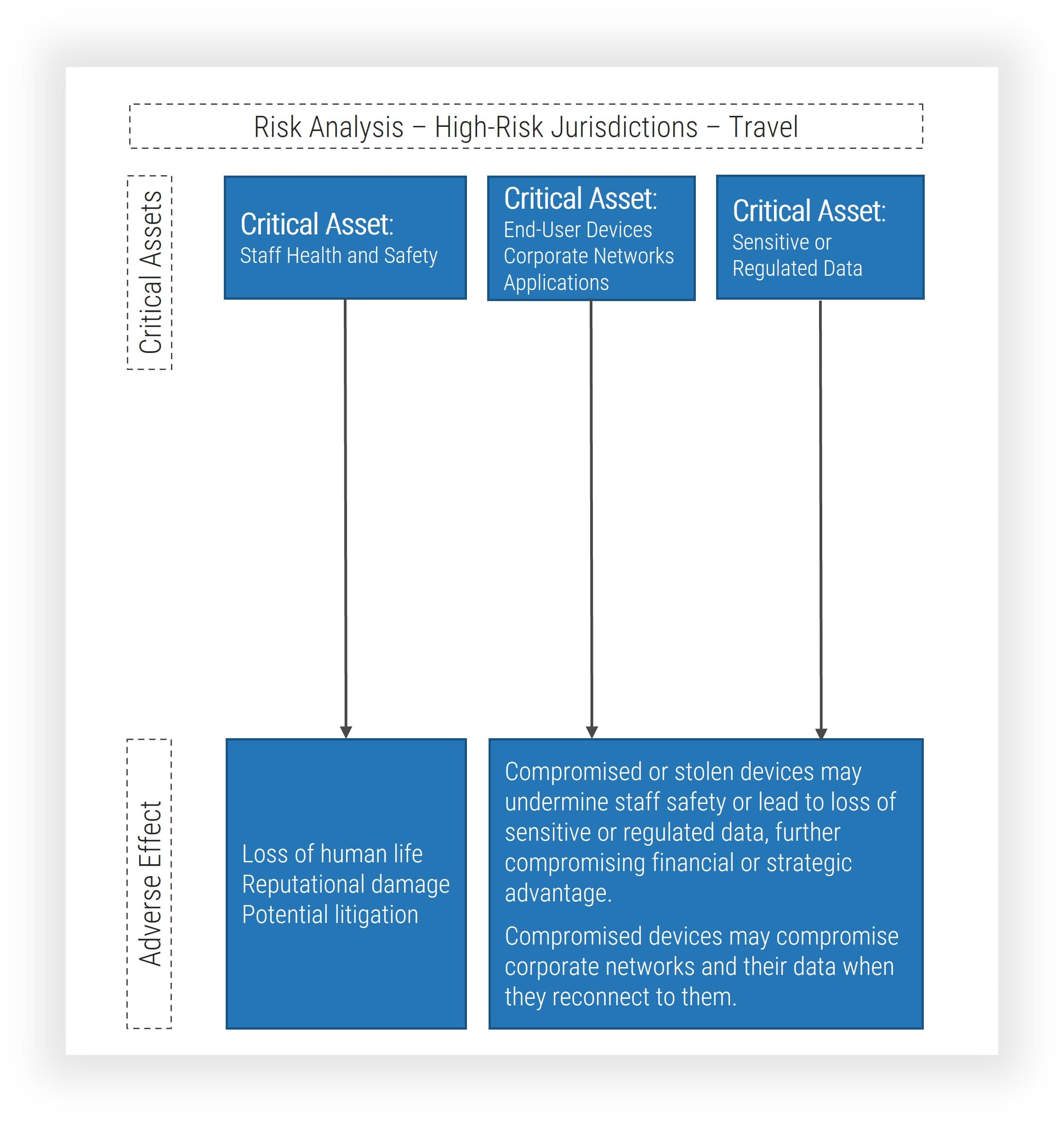
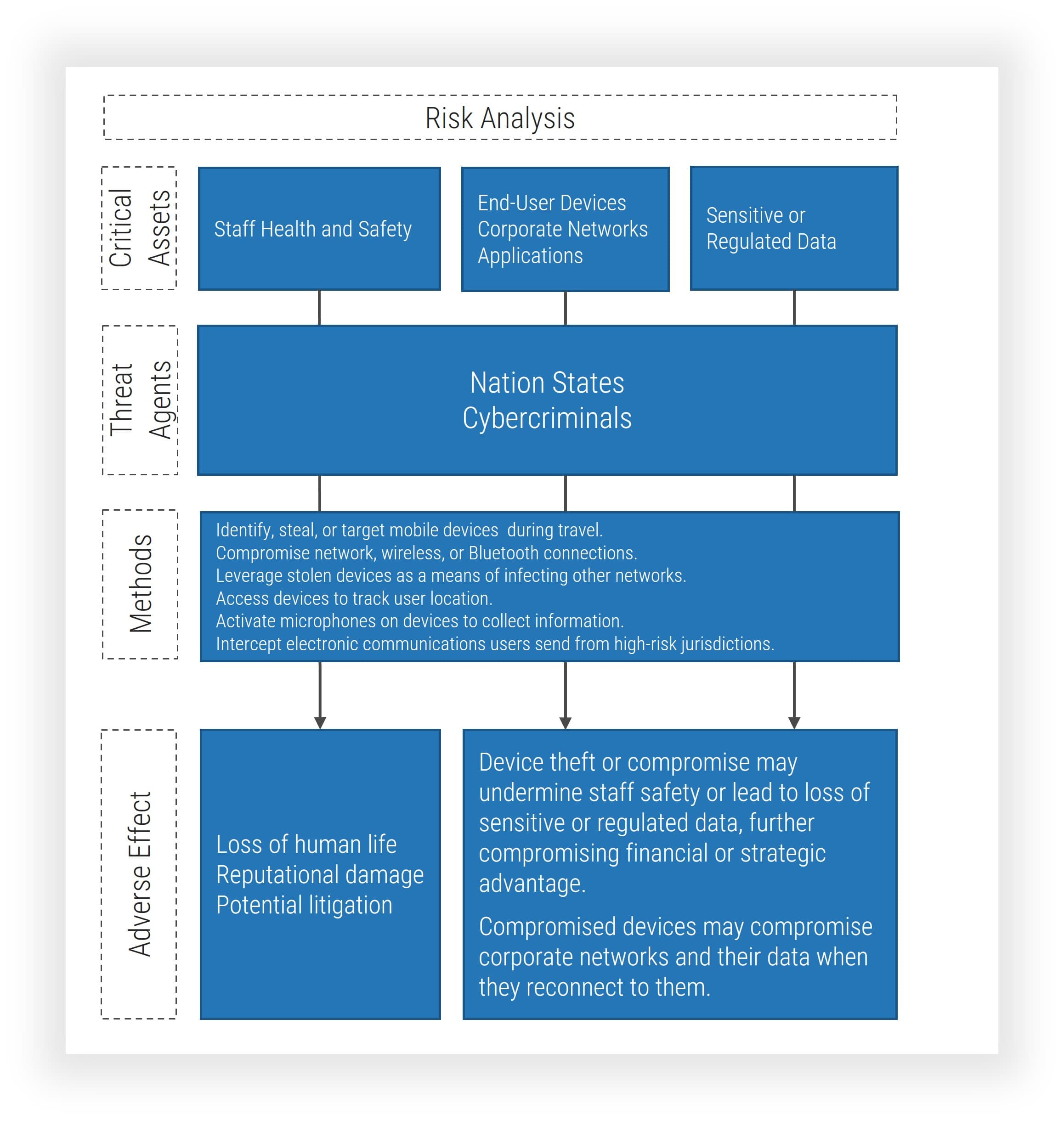
Identify critical assets in high-risk jurisdictions, their vulnerabilities to relevant threats, and the adverse impact should malicious agents exploit them.
Assess risk exposure of critical assets in high-risk jurisdictions.
Activities
2.1 Identify critical assets.
2.2 Identify threats.
2.3 Assess risk likelihood.
2.4 Assess risk impact.
Outputs
Key risk scenarios
Jurisdictional risk exposure
Jurisdictional Risk Register and Heat Map
3 Build Risk Treatment Roadmap
The Purpose
Prioritize and treat jurisdictional risks to critical assets.
Key Benefits Achieved
Build an initiative roadmap to reduce residual risks in high-risk jurisdictions.
Activities
3.1 Identify and assess risk response.
3.2 Assess residual risks.
3.3 Identify security controls.
3.4 Build initiative roadmap.
Outputs
Action plan to mitigate key risk scenarios
Further reading
Secure Operations in High-Risk Jurisdictions
Assessments often omit jurisdictional risks. Are your assets exposed?
EXECUTIVE BRIEF
Analyst Perspective
Operations in high-risk jurisdictions face unique security scenarios.
Michel Hébert
Research Director
Security and Privacy
Info-Tech Research Group

Alan Tang
Principal Research Director
Security and Privacy
Info-Tech Research Group
Traditional approaches to security strategies may miss key risk scenarios that critical assets face in high-risk jurisdictions. These include high-risk travel, heightened insider threats, advanced persistent threats, and complex compliance environments. Most organizations have security strategies and risk management practices in place, but securing global operations requires its own effort. Assess the security risk that global operations pose to critical assets. Consider the unique assets, threats, and vulnerabilities that come with operations in high-risk jurisdictions. Focus on the business activities you support and integrate your insights with existing risk management practices to ensure the controls you propose get the visibility they need. Your goal is to build a plan that mitigates the unique security risks that global operations pose and secures critical assets in high-risk areas. Don’t leave security to chance.
Executive Summary
Your Challenge
- Security leaders who support operations in many countries struggle to mitigate security risks to critical assets. Operations in high-risk jurisdictions contend with complex threat environments and security risk scenarios that often require a unique response.
- Security leaders need to identify critical assets, assess vulnerabilities, catalog threats, and identify the security controls necessary to mitigate related operational risks.
Common Obstacles
- Securing operations in high-risk jurisdictions requires additional due diligence. Each jurisdiction involves a different risk context, which complicates efforts to identify, assess, and mitigate security risks to critical assets.
- Security leaders need to engage the organization with the right questions and identify high-risk vulnerabilities and security risk scenarios to help stakeholders make an informed decision about how to assess and treat the security risks they face in high-risk jurisdictions.
Info-Tech’s Approach
Info-Tech has developed an effective approach to protecting critical assets in high-risk jurisdictions.
This approach includes tools for:
- Evaluating the security context of your organization’s high-risk jurisdictions.
- Identifying security risk scenarios unique to high-risk jurisdictions and assessing the exposure of critical assets.
- Planning and executing a response.
Info-Tech Insight
Organizations with global operations must contend with a more diverse set of assets, threats, and vulnerabilities when they operate in high-risk jurisdictions. Security leaders need to take additional steps to secure operations and protect critical assets.
Business operations in high-risk jurisdictions face a more complex security landscape
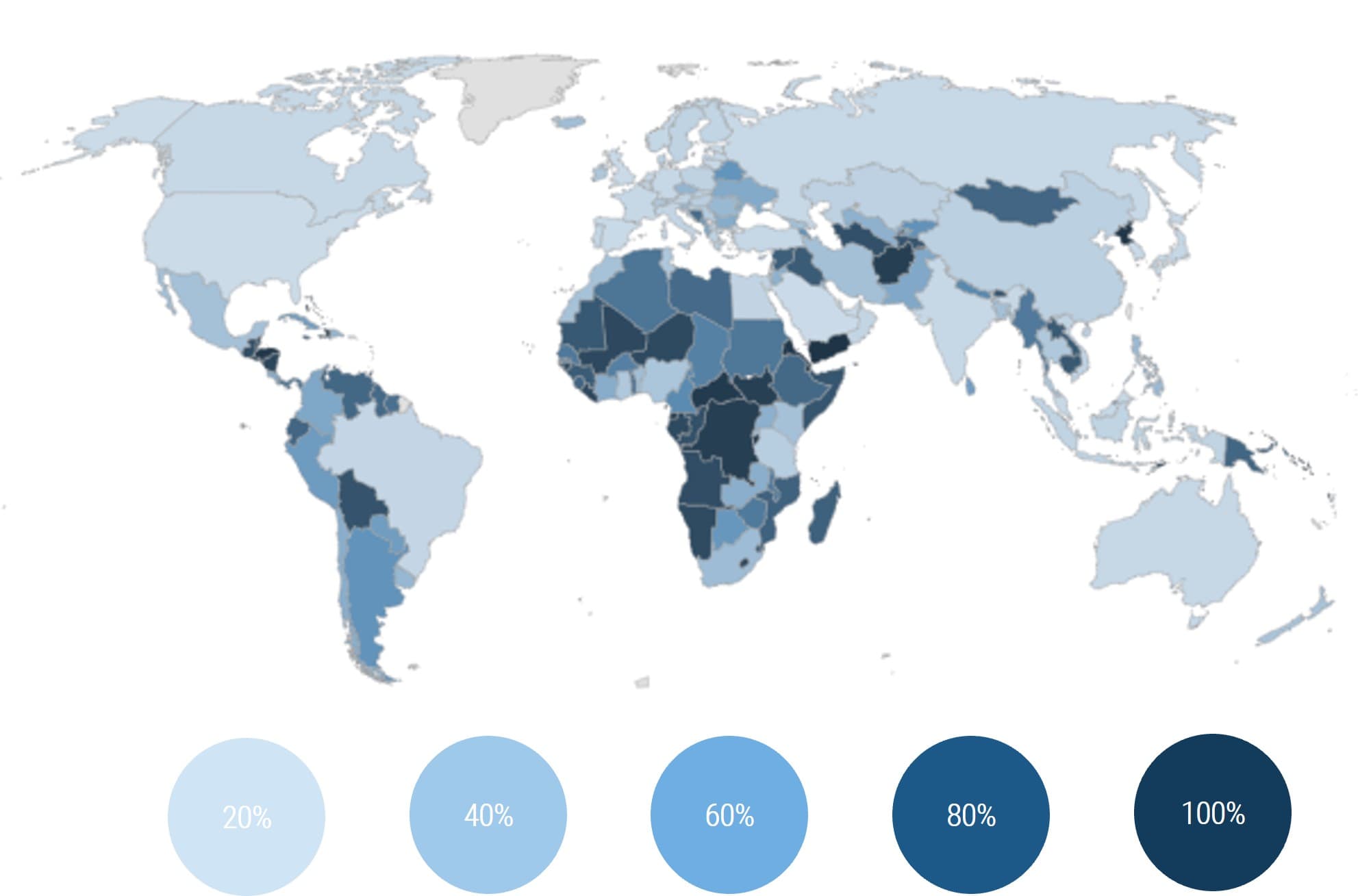
Information security risks to business operations vary widely by region.
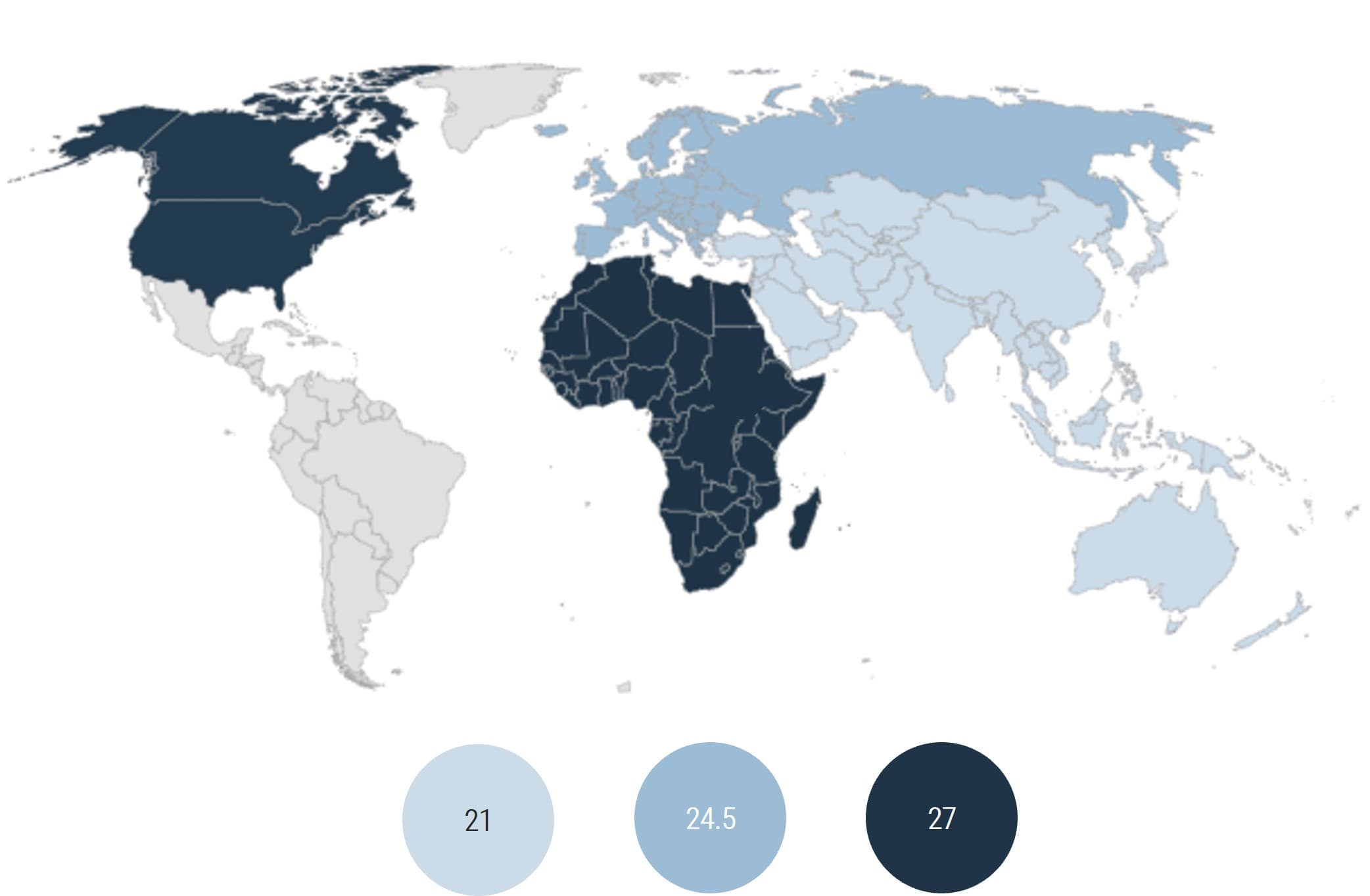
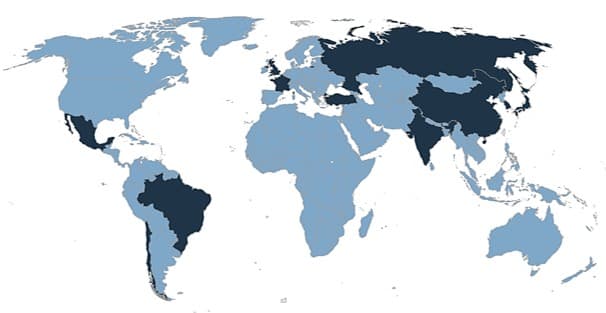
The 2022 Allianz Risk Barometer surveyed 2,650 business risk specialists in 89 countries to identify the most important risks to operations. The report identified cybercrime, IT failures, outages, data breaches, fines, and penalties as the most important global business risks in 2022, but their results varied widely by region. The standout finding of the 2022 Allianz Risk Barometer is the return of security risks as the most important threat to business operations. Security risks will continue to be acute beyond 2022, especially in Africa, the Middle East, Europe, and the Asia-Pacific region, where they will dwarf risks of supply chain interruptions, natural catastrophe, and climate change.
Global operations in high-risk jurisdictions contend with more diverse threats. These security risk scenarios are not captured in traditional security strategies.
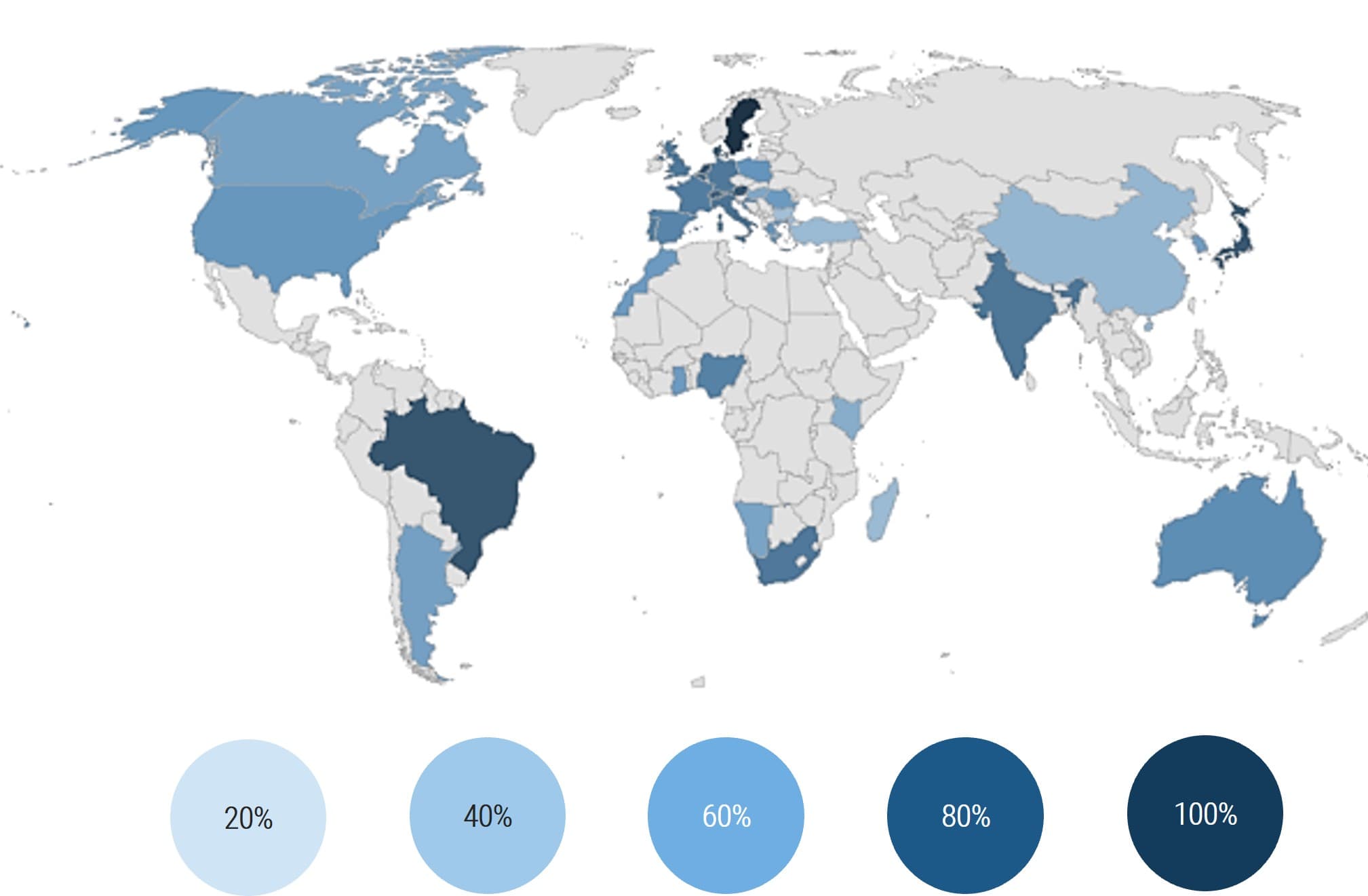
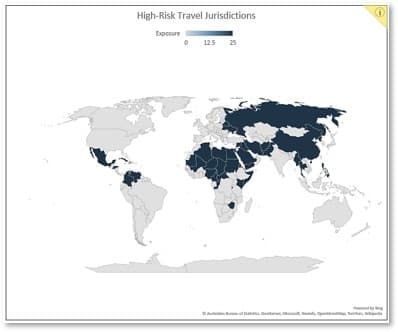
Figures represent the number of cybersecurity risks business risk specialists selected as a percentage of all business risks (Allianz, 2022). Higher scores indicate jurisdictions with higher security-related business risks. Jurisdictions without data are in grey.
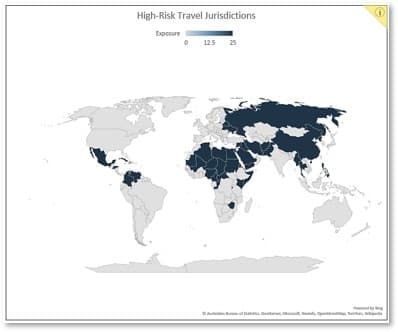
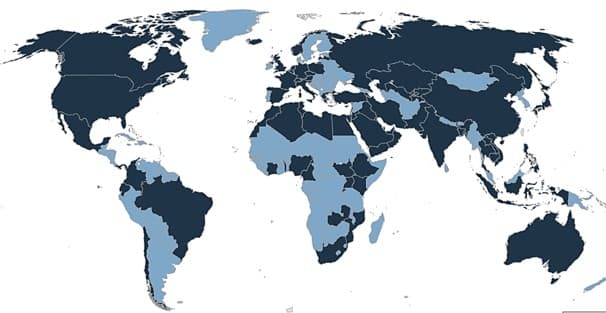
Different jurisdictions’ commitment to cybersecurity also varies widely, which increases security risks further
The Global Cybersecurity Index (GCI) provides insight into the commitment of different countries to cybersecurity.
The index assesses a country’s legal framework to identify basic requirements that public and private stakeholders must uphold and the legal instruments prohibiting harmful actions.
The 2020 GCI results show overall improvement and strengthening of the cybersecurity agenda globally, but significant regional gaps persist. Of the 194 countries surveyed:
- 33% had no data protection legislation.
- 47% had no breach notification measures in place.
- 50% had no legislation on the theft of personal information.
- 19% still had no legislation on illegal access.
Not every jurisdiction has the same commitment to cybersecurity. Protecting critical assets in high-risk jurisdictions requires additional due diligence.
The diagram sets out the score and rank for each country that took part in the Global Cybersecurity Index (ITU, 2021)
Higher scores show jurisdictions with a lower rank on the CGI, which implies greater risk. Jurisdictions without data are in grey.
Securing critical assets in high-risk jurisdictions requires additional effort
Traditional approaches to security strategy may miss these key risk scenarios.
As a result, security leaders who support operations in many countries need to take additional steps to mitigate security risks to critical assets.
Guide stakeholders to make informed decisions about how to assess and treat the security risks and secure operations.
- Engage the organization with the right questions.
- Identify critical assets and assess vulnerabilities.
- Catalogue threats and build risk scenarios.
- Identify the security controls necessary to mitigate risks.
Work with your organization to analyze the threat landscape, assess security risks unique to high-risk jurisdictions, and execute a response to mitigate them.
This project blueprint works through this process using the two most prevalent risk scenarios in high-risk jurisdictions: high-risk travel and compliance risk.
Key Risk Scenarios
- High-Risk Travel
- Compliance Risk
- Insider Threat
- Advanced Persistent Threat
- Commercial Surveillance

Travel risk is the first scenario we use as an example throughout the blueprint
- This project blueprint outlines a process to identify, assess, and mitigate key risk scenarios in high-risk jurisdictions. We use two common key risk scenarios as examples throughout the deck to illustrate how you create and assess your own scenarios.
- Supporting high-risk travel is the first scenario we will study in-depth as an example. Business growth, service delivery, and mergers and acquisitions can lead end users to travel to high-risk jurisdictions where staff, devices, and data are at risk.
- Compromised or stolen devices can provide threat actors with access to data that could compromise the organization’s strategic, economic, or competitive advantage or expose the organization to regulatory risk.
The project blueprint includes template guidance in Phase 3 to help you build and deploy your own travel guidelines to protect critical assets and support end users before they leave, during their trip, and when they return.
Before you leave
- Identify high-risk countries.
- Enable controls.
- Limit what you pack.
During your trip
- Assume you are monitored.
- Limit access to systems.
- Prevent theft.
When you return
- Change your password.
- Restore your devices.
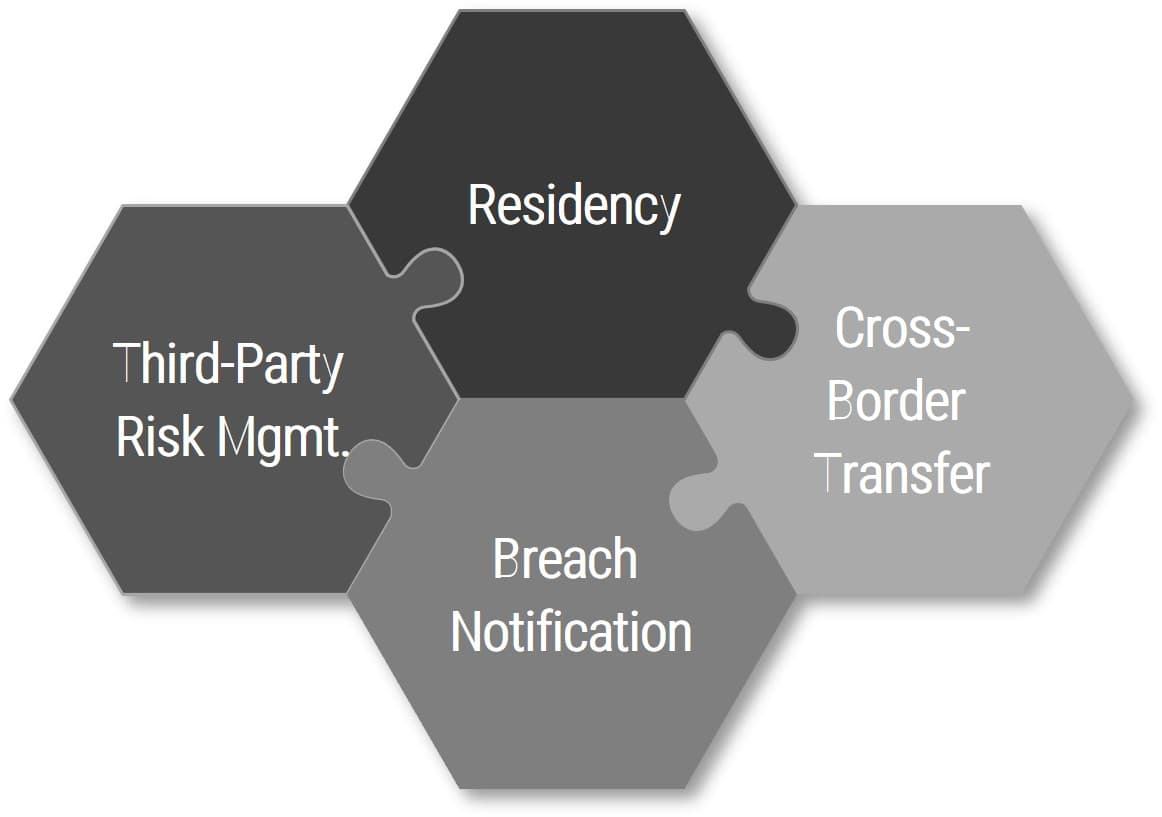
Compliance risk is the second scenario we use as an example
- Mitigating compliance risk is the second scenario we will study as an example in this blueprint. The legal and regulatory landscape is evolving rapidly to keep step with the pace of technological change. Security and privacy leaders are expected to mitigate the risk of noncompliance as the organization expands to new jurisdictions.
- Later sections will show how to think through at least four compliance risks, including:
- Cross-border data transfer
- Third-party risk management
- Data breach notification
- Data residency
The project blueprint includes template guidance in Phase 3 to help you deploy your own compliance governance controls as a risk mitigation measure.
Secure Operations in High-Risk Jurisdictions: Info-Tech’s methodology
|
1. Identify Context |
2. Assess Risks |
3. Execute Response |
|
|---|---|---|---|
|
Phase Steps |
|
|
|
|
Phase Outcomes |
|
|
|
Blueprint deliverables
Each step of this blueprint is accompanied by supporting deliverables to help you accomplish your goals:
Business Security Requirements
Identify the context for the global security risk assessment, including risk appetite and risk tolerance.
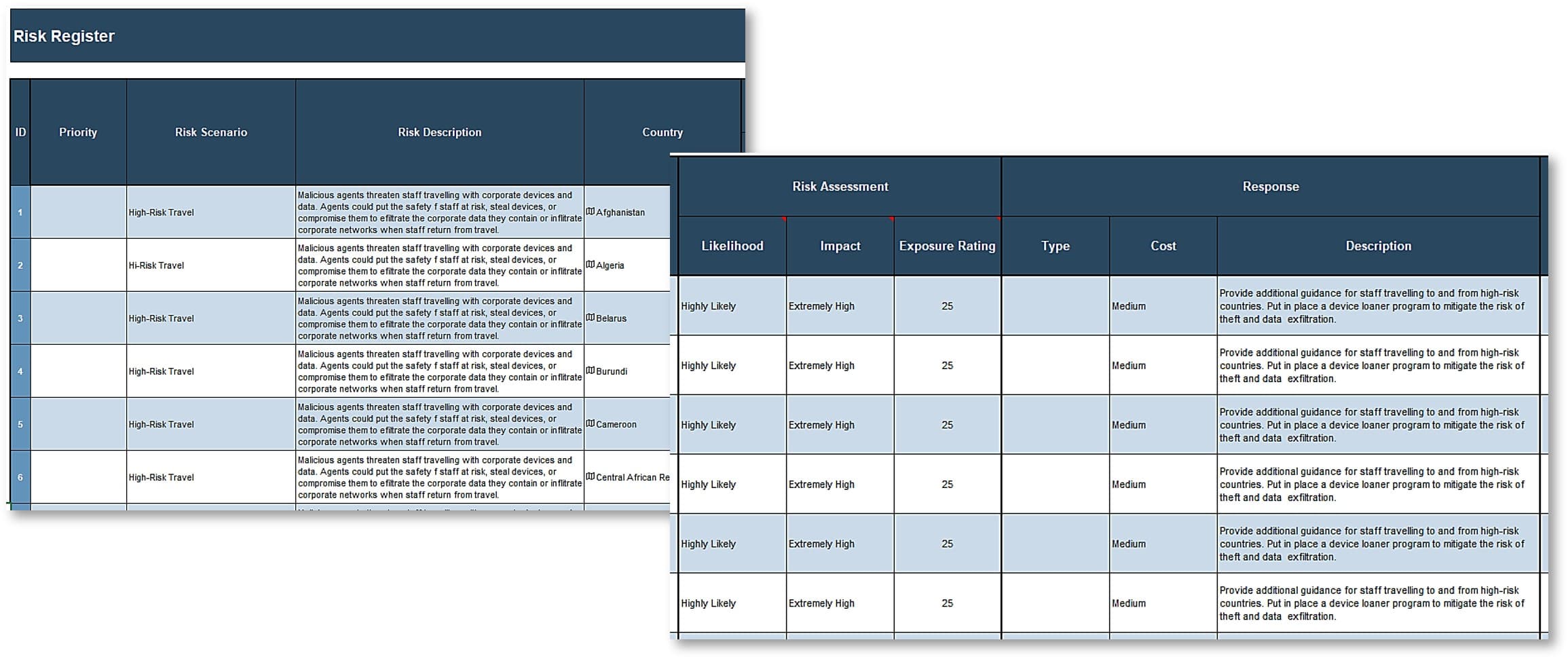
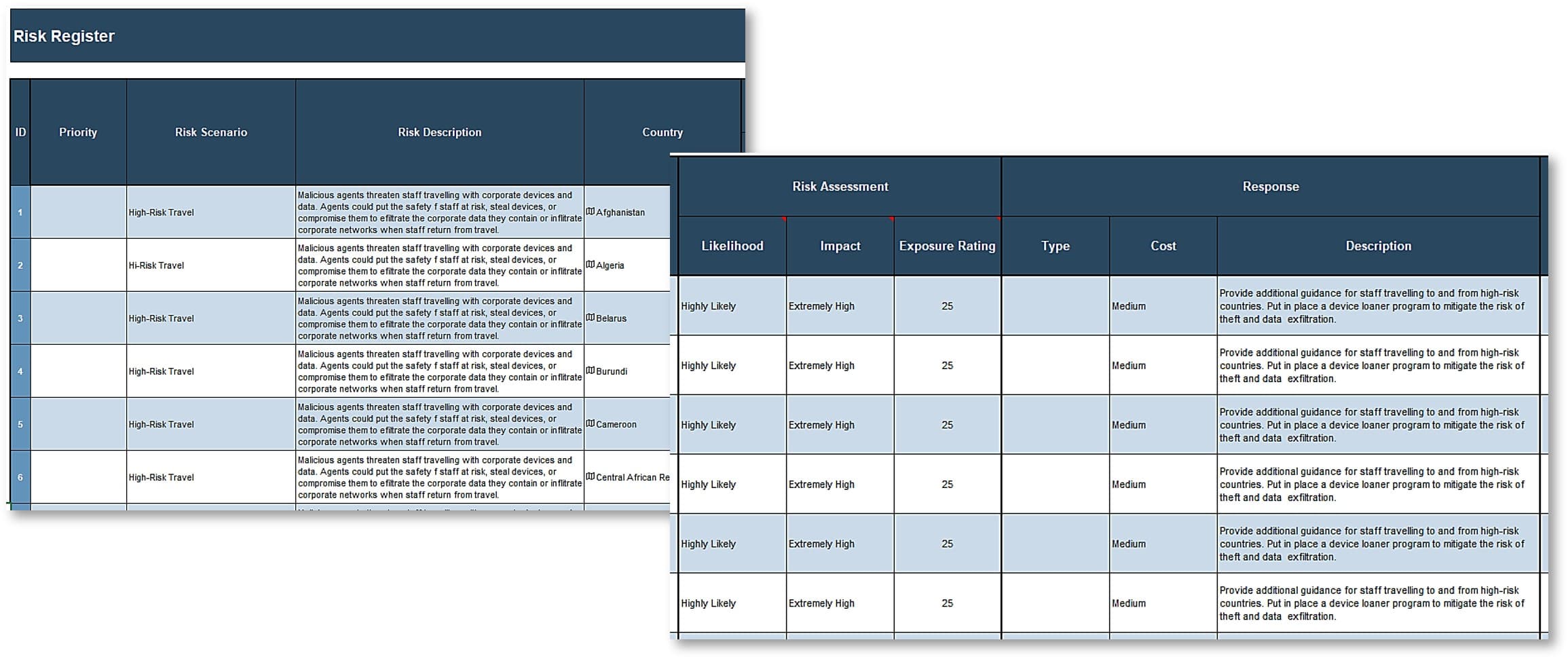
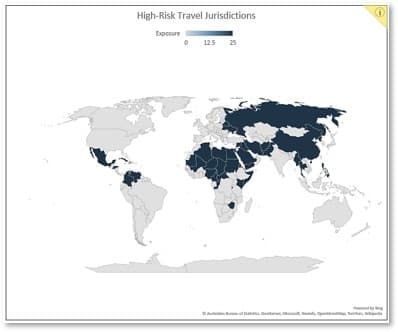
Jurisdictional Risk Register and Heatmap
Identify critical global assets and the threats they face in high-risk jurisdictions and assess exposure.
Mitigation Plan
Roadmap of initiatives and security controls to mitigate global risks to critical assets. Tools and templates to address key security risk scenarios.
Key deliverable:
Jurisdictional Risk Register and Heatmap
Use the Jurisdictional Risk Register and Heatmap Tool to capture information security risks to critical assets in high-risk jurisdictions. The tool generates a world chart that illustrates the risks global operations face to help you engage the business and execute a response.
Blueprint benefits
Protect critical assets in high-risk jurisdictions
IT Benefits
Assess and remediate information security risk to critical assets in high-risk jurisdictions.
Easily integrate your risk assessment with enterprise risk assessments to improve communication with the business.
Illustrate key information security risk scenarios to make the case for action in terms the business understands.
Business Benefits
Develop mitigation plans to protect staff, devices, and data in high-risk jurisdictions.
Support business growth in high-risk jurisdictions without compromising critical assets.
Mitigate compliance risk to protect your organization’s reputation, avoid fines, and ensure business continuity.
Quantify the impact of securing global operations
The tool included with this blueprint can help you measure the impact of implementing the research
- Use the Jurisdictional Risk Register and Heatmap Tool to describe the key risk scenarios you face, assess their likelihood and impact, and estimate the cost of mitigating measures. Working through the project in this way will help you quantify the impact of securing global operations.
Establish Baseline Metrics
- Review existing information security and risk management metrics and the output of the tools included with the blueprint.
- Identify metrics to measure the impact of your risk management efforts. Focus specifically on high-risk jurisdictions.
- Compare your results with those in your overall security and risk management program.
|
ID |
Metric |
Why is this metric valuable? |
How do I calculate it? |
|---|---|---|---|
|
1. |
Overall Exposure – High-Risk Jurisdictions |
Illustrates the overall exposure of critical assets in high-risk jurisdictions. |
Use the Jurisdictional Risk Register and Heatmap Tool. Calculate the impact times the probability rating for each risk. Take the average. |
|
2. |
# Risks Identified – High-Risk Jurisdictions |
Informs risk tolerance assessments. |
Use the Jurisdictional Risk Register and Heatmap Tool. |
|
3. |
# Risks Treated – High-Risk Jurisdictions |
Informs residual risk assessments. |
Use the Jurisdictional Risk Register and Heatmap Tool. |
|
4. |
Mitigation Cost – High-Risk Jurisdictions |
Informs cost-benefit analysis to determine program effectiveness. |
Use the Jurisdictional Risk Register and Heatmap Tool. |
|
5. |
# Security Incidents – High-Risk Jurisdictions |
Informs incident trend calculations to determine program effectiveness. |
Draw the information from your service desk or IT service management tool. |
| 6. |
Incident Remediation Cost – High-Risk Jurisdictions |
Informs cost-benefit analysis to determine program effectiveness. |
Estimate based on cost and effort, including direct and indirect cost such as business disruptions, administrative finds, reputational damage, etc. |
|
7. |
TRENDS: Program Effectiveness – High-Risk Jurisdictions |
# of security incidents over time. Remediation : Mitigation costs over time |
Calculate based on metrics 5 to 7. |
Info-Tech offers various levels of support to best suit your needs.
DIY Toolkit
"Our team has already made this critical project a priority, and we have the time and capability, but some guidance along the way would be helpful."
Guided Implementation
"Our team knows that we need to fix a process, but we need assistance to determine where to focus. Some check-ins along the way would help keep us on track."
Workshop
"We need to hit the ground running and get this project kicked off immediately. Our team has the ability to take this over once we get a framework and strategy in place."
Consulting
"Our team does not have the time or the knowledge to take this project on. We need assistance through the entirety of this project."
Diagnostics and consistent frameworks are used throughout all four options.
Guided Implementation
What does a typical GI on this topic look like?
Phase 1
Call #1: Scope project requirements, determine assessment scope, and discuss challenges.
Phase 2
Call #2: Conduct initial risk assessment and determine risk tolerance.
Call #3: Evaluate security pressures in high-risk jurisdictions.
Call #4: Identify risks in high-risk jurisdictions.
Call #5: Assess risk exposure.
Phase 3
Call #6: Treat security risks in high-risk jurisdictions.
A Guided Implementation (GI) is a series of calls with an Info-Tech analyst to help implement our best practices in your organization. A typical GI is between 8 to 12 calls over the course of 4 to 6 months.
Workshop Overview
Contact your account representative for more information. workshops@infotech.com 1-888-670-8889
|
Days 1 |
Days 2-3 |
Day 4 |
Day 5 |
|
|---|---|---|---|---|
|
Identify Context |
Key Risk Scenarios |
Build Roadmap |
Next Steps and Wrap-Up (offsite) |
|
|
Activities |
1.1.1 Determine assessment scope. 1.1.2 Determine business goals. 1.1.3 Identify compliance obligations. 1.2.1 Determine risk appetite. 1.2.2 Conduct pressure analysis. |
2.1.1 Identify assets. 2.1.2 Identify threats. 2.2.1 Assess risk likelihood. 2.2.2 Assess risk impact. |
3.1.1 Identify and assess risk response. 3.1.2 Assess residual risks. 3.2.1 Identify security controls. 3.2.2 Build initiative roadmap. |
5.1 Complete in-progress deliverables from previous four days. 5.2 Set up review time for workshop deliverables and to discuss next steps. |
|
Deliverables |
|
|
|
|
No safe jurisdictions
Stakeholders sometimes ask information security and privacy leaders to produce a list of safe jurisdictions from which to operate. We need to help them see that there are no safe jurisdictions, only relatively risky ones. As you build your security program, deepen the scope of your risk assessments to include risk scenarios critical assets face in different jurisdictions. These risks do not need to rule out operations, but they may require additional mitigation measures to keep staff, data, and devices safe and reduce potential reputational harms.
Traditional approaches to security strategy often omit jurisdictional risks.
Global operations must contend with a more complex security landscape. Secure critical assets in high-risk jurisdictions with a targeted risk assessment.
The two greatest risks are high-risk travel and compliance risk.
You can mitigate them with small adjustments to your security program.
Support High-Risk Travel
When securing travel to high-risk jurisdictions, you must consider personnel safety as well as data and device security. Put measures and guidelines in place to protect them before, during, and after travel.
Mitigate Compliance Risk
Think through data residency requirements, data breach notification, cross-border data transfer, and third-party risks to support business growth and mitigate compliance risks in high-risk jurisdictions to protect your organization’s reputation and avoid hefty fines or business disruptions.
Phase 1
Identify Context
This phase will walk you through the following activities:
- Assess business requirements to understand the goals of the organization’s global operations, as well as its risk governance, policies, and practices.
- Evaluate jurisdictional security pressures to understand threats to critical assets and capture the expectations of external stakeholders, including customers, regulators, legislators, and business partners, and assess risk tolerance.
This phase involves the following participants:
- Business stakeholders
- IT leadership
- Security team
- Risk and Compliance
Step 1.1
Assess Business Requirements
Activities
1.1.1 Determine assessment scope
1.1.2 Identify enterprise goals in high-risk jurisdictions
1.1.3 Identify compliance obligations
This step involves the following participants:
- Business stakeholders
- IT leadership
- Security team
- Risk and Compliance
Outcomes of this step
- Assess business requirements to understand the goals of the organization’s global operations, as well as its risk governance, policies, and practices.
Focus the risk assessment on high-risk jurisdictions
Traditional approaches to information security strategy often miss threats to global operations
- Successful security strategies are typically sensitive to risks to different IT systems and lines of business.
- However, securing global operations requires additional focus on high-risk jurisdictions, considering what makes them unique.
- This first phase of the project will help you evaluate the business context of operations in high-risk jurisdictions, including:
- Enterprise and security goals.
- Lines of business, physical locations, and IT systems that need additional oversight.
- Unique compliance obligations.
- Unique risks and security pressures.
- Organizational risk tolerance in high-risk jurisdictions.
Focus your risk assessment on the business activities security supports in high-risk jurisdictions and the unique threats they face to bridge gaps in your security strategy.
Identify jurisdictions with higher inherent risks
Your security strategy may not describe jurisdictional risk adequately.
- Security strategies list lines of business, physical locations, and IT systems the organization needs to secure and those whose security will depend on a third-party. You can find additional guidance on fixing the scope and boundaries of a security strategy in Phase 1 of Build an Information Security Strategy.
- However, security risks vary widely from one jurisdiction to another according to:
- Active cyber threats.
- Legal and regulatory frameworks.
- Regional security and preparedness capabilities.
- Your first task is to identify high-risk jurisdictions to target for additional oversight.
Work closely with your enterprise risk management function.
Enterprise risk management functions are often tasked with developing risk assessments from composite sources. Work closely with them to complete your own assessment.
Countries at heightened risk of money laundering and terrorism financing are examples of high-risk jurisdictions. The Financial Action Task Force and the U.S. Treasury publish reports three times a year that identify Non-Cooperative Countries or Territories.
Develop a robust jurisdictional assessment
Design an intelligence collection strategy to inform your assessment
- Relying on a single source may lead you to miscalculate risk exposure and miss relevant factors. Use a range of internal, external, and outsourced resources to identify higher-risk jurisdictions.
- Focus your jurisdictional assessment on:
- Strategic intelligence, which sheds light on trends and motivations that affect the threat landscape. For instance:
- Countries that national law enforcement identifies as posing a higher travel risk
- Third-party assessments of business and cybersecurity risk by jurisdiction
- Third-party assessment of jurisdictional commitment to information security
- Tactical intelligence, which identifies the extent of incidents in each jurisdiction. For instance:
- Vendor report on % of security attacks by type and country
- You can find additional guidance on designing a threat intelligence collection strategy in Phase 2 of Integrate Threat Intelligence into your Security Operations.
Strategic Intelligence
White papers, briefings, reports. Audience: C-Suite, board members
Tactical Intelligence
Internal reports, vendor reports. Audience: Security leaders
Operational intelligence
Indicators of compromise. Audience: IT Operations
Operational intelligence focuses on machine-readable data used to block attacks, triage and validate alerts, and eliminate threats from the network. It becomes outdated in a matter of hours and is less useful for this exercise.
Determine travel risks to bolster your assessments
Not all locations and journeys will require the same security measures.
- Travel risks vary significantly according to destination, the nature of the trip, and traveler profile.
- Access to an up-to-date country risk rating system enables your organization and individual staff to quickly determine the overall level of risk in a specific country or location.
- Based on this risk rating, you can specify what security measures are required prior to travel and what level of travel authorization is appropriate, in line with the organization's security policy or travel security procedures.
- While some larger organizations can maintain their own country risk ratings, this requires significant capacity, particularly to obtain the necessary information to keep these regularly updated.
- It may be more effective for your organization to make use of the travel risk ratings provided by an external security information provider, such as a company linked to your travel insurance or travel booking service, if available.
- Alternatively, various open-source travel risk ratings are available via embassy travel sites or other website providers.
Without a flexible system to account for the risk exposures of different jurisdictions, staff may perceive measures as a hindrance to operations.
Develop a tiered risk rating
The example below outlines potential risk indicators for high-risk travel.
|
Rating |
Description |
|---|---|
|
Low |
Generally secure with adequate physical security. Low violent crime rates. Some civil unrest during significant events. Acts of terrorism rare. Risks associated with natural disasters limited and health threats mainly preventable. |
|
Moderate |
Periodic civil unrest. Antigovernment, insurgent, or extremist groups active with sporadic acts of terrorism. Staff at risk from common and violent crime. Transport and communications services are unreliable and safety records are poor. Jurisdiction prone to natural disasters or disease epidemics. |
|
High |
Regular periods of civil unrest, which may target foreigners. Antigovernment, insurgent, or extremist groups very active and threaten political or economic stability. Violent crime rates high, often targeting foreigners. Infrastructure and emergency services poor. May be regular disruption to transportation or communications services. Certain areas off-limits to foreigners. Jurisdictions experiencing natural disasters or epidemics are considered high risk. |
|
Extreme |
Undergoing active conflict or persistent civil unrest. Risk of being caught up in a violent incident or attack is very high. Authorities may have lost control of significant portions of the country. Lines between criminality and political and insurgent violence are blurred. Foreigners are likely to be denied access to parts of the country. Transportation and communication services are severely degraded or nonexistent. Violence presents a direct threat to staff security. |
Ratings are formulated by assessing several types of risk, including conflict, political/civil unrest, terrorism, crime, and health and infrastructure risks.
1.1.1 Determine assessment scope
1 – 2 hours
- As a group, brainstorm a list of high-risk jurisdictions to target for additional assessment. Write down as many items as possible to include in:
- Lines of business
- Physical locations
- IT systems
Pay close attention to elements of the assessment that are not in scope.
|
Input |
Output |
|
|
|
Materials |
Participants |
|
|
Download the Information Security Requirements Gathering Tool
Position your efforts in a business context
Securing critical assets in high-risk jurisdictions is a business imperative
- Many companies relegate their information security strategies to their IT department. Aside from the strain the choice places on a department that already performs many different functions, it wrongly implies that mitigating information security risk is simply an IT problem.
- Managing information security risks is a business problem. It requires that organizations identify their risk appetite, prioritize relevant threats, and define risk mitigation initiatives. Business leaders can only do these activities effectively in a context that recognizes the business and financial benefits of implementing protections.
- This is notably true of businesses with operations in many different countries. Each jurisdiction has its own set of security risks the organization must account for, as well as unique local laws and regulations that affect business operations.
- In high-risk jurisdictions, your efforts must consider the unique operational challenges your organization may not face in its home country. Your efforts to secure critical assets will be most successful if you describe key risk scenarios in terms of their impact on business goals.
- You can find additional guidance on assessing the business context of a security strategy in Phase 1 of Build an Information Security Strategy.
Do you understand the unique business context of operations in high-risk jurisdictions?
1.1.2 Identify business goals
Estimated Time: 1-2 hours
- As a group, brainstorm the primary and secondary business goals of the organization. Focus your assessment on operations in high-risk jurisdictions you identified in Exercise 1.1.1. Review:
- Relevant corporate and IT strategies.
- The business goal definitions and indicator metrics in tab 2, “Goals Definition,” of the Information Security Requirements Gathering Tool.
Input | Output |
|
|
Materials | Participants |
|
|
Download the Information Security Requirements Gathering Tool
Record business goals
Capture the results in the Information Security Requirements Gathering Tool
- Record the primary and secondary business goals you identified in tab 3, “Goals Cascade,” of the Information Security Requirements Gathering Tool.
- Next, record the two security alignment goals you selected for each business goal based on the tool’s recommendations.
- Finally, review the graphic diagram that illustrates your goals on tab 6, “Results,” of the Information Security Requirements Gathering Tool.
- Revisit this exercise whenever operations expands to a new jurisdiction to capture how they contribute to the organization’s mission and vision and how the security program can support them.
Tab 3, Goals Cascade
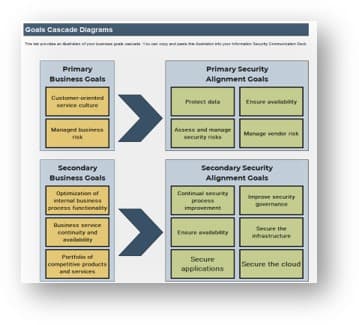
Tab 6, Results
Analyze business goals
Assess how operating in multiple jurisdictions adds nuance to your business goals
- Security leaders need to understand the direction of the business to propose relevant security initiatives that support business goals in high-risk jurisdictions.
- Operating in different jurisdictions carries its own degree of risk. The organization is subject not only to the information security risks and legal frameworks of its country of origin but also to those associated with international jurisdictions.
- You need to understand where your organization operates and how these different jurisdictions contribute to your business goals to support their performance and protect the firm’s reputation.
- This exercise will make an explicit link between security and privacy concerns in high-risk jurisdictions, what the business cares about, and what security is trying to accomplish.
If the organization is considering a merger and acquisition project that will expand operations in jurisdictions with different travel risk profiles, the security organization needs to revise the security strategy to ensure the organization can support high-risk travel and mitigate risks to critical assets.
Identify compliance obligations
Data compliance obligations loom large in high-risk jurisdictions
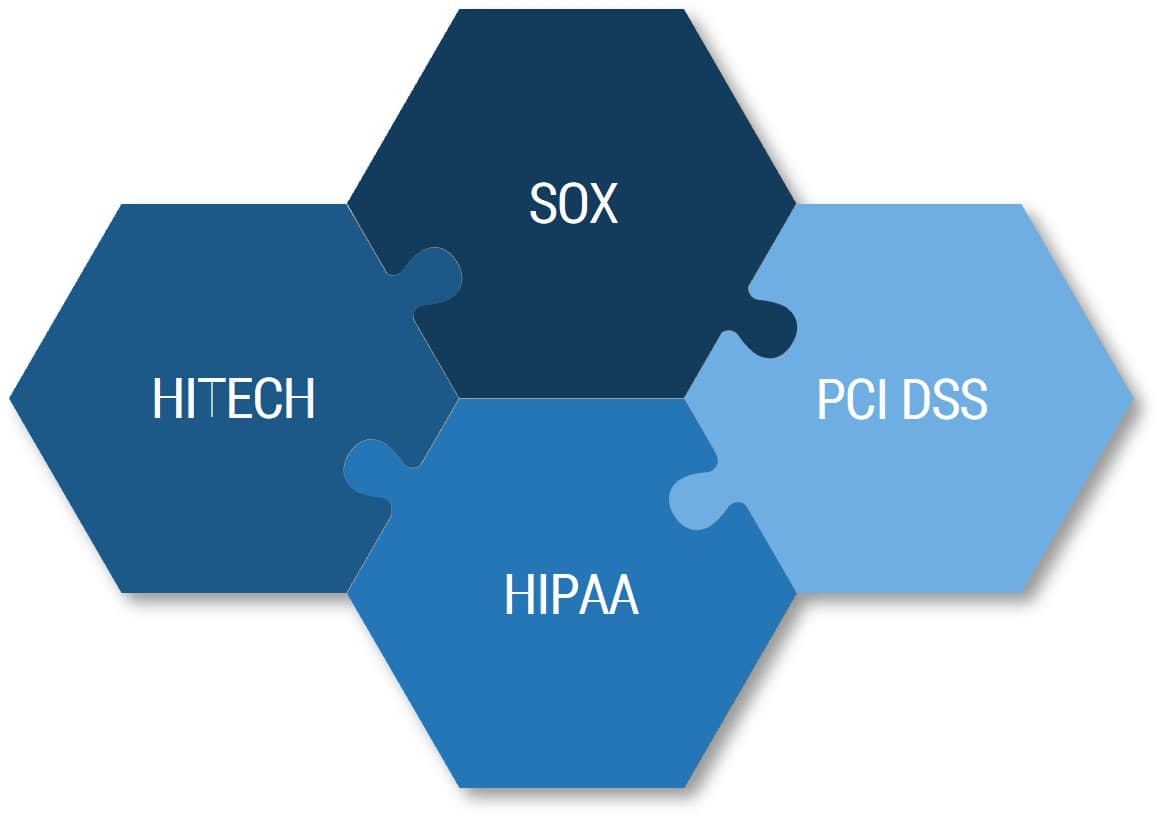
Security leaders are familiar with most conventional regulatory obligations that govern financial, personal, and healthcare data in North America and Europe.
Data privacy concerns, nationalism, and the economic value of data are all driving jurisdictions to adopt data residency and data localization and to shut down the cross-border transfer of data.
The next step requires you to consider the compliance obligations the organization needs to meet to support the business as it expands to other jurisdictions through natural growth, mergers, and acquisitions.
1.1.3 Identify compliance obligations
Estimated Time: 1-2 hours
- As a group, brainstorm compliance obligations in target jurisdictions. Focus your assessment on operations in high-risk jurisdictions.
Include:
- Laws
- Governing regulations
- Industry standards
- Contractual agreements
Input | Output |
|
|
Materials | Participants |
|
|
Download the Information Security Requirements Gathering Tool
Step 1.2
Evaluate Security Pressures
Activities
1.2.1 Conduct initial risk assessment
1.2.2 Conduct pressure analysis
1.2.3 Determine risk tolerance
This step involves the following participants:
- Security team
- Risk and Compliance
- IT leadership (optional)
Outcomes of this step
Identify threats to global assets and capture the security expectations of external stakeholders, including customers, regulators, legislators, and business partners, and determine risk tolerance.
Evaluate security pressures to set the risk context
Perform an initial assessment of high-risk jurisdictions to set the context.
Assess:
- The threat landscape.
- The security pressures from key stakeholders.
- The risk tolerance of your organization.
You should be able to find the information in your existing security strategy. If you don’t have the information, work through the next three steps of the project blueprint.
Some jurisdictions carry inherent risks
- Jurisdictional risks stem from legal, regulatory, or political factors that exist in different countries or regions. They can also stem from unexpected legal changes in regions where critical assets have exposure. Understanding jurisdictional risks is critical because they can require additional security controls.
- Jurisdictional risk tends to be higher in jurisdictions:
- Where the organization:
- Conducts high-value or high-volume financial transactions.
- Supports and manages critical infrastructure.
- Has high-cost data or data whose compromise could undermine competitive advantage.
- Has a high percentage of part-time employees and contractors.
- Experiences a high rate of employee turnover.
- Where state actors:
- Have a low commitment to cybersecurity, financial, and privacy legislation and regulation.
- Support cybercrime organizations within their borders.
Jurisdictional risk is often reduced to countries where money laundering and terrorist activities are high. In this blueprint, the term refers to the broader set of information security risks that arise when operating in a foreign country or jurisdiction.
Five key risk scenarios are most prevalent
Key Risk Scenarios
- High-Risk Travel
- Compliance Risk
- Insider Threat
- Advanced Persistent Threat
- Commercial Surveillance
Security leaders who support operations in many countries need to take additional steps to mitigate security risks to critical assets. The goal of the next two exercises is to analyze the threat landscape and security pressures unique to high-risk jurisdictions, which will inform the construction of key scenarios in Phase 2. These five scenarios are most prevalent in high-risk jurisdictions. Keep them in mind as you go through the exercises in this section.
1.2.1 Assess jurisdictional risk
1-3 hours
- As a group, review the questions on tab 2, “Risk Assessment,” of the Information Security Pressure Analysis Tool.
- Gather the required information from subject matter experts on the following risk elements with a focus on high-risk jurisdictions:
- Review each question in tab 2 of the Information Security Pressure Analysis Tool and select the most appropriate response.
Input | Output |
|
|
Materials | Participants |
|
|
For more information on how to complete the risk assessment questionnaire, see Step 1.2.1 of Build an Information Security Strategy.
1.2.2 Conduct pressure analysis
1-3 hours
- As a group, review the questions on tab 3, “Pressure Analysis,” of the Information Security Pressure Analysis Tool.
- Gather the required information from subject matter experts on the following pressure elements with a focus on high-risk jurisdictions:
- Compliance and oversight
- Customer expectations
- Business expectations
- IT expectations
For more information on how to complete the pressure analysis questionnaire, see Step 1.3 of Build an Information Security Strategy.
Input | Output |
|
|
Materials | Participants |
|
|
A low security pressure means that your stakeholders do not assign high importance to information security. You may need to engage stakeholders with the right key risk scenarios to illustrate jurisdictional risk and generate support for new security controls.
Download the Information Security Pressure Analysis Tool
Assess risk tolerance
- Risk tolerance expresses the types and amount of risk the organization is willing to accept in pursuit of its goals.
- These expectations can help you identify, manage, and report on key risk scenarios in high-risk jurisdictions.
- For instance, an organization with a low risk tolerance will require a stronger information security program to minimize operational security risks.
- It’s up to business leaders to determine the risks they are willing to accept. They may need guidance to understand how system-level risks affect the organization’s ability to pursue its goals.
A formalized risk tolerance statement can help:
- Support risk-based security decisions that align with business goals.
- Provide a meaningful rationale for security initiatives.
- Improve the transparency of investments in the organization’s security program.
- Provide guidance for monitoring inherent risk and residual risk exposure.
The role of security professionals is to identify and analyze key risk scenarios that may prevent the organization from reaching its goals.
1.2.3 Determine risk tolerance
1-3 hours
- As a group, review the questions on tab 4, “Risk Tolerance,” of the Information Security Pressure Analysis Tool.
- Gather the required information from subject matter experts on the following risk tolerance elements:
- Recent IT problems, especially downtime and data recovery issues
- Historical security incidents
- Existing security strategy
- Business impact assessments
- Service-level agreements
For more information on how to complete the risk tolerance questionnaire, see Step 1.4 of Build an Information Security Strategy.
Input | Output |
|
|
Materials | Participants |
|
|
Download the Information Security Pressure Analysis Tool
Review the output of the results tab
- The organizational risk assessment provides a high-level assessment of inherent risks in high-risk jurisdictions. Use the results to build and assess key risk scenarios in Phase 2.
- Use the security pressure analysis to inform stakeholder management efforts. A low security pressure indicates that stakeholders do not yet grasp the impact of information security on organizational goals. You may need to communicate its importance before you discuss additional security controls.
- Jurisdictions in which organizations have a low risk tolerance will require stronger information security controls to minimize operational risks.



Phase 2
Assess Security Risks to Critical Assets
This phase will walk you through the following activities:
- Identify critical assets, their vulnerabilities to relevant threats, and the adverse impact a successful threat event would have on the organization.
- Assess risk exposure of critical assets in high-risk jurisdictions for each risk scenario through an analysis of its likelihood and impact.
This phase involves the following participants:
- Security team
- Risk and Compliance
- IT leadership (optional)
Step 2.1
Identify Risks
Activities
2.1.1 Identify assets
2.1.2 Identify threats
This step involves the following participants:
- Security team
- Risk and Compliance
- IT leadership (optional)
Outcomes of this step
- Define risk scenarios that identify critical assets, their vulnerabilities to relevant threats, and the adverse impact a successful threat event would have on the organization.
This blueprint focuses on mitigating jurisdictional risks
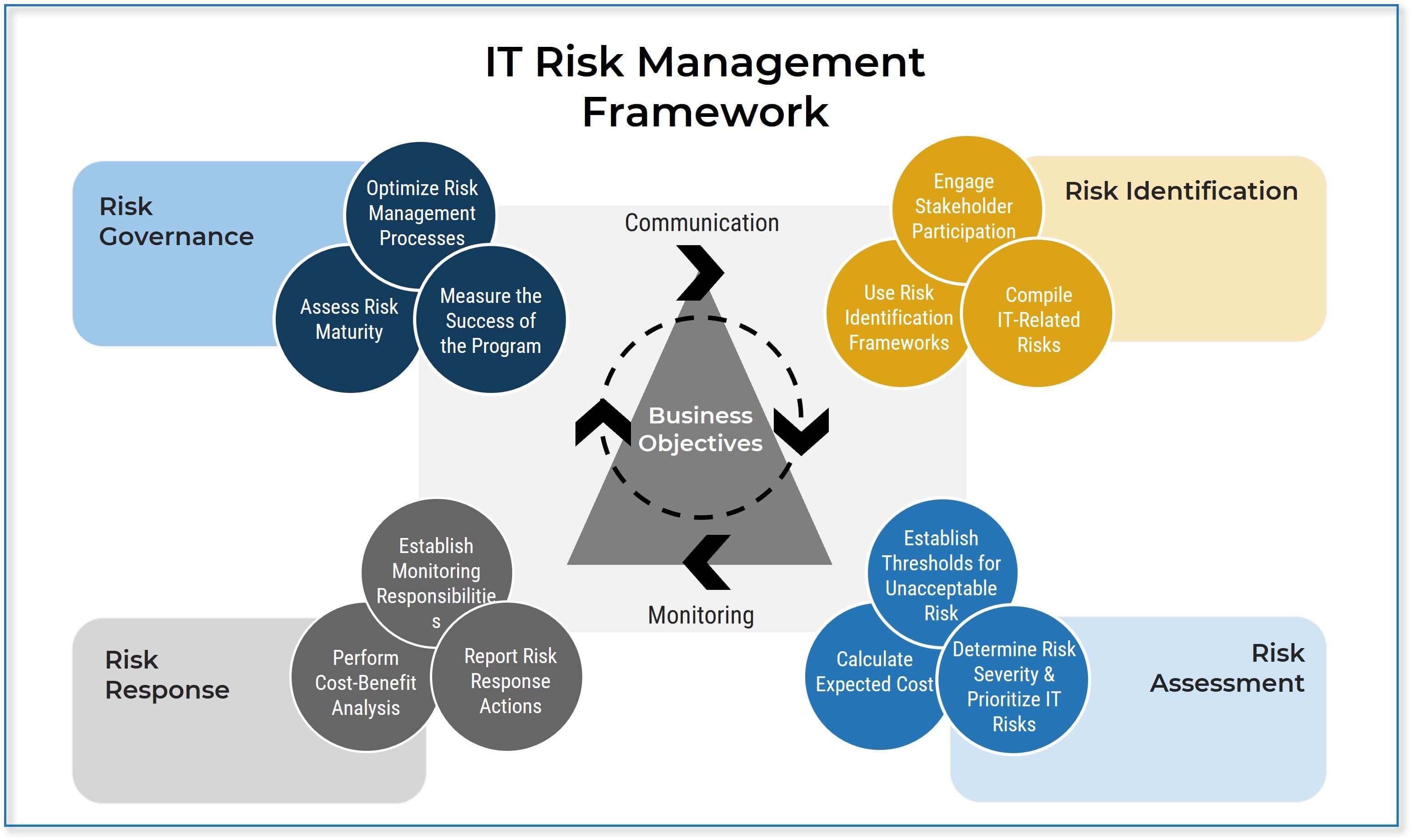
For a deeper dive into building a risk management program, see Info-Tech’s core project blueprints on risk management:
Build an IT Risk Management Program
Combine Security Risk Management Components Into One Program
Draft key risk scenarios to illustrate adverse events
Risk scenarios help decision-makers understand how adverse events affect business goals.
- Risk-scenario building is the process of identifying the critical factors that contribute to an adverse event and crafting a narrative that describes the circumstances and consequences if it were to happen.
- Risk scenarios set up the risk analysis stage of the risk assessment process. They are narratives that describe in detail:
- The asset at risk.
- The threat that can act against the asset.
- Their intent or motivation.
- The circumstances and threat actor model associated with the threat event.
- The potential effect on the organization.
- When or how often the event might occur.
Risk scenarios are further distilled into a single sentence or risk statement that communicates the essential elements from the scenario.
Well-crafted risk scenarios have four components
The second phase of the project will help you craft meaningful risk scenarios
|
Threat |
Exploits an |
Asset |
Using a |
Method |
Creating an |
Effect |
|
An actor capable of harming an asset |
Anything of value that can be affected and results in loss |
Technique an actor uses to affect an asset |
How loss materializes |
|||
|
Examples: Malicious or untrained employees, cybercriminal groups, malicious state actors |
Examples: Systems, regulated data, intellectual property, people |
Examples: Credential compromise, privilege escalation, data exfiltration |
Examples: Loss of data confidentiality, integrity, or availability; impact on staff health & safety |
|||
Risk scenarios are concise, four to six sentence narratives that describe the core elements of forecasted adverse events. Use them to engage stakeholders with the right questions and guide them to make informed decisions about how to address and treat security risks in high-risk jurisdictions.
The next slides review five key risk scenarios prevalent in high-risk jurisdictions. Use them as examples to develop your own.
Travel to high-risk jurisdictions requires special measures to protect staff, devices, and data
Governmental, academic, and commercial advisors compile lists of jurisdictions that pose greater travel risks annually.
For instance, in the US, these lists might include countries that are:
- Subjects of travel warnings by the US Department of State.
- Identified as high risk by other US government sources such as:
- The Department of the Treasury Office of Foreign Assets Control (OFAC).
- The Federal Bureau of Investigation (FBI).
- The Office of the Director of National Intelligence (ODNI).
- Compiled from academic and commercial sources, such as Control Risks.
When securing travel to high-risk jurisdictions, you must consider personnel safety as well as data and device security.
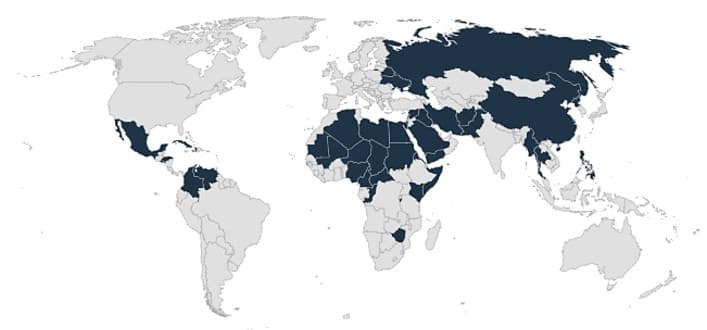
The diagram presents high-risk jurisdictions based on US governmental sources (2021) listed on this slide.
High-risk travel
Likelihood: Medium
Impact: Medium
Key Risk Scenario #1
Malicious state actors, cybercriminals, and competitors can threaten staff, devices, and data during travel to high-risk jurisdictions. Device theft or compromise may occur while traveling through airports, accessing hotel computer and phone networks, or in internet cafés or other public areas. Threat actors can exploit data from compromised or stolen devices to undermine the organization’s strategic, economic, or competitive advantage. They can also infect compromised devices with malware that delivers malicious payloads once they reconnect with home networks.
Threat Actor:
- Malicious state actors
- Cybercriminals
- Competitors
Assets:
- Staff
- IT systems
- Sensitive data
Effect:
- Compromised staff health and safety
- Loss of data
- Lost of system integrity
Methods:
- Identify, steal, or target mobile devices.
- Compromise network, wireless, or Bluetooth connections.
- Leverage stolen devices as a means of infecting other networks.
- Access devices to track user location.
- Activate microphones on devices to collect information.
- Intercept electronic communications users send from high-risk jurisdictions.
The data compliance landscape is a jigsaw puzzle of data protection and data residency requirements
Since the EU passed the GDPR in 2016, jurisdictions have turned to data regulations to protect citizen data
Data privacy concerns, nationalism, and the economic value of data are all driving jurisdictions to adopt data residency, breach notification, and cross-border data transfer regulations. As 2021 wound down to a close, nearly all the world’s 30 largest economies had some form of data regulation in place. The regulatory landscape is shifting rapidly, which complicates operations as organizations grow into new markets or engage in merger and acquisition activities.
Global operations require special attention to data-residency requirements, data breach notification requirements, and cross-border data transfer regulations to mitigate compliance risk.
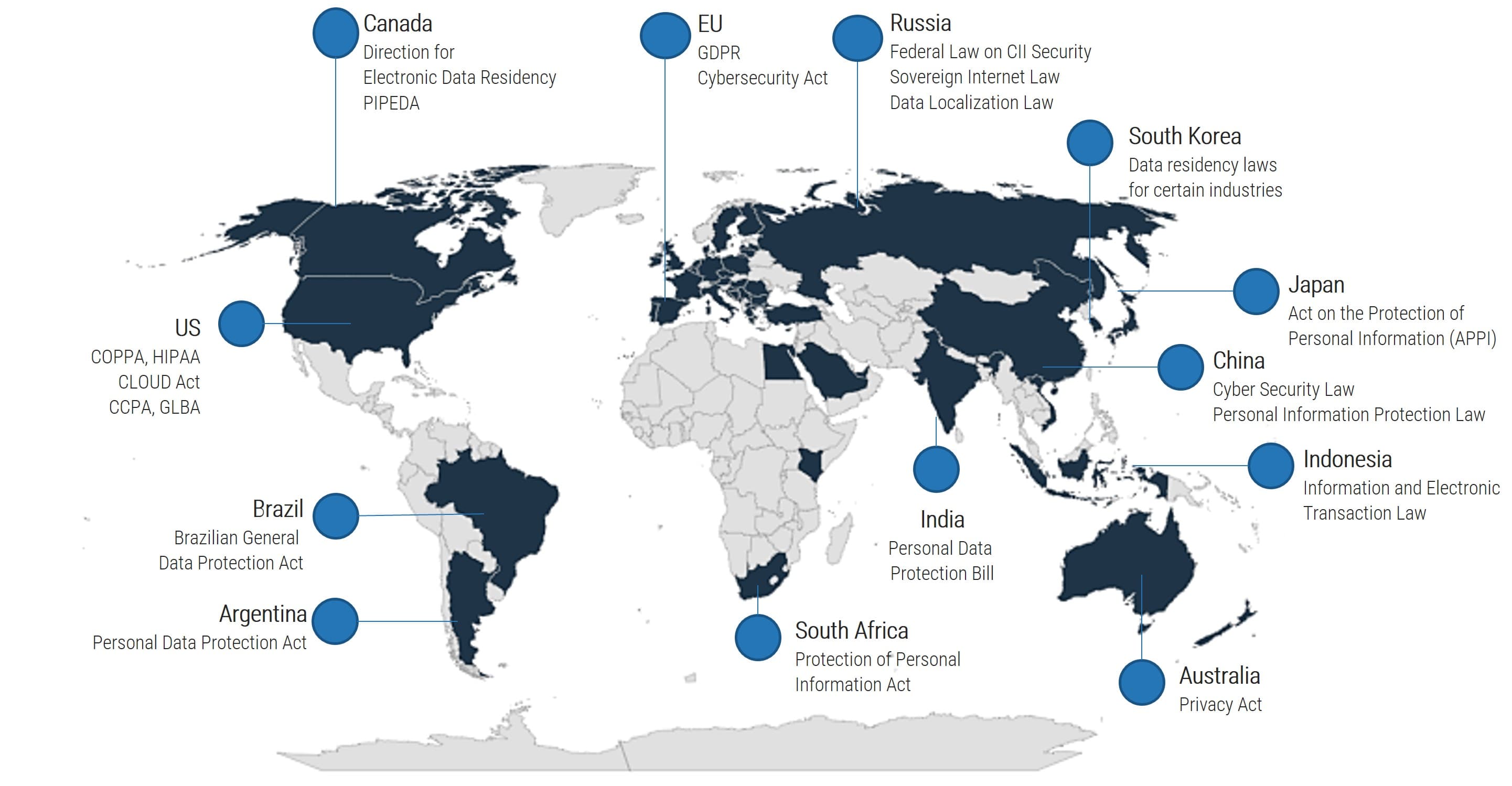
Compliance risk
Likelihood: Medium
Impact: High
Key Risk Scenario #2
Rapid changes in the privacy and security regulatory landscape threaten organizations’ ability to meet their compliance obligations from local legal and regulatory frameworks. Organizations risk reputational damage, administrative fines, criminal charges, and loss of market share. In extreme cases, organizations may lose their license to operate in high-risk jurisdictions. Shifts in the regulatory landscape can involve additional requirements for data residency, cross-border data transfer, data breach notification, and third-party risk management.
Threat Actor:
- Local, regional, and national state actors
Asset:
- Reputation, market share
- License to operate
Effect:
- Administrative fines
- Loss of reputation, brand trust, and consumer loyalty
- Loss of market share
- Suspension of business operations
- Lawsuits due to collective actions and claims
- Criminal charges
Methods:
- Shifts in the privacy and security regulatory landscape, including requirements for:
- Data residency.
- Cross-border data transfer.
- Data breach notification.
- Third-party security and privacy risk management.
The incidence of insider threats varies widely by jurisdiction in unexpected ways
On average, companies in North America, the Middle East, and Africa had the most insider incidents in 2021, while those in the Asia-Pacific region had the least.
The Ponemon Institute set out to understand the financial consequences that result from insider threats and gain insight into how well organizations are mitigating these risks.
In the context of this research, insider threat is defined as:
- Employee or contractor negligence.
- Criminal or malicious insider activities.
- Credential theft (imposter risk).
On average, the total cost to remediate insider threats in 2021 was US$15.4 million per incident.
In all regions, employee or contractor negligence occurred most frequently. Organizations in North America and in the Middle East and Africa were most likely to experience insider threat incidents in 2021.
The diagram represents the average number of insider incidents reported per organization in 2021. The results are analyzed in four regions (Ponemon Institute, 2022)
Insider threat
Likelihood: Low to Medium
Impact: High
Key Risk Scenario #3
Malicious insiders, negligent employees, and credential thieves can exploit inside access to information systems to commit fraud, steal confidential or commercially valuable information, or sabotage computer systems. Insider threats are difficult to identify, especially when security is geared toward external threats. They are often familiar with the organization’s data and intellectual property as well as the methods in place to protect them. An insider may steal information for personal gain or install malicious software on information systems. They may also be legitimate users who make errors and disregard policies, which places the organization at risk.
Threat Actor:
- Malicious insiders
- Negligent employees
- Infiltrators
Asset:
- Sensitive data
- Employee credentials
- IT systems
Effects:
- Loss of system integrity
- Loss of data confidentiality
- Financial loss
Methods:
- Infiltrators may compromise credentials.
- Malicious or negligent insiders may use corporate email to steal or share sensitive data, including:
- Regulated data.
- Intellectual property.
- Critical business information.
- Malicious agents may facilitate data exfiltration, as well as open-port and vulnerability scans.
The risk of advanced persistent threats is more prevalent in Central and South America and the Asia-Pacific region
Attacks from advanced persistent threat (APT) actors are more sophisticated than traditional ones.
- More countries will use legal indictments as part of their cyber strategy. Exposing toolsets of APT groups carried out at the governmental level will drive more states to do the same.
- Expect APTs to increasingly target network appliances like VPN gateways as organizations continue to sustain hybrid workforces.
- The line between APTs and state-sanctioned ransomware groups is blurring. Expect cybercriminals to wield better tools, mount more targeted attacks, and use double-extortion tactics.
- Expect more disruption and collateral damage from direct attacks on critical infrastructure.
Top 10 Significant Threat Actors:
- Lazarus
- DeathStalker
- CactusPete
- IAmTheKing
- TransparentTribe
- StrongPity
- Sofacy
- CoughingDown
- MuddyWater
- SixLittleMonkeys
Top 10 Targets:
- Government
- Banks
- Financial Institutions
- Diplomatic
- Telecommunications
- Educational
- Defense
- Energy
- Military
- IT Companies
Top 12 countries targeted by APTs (Kaspersky, 2020)
Track notable APTs to revise your list of high-risk jurisdictions and review the latest tactics and techniques
Governmental advisors track notable APT actors that pose greater risks.
The CISA Shields Up site, SANS Storm Center site, and MITRE ATT&CK group site provide helpful and timely information to understand APT risks in different jurisdictions.
The following threat actors are currently associated with cyberattacks affiliated with the Russian government.
|
Activity Group |
Risks |
|---|---|
|
Known as Fancy Bear, this threat group has been tied to espionage since 2004. They compromised the Hillary Clinton campaign, amid other major events. |
|
| APT29 (SVT) |
Tied to espionage since 2008. Reportedly compromised the Democratic National Committee in 2015. Cited in the 2021 SolarWinds compromise. |
| Buhtrap/RTM Group |
Group focused on financial targets since 2014. Currently known to target Russian and Ukrainian banks. |
| Gamaredon |
Operating in Crimea. Aligned with Russian interests. Has previously targeted Ukrainian government officials and organizations. |
| DEV-0586 |
Carried out wiper malware attacks on Ukrainian targets in January 2022. |
| UNC1151 |
Active since 2016. Linked to information operation campaigns and the distribution of anti-NATO material. |
| Conti |
Most successful ransomware gang of 2021, with US$188M revenue. Supported Russian invasion of Ukraine, threatening attacks on allied critical infrastructure. |
Sources: MITRE ATT&CK; Security Boulevard, 2022; Reuters, 2022; The Verge, 2022
Advanced persistent threat
Likelihood: Low to Medium
Impact: High
Key Risk Scenario #4
Advanced persistent threats are state actors or state-sponsored affiliates with the means to avoid detection by anti-malware software and intrusion detection systems. These highly-skilled and persistent malicious agents have significant resources with which to bypass traditional security controls, establish a foothold in the information technology infrastructure, and exfiltrate data undetected. APTs have the resources to adapt to a defender’s efforts to resist them over time. The loss of system integrity and data confidentiality over time can lead to financial losses, business continuity disruptions, and the destruction of critical infrastructure.
Threat Actor:
- State actors
- State-sponsored affiliates
Asset:
- Sensitive data
- IT systems
- Critical infrastructure
Effects:
- Loss of system integrity
- Loss of data confidentiality
- Financial loss
- Business continuity disruptions
- Infrastructure destruction
Methods:
- Persistent, consistent attacks using the most advanced threats and tactics to bypass security defenses.
- The goal of APTs is to maintain access to networks for prolonged periods without being detected.
- The median dwell time differs widely between regions. FireEye reported the mean dwell time for 2018:
- Americas: 71 days
- Europe, Middle East, and Africa: 177 days
- Asia-Pacific: 204 days
Sources: Symantec, 2011; FireEye, 2019
Threat agents have deployed invasive technology for commercial surveillance in at least 76 countries since 2015
State actors and their affiliates purchased and used invasive spyware from companies in Europe, Israel, and the US.
- “Customers are predominantly repressive regimes looking for new ways to control the flow of information and stifle dissent. Less than 10% of suspected customers are considered full democracies by the Economist Intelligence Unit.” (Top10VPN, 2021)
- Companies based in economically developed and largely democratic states are profiting off the technology.
- The findings demonstrate the need to consider geopolitical realities when assessing high-risk jurisdictions and to take meaningful action to increase layered defenses against invasive malware.
- Spyware is having an increasingly well-known impact on civil society. For instance, since 2016, over 50,000 individual phone numbers have been identified as potential targets by NSO Group, the Israeli manufacturers of the notorious Pegasus Spyware. The target list contained the phone numbers of politicians, journalists, activists, doctors, and academics across the world.
- The true number of those affected by spyware is almost impossible to determine given that many fall victim to the technology and do not notice.
Countries where commercial surveillance tools have been deployed (“Global Spyware Market Index,” Top10VPN, 2021)
The risks and effects of spyware vary greatly
Spyware can steal mundane information, track a user’s every move, and everything in between.
Adware
Software applications that display advertisements while the program is running.
Keyboard Loggers
Applications that monitor and record keystrokes. Malicious agents use them to steal credentials and sensitive enterprise data.
Trojans
Applications that appear harmless but inflict damage or data loss to a system.
Mobile Spyware
Surveillance applications that infect mobile devices via SMS or MMS channels, though the most advanced can infect devices without user input.
State actors and their affiliates use system monitors to track browsing habits, application usage, and keystrokes and capture information from devices’ GPS location data, microphone, and camera. The most advanced system monitor spyware, such as NSO Group’s Pegasus, can infect devices without user input and record conversations from end-to-end encrypted messaging systems.
Commercial surveillance
Likelihood: Low to Medium
Impact: Medium
Key Risk Scenario #5
Malicious agents can deploy malware on end-user devices with commercial tools available off the shelf to secretly monitor the digital activity of users. Attacks exploit widespread vulnerabilities in telecommunications protocols. They occur through email and text phishing campaigns, malware embedded in untested applications, and sophisticated zero-click attacks that deliver payloads without requiring user interactions. Attacks target sensitive as well as mundane information. They can be used to track employee activities, investigate criminal activity, or steal credentials, credit card numbers, or other personally identifiable information.
Threat Actor:
- State actors
- State-sponsored affiliates
Asset:
- Sensitive data
- Staff health and safety
- IT systems
Effects:
- Data breaches
- Loss of data confidentiality
- Increased risk to staff health and safety
- Misuse of private data
- Financial loss
Methods:
- Email and text phishing attacks that delivery malware payloads
- Sideloading untested applications from a third-party source rather than an official retailer
- Sophisticated zero-click attacks that deliver payloads without requiring user interaction
Use the Jurisdictional Risk Register and Heatmap Tool
The tool included with this blueprint can help you draft risk scenarios and risk statements in this section.
The risk register will capture a list of critical assets and their vulnerabilities, the threats that endanger them, and the adverse effect your organization may face.
Download the Jurisdictional Risk Register and Heatmap Tool
2.1.1 Identify assets
1 – 2 hours
- As a group, consider critical or mission-essential functions in high-risk jurisdictions and the systems on which they depend. Brainstorm a list of the organization’s mission-supporting assets in high-risk jurisdictions. Consider:
- Staff
- Critical IT systems
- Sensitive data
- Critical operational processes
- Information systems.
- Sensitive or regulated data.
- Staff health and safety.
- Critical operations and objectives.
- Organizational finances.
- Reputation and brand loyalty
Threat | Exploits an | Asset | Using a | Method | Creating an | Effect |
Inputs for risk scenario identification
Input | Output |
|
|
Materials | Participants |
|
|
Threat | Exploits an | Asset | Using a | Method | Creating an | Effect |
Inputs for risk scenario identification
Model threats to narrow the range of scenarios
Motives and capabilities to perform attacks on critical assets vary across different threat actors.
|
Category |
Actions |
Motivation |
Sophistication |
|---|---|---|---|
|
Nation-states |
Cyberespionage, cyberattacks |
Geopolitical |
High. Dedicated resources and personnel, extensive planning and coordination. |
|
Proxy organizations |
Espionage, destructive attacks |
Geopolitical, Ideological, Profit |
Moderate. Some planning and support functions and technical expertise. |
|
Cybercrime |
Theft, fraud, extortion |
Profit |
Moderate. Some planning and support functions and technical expertise. |
|
Hacktivists |
Disrupt operations, attack brands, release sensitive data |
Ideological |
Low. Rely on widely available tools that require little skill to deploy. |
|
Insiders |
Destruction or release of sensitive data, theft, exposure through negligence |
Incompetence, Discontent |
Internal access. Acting on their own or in concert with any of the above. |
- Criminals, hacktivists, and insiders vary in sophistication. Some criminal groups demonstrate a high degree of sophistication; however, a large cyber event that damages critical infrastructure does not align with their incentives to make money at minimal risk.
- Proxy actors conduct offensive cyber operations on behalf of a beneficiary. They may be acting on behalf of a competitor, national government, or group of individuals.
- Nation-states engage in long-term espionage and offensive cyber operations that support geopolitical and strategic policy objectives.
2.1.2 Identify threats
1 – 2 hours
- Review the outputs from activity 1.1.1 and activity 2.1.1.
- Identify threat agents that could undermine the security of critical assets in high-risk jurisdictions. Include internal and external actors.
- Assess their motives, means, and opportunities.
- Which critical assets are most attractive? Why?
- What paths and vulnerabilities can threat agents exploit to reach critical assets without going through a control?
- How could they defeat existing controls? Draw on the MITRE framework to inform your analysis.
- Once agents defeat a control, what further attack can they launch?
Threat | Exploits an | Asset | Using a | Method | Creating an | Effect |
Inputs for risk scenario identification
Input | Output |
|
|
Materials | Participants |
|
|
2.1.2 Identify threats (continued)
1 – 2 hours
- On a whiteboard, brainstorm how threat agents will exploit vulnerabilities in critical assets to reach their goal. Redefine attack vectors to capture what could result from a successful initial attack.
For example:
- State actors and cybercriminals may steal or compromise end-user devices during travel to high-risk jurisdictions using malware they embed in airport charging stations, internet café networks, or hotel business centers.
- Compromised devices may infect corporate networks and threaten sensitive data once they reconnect to them.
Threat | Exploits an | Asset | Using a | Method | Creating an | Effect |
Bring together the critical risk elements into a single risk scenario
Summarize the scenario further into a single risk statement
Risk Scenario: High-Risk Travel
State actors and cybercriminals can threaten staff, devices, and data during travel to high-risk jurisdictions. Device theft or compromise may occur while traveling through airports, accessing hotel computer and phone networks, or in internet cafés or other public areas. Threat actors can exploit data from compromised or stolen devices to undermine the organization’s strategic, economic, or competitive advantage. They can also infect compromised devices with malware that delivers malicious payloads once they reconnect with home networks.
Risk Statement
Cybercriminals compromise end-user devices during travel to high-risk jurisdictions, jeopardizing staff safety and leading to loss of sensitive data.
Risk Scenario: Compliance Risk
Rapid changes in the privacy and security regulatory landscape threaten an organization’s ability to meet its compliance obligations from local legal and regulatory frameworks. Organizations that fail to do so risk reputational damage, administrative fines, criminal charges, and loss of market share. In extreme cases, organizations may lose their license to operate in high-risk jurisdictions. Shifts in the regulatory landscape can involve additional requirements for data residency, cross-border data transfer, data breach notification, and third-party risk management.
Risk Statement
Rapid changes in the privacy and security regulations landscape threaten our ability to remain compliant, leading to reputational and financial loss.
Fill out the Jurisdictional Risk Register and Heatmap Tool
The tool is populated with data from two key risk scenarios: high-risk travel and compliance risk.
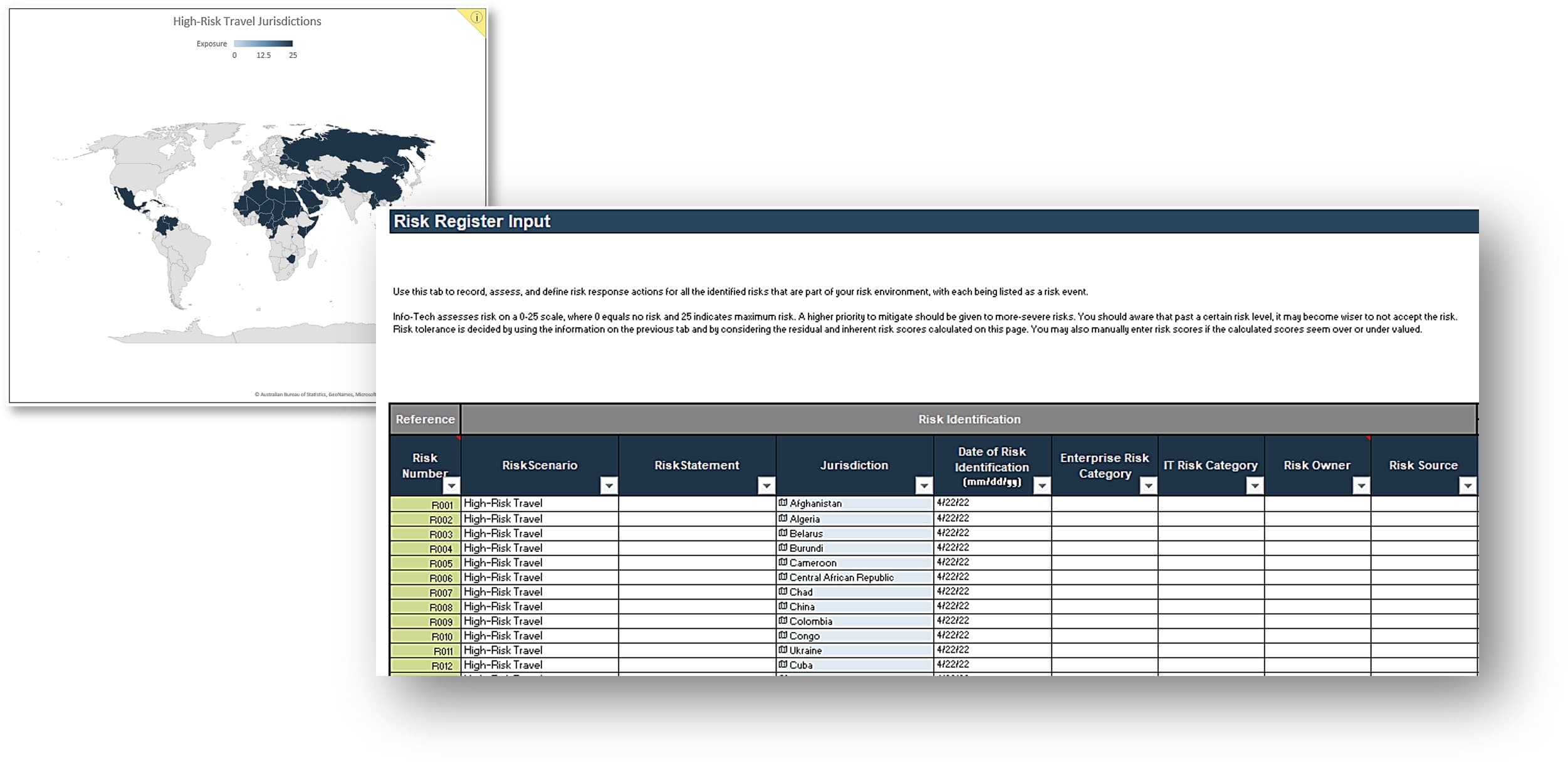
- Label the risk in Tab 3, Column B.
- Record your risk scenario in Tab 3, Column C.
- Record your risk statement in Tab 3, Column D.
- Identify the applicable jurisdictions in Tab 3, Column E.
- You can further categorize the scenario as:
- an enterprise risk (Column G).
- an IT risk (Column H).
Download the Jurisdictional Risk Register and Heatmap Tool
Step 2.2
Assess Risk Exposure
Activities
2.2.1 Identify existing controls
2.2.2 Assess likelihood and impact
This step involves the following participants:
- Security team
- Risk and Compliance
- IT leadership (optional)
Outcomes of this step
- Assess risk exposure for each risk scenario through an analysis of its likelihood and impact.
Brush up on risk assessment essentials
The next step will help you prioritize IT risks based on severity.
Likelihood of Occurrence X Likelihood of Impact = Risk Severity
Likelihood of occurrence: How likely the risk is to occur.
Likelihood of impact: The likely impact of a risk event.
Risk severity: The significance of the risk.
Evaluate risk severity against the risk tolerance thresholds and the cost of risk response.
Identify existing controls before you proceed
Existing controls will reduce the inherent likelihood and impact of the risk scenario you face.
Existing controls were put in place to avoid, mitigate, or transfer key risks your organization faced in the past. Without considering existing controls, you run the risk of overestimating the likelihood and impact of the risk scenarios your organization faces in high-risk jurisdictions.
For instance, the ability to remote-wipe corporate-owned devices will reduce the potential impact of a device lost or compromised during travel to high-risk jurisdictions.
As you complete the risk assessment for each scenario, document existing controls that reduce their inherent likelihood and impact.
2.2.1 Document existing controls
6-10 hours
- Document the Risk Category and Existing Controls in the Jurisdictional Risk Register and Heatmap Tool.
- Tactical controls apply to individual risks only. For instance, the ability to remote-wipe devices mitigates the impact of a device lost in a high-risk jurisdiction.
- Strategic controls apply to multiple risks. For instance, deploying MFA for critical applications mitigates the likelihood that malicious actors can compromise a lost device and impedes their access in devices they do compromise.
Input | Output |
|
|
Materials | Participants |
|
|
Download the Jurisdictional Risk Register and Heatmap Tool.
Assess the risk scenarios you identified in Phase 1
The risk register is the central repository for risks in high-risk jurisdictions.
- Use the second tab of the Jurisdictional Risk Register and Heatmap Tool to create likelihood, impact, and risk tolerance assessment scales to evaluate every risk event effectively.
- Severity-level assessment is a “first pass” of your risk scenarios that will reveal your organization’s most severe risks in high-risk jurisdictions.
- You can incorporate expected cost calculations into your evaluation to assess scenarios in greater detail.
- Expected cost represents how much you would expect to pay in an average year for each risk event. Expected cost calculations can help compare IT risks to non-IT risks that may not use the same scales and communicate system-level risk to the business in a language they will understand.
Expected cost calculations may not be practical. Determining robust likelihood and impact values to produce cost estimates can be challenging and time consuming. Use severity-level assessments as a first pass to make the case for risk mitigation measures and take your lead from stakeholders.
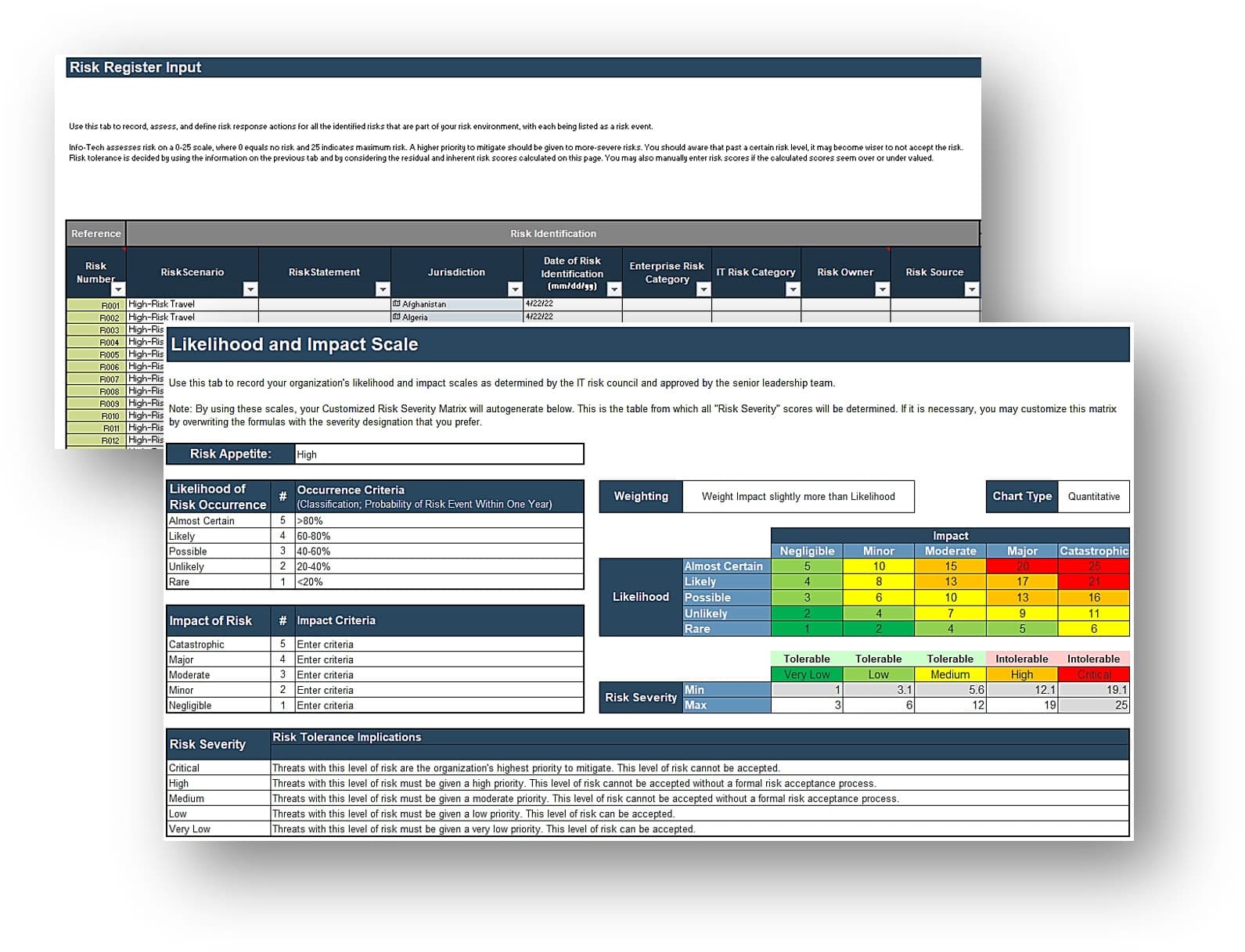
Use the Jurisdictional Risk Register and Heatmap Tool to capture and analyze your data.
2.2.2 Assess likelihood and impact
6-10 hours
- Assign each risk scenario a likelihood of occurrence and a likely impact level that represents the impact of the scenario on the whole organization considering existing controls. Record your results in Tab 3, column R and S, respectively.
- You can further dissect likelihood and impact into component parameters but focus first on total likelihood and impact to keep the task manageable.
- As you input the first few likelihood and impact values, compare them to one another to ensure consistency and accuracy. For instance, is a device lost in a high-risk jurisdiction truly more impactful than a device compromised with commercial surveillance software?
- The tool will calculate the probability of risk exposure based on the likelihood and consequence associated with the scenario. The results are published in Tab 3, Column T.
Input | Output |
|
|
Materials | Participants |
|
|
Download the Jurisdictional Risk Register and Heatmap Tool.
Refine your risk assessment to justify your estimates
Document the rationale behind each value and the level of consensus in group discussions.
Stakeholders will likely ask you to explain some of the numbers you assigned to likelihood and impact assessments. Pointing to an assessment methodology will give your estimates greater credibility.
- Assign one individual to take notes during the assessment exercise.
- Have them document the main rationale behind each value and the level of consensus.
The goal is to develop robust intersubjective estimates of the likelihood and impact of a risk scenario.
We assigned a 50% likelihood rating to a risk scenario. Were we correct?
Assess the truth of the following statements to test likelihood assessments. In this case, do these two statements seem true?
- The risk event will likely occur once in the next two years, all things being equal.
- In two nearly identical organizations, one out of two will experience the risk event this year.
Phase 3
Execute Response
This phase will walk you through the following activities:
- Prioritize and treat global risks to critical assets based on their value and exposure.
- Build an initiative roadmap that identifies and applies relevant controls to protect critical assets. Identify key risk indicators to monitor progress.
This phase involves the following participants:
- Security team
- Risk and Compliance
- IT leadership (optional)
Step 3.1
Treat Security Risks
Activities
3.1.1 Identify and assess risk response
This step involves the following participants:
- Security team
- Risk and Compliance
- IT leadership (optional)
Outcomes of this step
- Prioritize and treat global risks to critical assets based on their value and exposure.
Analyze and select risk responses
The next step will help you treat the risk scenarios you built in Phase 2.
Identify
Identify risk responses.
Predict
Predict the effectiveness of the risk response, if implemented, by estimating the residual likelihood and impact of the risk.
Calculate
The tool will calculate the residual severity of the risk after applying the risk response.
The first part of the phase outlines project activities. The second part elaborates on high-risk travel and compliance risk, the two key risk scenarios we are following throughout the project. Use the Jurisdictional Risk Register and Heatmap Tool to capture your work.
Analyze likelihood and impact to identify response
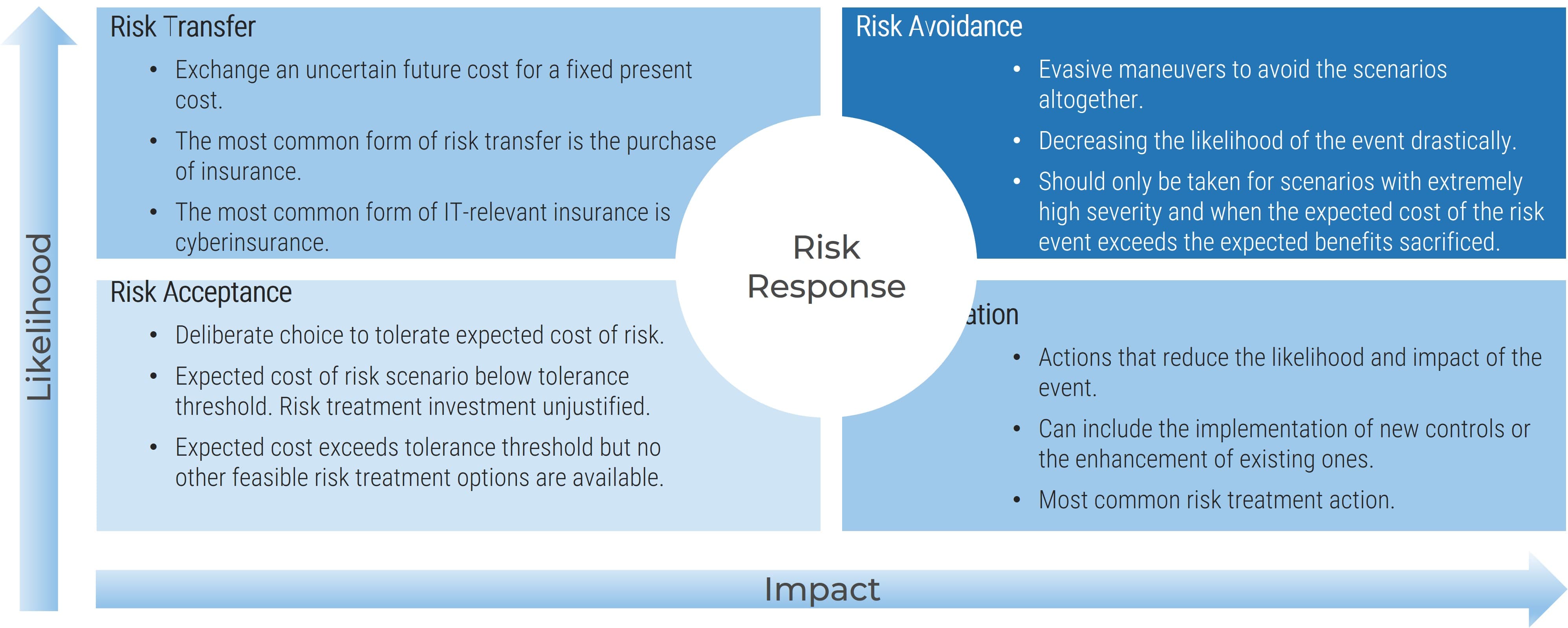
3.1.1 Identify and assess risk response
Complete the following steps for each risk scenario.
- Identify a risk response action that will help reduce the likelihood of occurrence or the impact if the scenario were to occur. Indicate the type of risk response (avoidance, mitigation, transfer, acceptance, or no risk exists).
- Assign each risk response action a residual likelihood level and a residual impact level. This is the same step you performed in Activity 2.2.2, but you are now are estimating the likelihood and impact of the risk event after you implemented the risk response action successfully. The Jurisdictional Risk Register and Heatmap Tool will generate a residual risk severity level for each risk event.
- Identify the potential Risk Action Owner (Project Manager) if the response is selected and turned into an IT project, and document this in the Jurisdictional Risk Register and Heatmap Tool .
- For each risk event, document risk response actions, residual likelihood and impact levels, and residual risk severity level.
Input | Output |
|
|
Materials | Participants |
|
|
Download the Jurisdictional Risk Register and Heatmap Tool
Step 3.2
Mitigate Travel Risk
Activities
3.2.1 Develop a travel policy
3.2.2 Develop travel procedures
3.2.3 Design high-risk travel guidelines
This step involves the following participants:
- Security team
- Risk and Compliance
- IT leadership (optional)
Outcomes of this step
- Prioritize and treat global risks to critical assets based on their value and exposure.
Identify controls to mitigate jurisdictional risk
This section provides guidance on the most prevalent risk scenarios identified in Phase 2 and provides a more in-depth examination of the two most prevalent ones, high-risk travel and compliance risk. Determine the appropriate response to each risk scenario to keep global risks to critical assets aligned with the organization’s risk tolerance.
Key Risk Scenarios
- High-Risk Travel
- Compliance Risk
- Insider Threat
- Advanced Persistent Threat
- Commercial Surveillance
Travel risk is a common concern in organizations with global operations
- The security of staff, devices, and data is one of the biggest challenges facing organizations with a global footprint. Working and traveling in unpredictable environments will aways carry a degree of risk, but organizations can do much to develop a safer and more secure working environment.
- Compromised or stolen devices can provide threat actors with access to data that could compromise the organization’s strategic, economic, or competitive advantage or expose the organization to regulatory risk.
- For many organizations, security risk assessments, security plans, travel security procedures, security training, and incident reporting systems are a key part of their operating language.
- The following section provides a simple structure to help organizations demystify travel in high-risk jurisdictions.
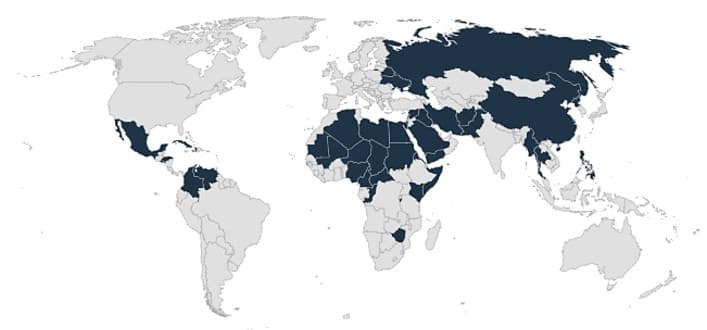
Before you leave
- Identify high-risk countries.
- Enable controls.
- Limit what you pack.
During your trip
- Assume you are monitored.
- Limit access to systems.
- Prevent theft.
When you return
- Change your password.
- Restore your devices.
Case study
Higher Education: Camosun College
Interview: Evan Garland
Frame additional security controls as a value-added service.
Situation
The director of the international department at Camosun College reached out to IT security for additional support. Department staff often traveled to hostile environments. They were concerned malicious agents would either steal end-user devices or compromise them and access sensitive data. The director asked IT security for options that would better protect traveling staff, their devices, and the information they contain.
Challenges
First, controls would need to admit both work and personal use of corporate devices. Staff relied exclusively on work devices for travel to mitigate the risk of personal device theft. Personal use of corporate devices during travel was common. Second, controls needed to strike the right balance between friction and effortless access. Traveling staff had only intermittent access to IT support. Restrictive controls could prevent them from accessing their devices and data altogether.
Solution
IT consulted staff to discuss light-touch solutions that would secure devices without introducing too much complexity or compromising functionality. They then planned security controls that involved user interaction and others that did not and identified training requirements.
Results
|
Controls with user interaction |
Controls without user interaction |
|
|
Build a program to mitigate travel risks
There is no one-size-fits-all solution.
The most effective solution will take advantage of existing risk management policies, processes, and procedures at your organization.
- Develop a framework. Outline the organization’s approach to high-risk travel, including the policies, procedures, and mechanisms put in place to ensure safe travel to high-risk jurisdictions.
- Draft a policy. Outline the organization’s risk attitude and key security principles and define roles and responsibilities. Include security responsibilities and obligations in job descriptions of staff members and senior managers.
- Provide flexible options. Inherent travel risk will vary from one jurisdiction to another. You will likely not find an approach that works for every case. Establish locally relevant measures and plans in different security contexts and risk environments.
- Look for quick wins. Identify measures or requirements that you can establish quickly but that can have a positive effect on the security of staff, data, and devices.
- Monitor and review. Undertake periodic reviews of the organization’s security approach and management framework, as well as their implementation, to ensure the framework remains effective.
3.2.1 Develop a travel policy
- Work with your business leaders to build a travel policy for high-risk jurisdictions. The policy should be a short and accessible document structured around four key sections:
- A statement on the importance of staff security and safety, the scope of the policy, and who it applies to (staff, consultants, contractors, volunteers, visitors, accompanying dependants, etc.).
- A principles section explaining the organization’s security culture, risk attitude, and the key principles that shape the organization’s approach to staff security and safety.
- A responsibilities section setting out the organization’s security risk management structure and the roles and actions allocated to specific positions.
- A minimal security requirements section establishing the specific security requirements that must be in place in all locations and specific locations.
- Common security principles include:
- Shared responsibility – Managing risks to staff is a shared organizational responsibility.
- Acknowledgment of risk – Managing security will not remove all risks. Staff need to appreciate, as part of their informed consent, that they are still exposed to risk.
- Primacy of life – Staff safety is of the highest importance. Staff should never place themselves at excessive risk to meet program objectives or protect property.
- Proportionate risk – Risks must be assessed to ensure they are proportionate to the benefits organizational activities provide and the ability to manage those risks.
- Right to withdraw – Staff have the right to withdraw from or refuse to take up work in a particular area due to security concerns.
- No right to remain – The organization has the right to suspend activities that it considers too dangerous.
Input | Output |
|
|
Materials | Participants |
|
|
Develop security plans for high-risk travel
Security plans advise staff on how to manage the risk identified in assessments.
Security plans are key country documents that outline the security measures and procedures in place and the responsibilities and resources required to implement them. Security plans should be established in high-risk jurisdictions where your organization has a regular, significant presence. Security plans must remain relevant and accessible documents that address the specific risks that exist in that location, and, if appropriate, are specific about where the measures apply and who they apply to. Plans should be updated regularly, especially following significant incidents or changes in the operating environment or activities.
Key Components
Critical information – One-page summary of pertinent information for easy access and quick reference (e.g. curfew times, no-go areas, important contacts).
Overview – Purpose and scope of the document, responsibilities for security plan, organization’s risk attitude, date of completion and review date, and a summary of the security strategy and policy.
Current Context – Summary of current operating context and overall security situation; main risks to staff, assets, and operations; and existing threats and risk rating.
Procedures – Simple security procedures that staff should adhere to in order to prevent incidents and how to respond should problems arise. Standard operating procedures (SOPs) should address key risks identified in the assessment.
Security levels – The organization's security levels/phases, with situational indicators that reflect increasing risks to staff in that context and location and specific actions/measures required in response to increasing insecurity.
Incident reporting – The procedures and responsibilities for reporting security-related incidents; for example, the type of incidents to be reported, the reporting structure, and the format for incident reporting.
Determine travel risk
Tailor your risk response to the security risk assessment you conducted in earlier stages of this project.
Ratings are formulated by assessing several types of risk, including conflict, political/civil unrest, terrorism, crime, and health and infrastructure risks.
Rating | Description (Examples) | Recommended Action |
Low | Generally secure with adequate physical security. Low violent crime rates. Some civil unrest during significant events. Acts of terrorism rare. Risks associated with natural disasters limited and health threats mainly preventable. | Basic personal security, travel, and health precautions required. |
Moderate | Periodic civil unrest. Antigovernment, insurgent, or extremist groups active with sporadic acts of terrorism. Staff at risk from common and violent crime. Transport and communications services are unreliable and safety records are poor. Jurisdiction prone to natural disasters or disease epidemics. | Increased vigilance and routine security procedures required. |
High | Regular periods of civil unrest, which may target foreigners. Antigovernment, insurgent, or extremist groups very active and threaten political or economic stability. Violent crime rates high and targeting of foreigners is common. Infrastructure and emergency services poor. May be regular disruption to transportation or communications services. Certain areas off-limits to foreigners. Jurisdictions experiencing a natural disaster or a disease epidemic are considered high risk. | High level of vigilance and effective, context-specific security precautions required. |
Extreme | Undergoing active conflict or persistent civil unrest. Risk of being caught up in a violent incident or attack is very high. Civil authorities may have lost control of significant portions of the country. Lines between criminality and political and insurgent violence are blurred. Foreigners are likely to be denied access to significant parts of the country. Transportation and communication services are severely degraded or non-existent. Violence presents a direct threat to staff security. | Stringent security precautions essential and may not be sufficient to prevent serious incidents. Program activities may be suspended and staff withdrawn at very short notice. |
3.2.2 Develop travel procedures
- Work with your business leaders to build travel procedures for high-risk jurisdictions. The procedures should be tailored to the risk assessment and address the risk scenarios identified in Phase 2.
- Use the categories outlined in the next two slides to structure the procedure. Address all types of travel, detail security measures, and outline what the organization expects of travelers before, during, and after their trip.
- Consider the implementation of special measures to limit the impact of a potential security event, including:
- Information end-user device loaner programs.
- Temporary travel service email accounts.
- Specify what happens when staff add personal travel to their work trip to cover issues such as insurance, check-in, actual travel times, etc.
- Discuss the rationale for each procedure. Ensure the components align with the policy statements outlined in the high-risk travel policy developed in the previous step.
Input | Output |
|
|
Materials | Participants |
|
|
Draft procedures to mitigate travel risks
Address all types of travel, detail security measures, and outline what the organization expects of travelers before, during, and after their trip
|
Introduction |
Clarifies who the procedures apply to. Highlights any differences in travel security requirements or support provided to staff, consultants, partners, and official visitors. |
|---|---|
|
Travel risk ratings |
Explains the travel or country risk rating system, how staff access the information, the different categories and indicators, and their implications. |
|
Roles and responsibilities |
Clarifies the responsibilities of travelers, their line managers or contact points, and senior management regarding travel security and how this changes for destinations with higher risk ratings. |
|
Travel authorization |
Stipulates who in the organization authorizes travel, the various compliance measures required, and how this changes for destinations with higher risk ratings. |
|
Travel risk assessment |
Explains when travel risk assessments are required, the template that should be used, and who approves the completed assessments. |
Travel security procedures should specify what happens when staff add personal travel to their work trip to cover issues such as insurance, check-in, actual travel times, etc.
|
Pre-travel briefings |
Outlines the information that must be provided to travelers prior to departure, the type of briefing required and who provides it, and how these requirements change as risk ratings increase. |
|---|---|
|
Security training |
Explain security training required prior to travel. This may vary depending on the country’s risk rating. Includes information on training waiver system, including justifications and authorization. |
|
Traveler profile forms |
Travelers should complete a profile form, which includes personal details, emergency contacts, medical details, social media footprint, and proof-of-life questions (in contexts where there are abduction risks). |
|
Check-in protocol |
Specifies who travelers must maintain contact with while traveling and how often, as well as the escalation process in case of loss of contact. The frequency of check-ins should reflect the increase in the risk rating for the destination. |
|
Emergency procedures |
Outlines the organization's emergency procedures for security and medical emergencies. |
3.2.3 Design high-risk travel guidelines
- Supplement the high-risk travel policies and procedures with guidelines to help international travelers stay safe.
- The document is intended for an end-user audience and should reflect your organization’s policies and procedures for the use of information and information systems during international travel.
- Use the Digital Safety Guidelines for International Travel template in concert with this blueprint to provide guidance on what end users can do to stay safe before they leave, during their trip, and when they return.
- Consider integrating the guidelines into specialized security awareness training sessions that target end users who travel to high-risk jurisdictions.
- The guidelines should supplement and align with existing technical controls.
Input | Output |
|
|
Materials | Participants |
|
|
Download the Digital Safety Guidelines for International Travel template
Step 3.3
Mitigate Compliance Risk
Activities
3.3.1 Identify data localization obligations
3.3.2 Integrate obligations into IT system design
3.3.3 Document data processing activities
3.3.4 Choose the right mechanism
3.3.5 Implement the appropriate controls
3.3.6 Identify data breach notification obligations
3.3.7 Integrate data breach notification into incident response
3.3.8 Identify vendor security and data protection requirements
3.3.9 Build due diligence questionnaire
3.3.10 Build appropriate data processing agreement
This step involves the following participants:
- Security team
- Risk and Compliance
- IT leadership (optional)
Outcomes of this step
- Prioritize and treat global risks to critical assets based on their value and exposure.
Compliance risk is a prevalent risk in organizations with a global footprint
- The legal and regulatory landscape is evolving rapidly to keep step with the pace of technological change. Security and privacy leaders are expected to mitigate the risk of noncompliance as the organization expands to new jurisdictions.
- Organizations with a global footprint must stay abreast of local regulations and provide risk management guidance to business leaders to support global operations.
- This sections describes four compliance risks in this context:
- Cross-border data transfer
- Third-party risk management
- Data breach notification
- Data residency
Compliance with local obligations
Likelihood: Medium to High
Impact: High
Data Residency
Gap Controls
- Identify and document the data localization obligations for the jurisdictions that the organization is operating in.
- Design and implement IT systems that satisfy the data localization requirements.
- Comply with data localization obligations within each jurisdiction.
Heatmap of Global Data Residency Regulations
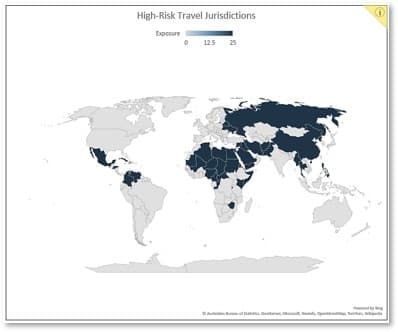
Source: InCountry, 2021
Examples of Data Residency Requirements
|
Country |
Data Type |
Local Storage Requirements |
|---|---|---|
|
Australia |
Personal data – heath record |
My Health Records Act 2012 |
|
China |
Personal information — critical information infrastructure operators |
Cybersecurity law |
|
Government cloud data |
Opinions of the Office of the Central Leading Group for Cyberspace Affairs on Strengthening Cybersecurity Administration of Cloud Computing Services for Communist Party and Government Agencies |
|
|
India |
Government email data |
The Public Records Act of 1993 |
|
Indonesia |
Data held by electronic system operator for the public service |
Regulation 82 concerning “Electronic System and Transaction Operation” |
|
Germany |
Government cloud service data |
Criteria for the procurement and use of cloud services by the federal German administration |
|
Russia |
Personal data |
The amendments of Data Protection Act No. 152 FZ |
|
Vietnam |
Data held by internet service providers |
The Decree on Management, Provision, and Use of Internet Services and Information Content Online (Decree 72) |
|
US |
Government cloud service data |
Defense Federal Acquisition Regulation Supplement: Network Penetration Reporting and Contracting for Cloud Services (DFARS Case 2013-D018) |
3.3.1 Identify data localization obligations
1-2 hours
- Work with your business leaders to identify and document the jurisdictions where your organization is operating in or providing services and products to consumers within.
- Work with your legal team to identify and document all relevant data localization obligations for the data your organization generates, collects, and processes in order to operate your business.
- Record your data localization obligations in the table below.
|
Jurisdiction |
Relevant Regulations |
Local Storage Requirements |
Date Type |
|---|---|---|---|
Input | Output |
|
|
Materials | Participants |
|
|
Download the Guidelines for Compliance With Local Security and Privacy Laws Template
3.3.2 Integrate obligations into your IT system design
1-2 hours
- Work with your IT department to design the IT architecture and systems to satisfy the data localization requirements.
- The table below provides a checklist for integrating privacy considerations into your IT systems.
|
Item |
Consideration |
Answer |
Supporting Document |
|---|---|---|---|
| 1 |
Have you identified business services that process data that will be subject to localization requirements? |
||
| 2 |
Have you identified IT systems associated with the business services mentioned above? |
||
| 3 |
Have you established a data inventory (i.e. data types, business purposes) for the IT systems mentioned above? |
||
| 4 |
Have you established a data flow diagram for the data identified above? |
||
| 5 |
Have you identified the types of data that should be stored locally? |
||
| 6 |
Have you confirmed whether a copy of the data locally stored will satisfy the obligations? |
||
| 7 |
Have you confirmed whether an IT redesign is needed or whether modifications (e.g. adding a server) to the IT systems would satisfy the obligations? |
||
| 8 |
Have you confirmed whether access from another jurisdiction is allowed? |
||
| 9 |
Have you identified how long the data should be stored? |
Input | Output |
|
|
Materials | Participants |
|
|
Download the Guidelines for Compliance With Local Security and Privacy Laws Template
Compliance with local obligations
Likelihood: Medium to High
Impact: High
Cross-Border Transfer
Gap Controls
- Know where you transfer your data.
- Identify jurisdictions that your organization is operating in and that impose different requirements for the cross-border transfer of personal data.
- Adopt and implement a proper cross-border data transfer mechanism in accordance with applicable privacy laws and regulations.
- Re-evaluate at appropriate intervals.
Which cross-border transfer mechanism should I choose?
|
Transfer Mechanism |
Advantages |
Disadvantages |
|---|---|---|
|
Standard Contractual Clauses (SCC) |
|
|
|
Binding Corporate Rules (BCRs) |
|
|
|
Code of Conduct |
|
|
|
Certification |
|
|
|
Consent |
|
|
3.3.3 Document data processing activities
1-2 hours
- Identify and document the following information:
- Name of business process
- Purposes of processing
- Lawful basis
- Categories of data subjects and personal data
- Data subject categories
- Which system the data resides in
- Recipient categories
- Third country/international organization
- Documents for appropriate safeguards for international transfer (adequacy, SCCs, BCRs, etc.)
- Description of mitigating measures
|
Input |
Output |
|
|
|
Materials |
Participants |
|
|
Download the Guidelines for Compliance With Local Security and Privacy Laws Template
3.3.4 Choose the right mechanism
1-2 hours
- Identify jurisdictions that your organization is operating in and that impose different requirements for the cross-border transfer of personal data. For example, the EU’s GDPR and China’s Personal Information Protection Law require proper cross-border transfer mechanisms before the data transfers. Your organization should decide which cross-border transfer mechanism is the best fit for your cross-border data transfer scenarios.
- Use the following table to identify and document the pros and cons of each data transfer mechanism and the final decision.
Data Transfer Mechanism | Pros | Cons | Final Decision |
|---|---|---|---|
SCC | |||
BCR | |||
Code of Conduct | |||
Certification | |||
Consent |
Input | Output |
|
|
Materials | Participants |
|
|
Download the Guidelines for Compliance With Local Security and Privacy Laws Template
3.3.5 Implement the appropriate controls
1-3 hours
- One of the most common mechanisms is standard contractual clauses (SCCs).
- Use Info-Tech’s Standard Contractual Clauses Template to facilitate your cross-border transfer activities.
- Identify and check whether the following core components are covered in your SCC and record the results in the table below.
| # | Core Components | Status | Note |
|---|---|---|---|
| 1 | Purpose and scope | ||
| 2 | Effect and invariability of the Clauses | ||
| 3 | Description of the transfer(s) | ||
| 4 | Data protection safeguards | ||
| 5 | Purpose limitation | ||
| 6 | Transparency | ||
| 7 | Accuracy and data minimization | ||
| 8 | Duration of processing and erasure or return of data | ||
| 9 | Storage limitation | ||
| 10 | Security of processing | ||
| 11 | Sensitive data | ||
| 12 | Onward transfers | ||
| 13 | Processing under the authority of the data importer | ||
| 14 | Documentation and compliance | ||
| 15 | Use of subprocessors | ||
| 16 | Data subject rights | ||
| 17 | Redress | ||
| 18 | Liability | ||
| 19 | Local laws and practices affecting compliance with the Clauses | ||
| 20 | Noncompliance with the Clauses and termination | ||
| 21 | Description of data processing activities, such as list of parties, description of transfer, etc. | ||
| 22 | Technical and organizational measures |
| Input | Output |
|
|
| Materials | Participants |
|
|
Download the Guidelines for Compliance With Local Security and Privacy Laws Template
Compliance with local obligations
Likelihood: High
Impact: Medium to High
Data Breach
Gap Controls
- Identify jurisdictions that your organization is operating in and that impose different obligations for data breach reporting.
- Document the notification obligations for various business scenarios, such as controller to DPA, controller to data subject, and processor to controller.
- Integrate breach notification obligations into security incident response process.
Examples of Data Breach Notification Obligations
|
Location |
Regulation/ Standard |
Reporting Obligation |
|---|---|---|
|
EU |
GDPR |
72 hours |
|
China |
PIPL |
Immediately |
|
US |
HIPAA |
No later than 60 days |
|
Canada |
PIPEDA |
As soon as feasible |
|
Global |
PCI DSS |
|
Summary of US State Data Breach Notification Statutes
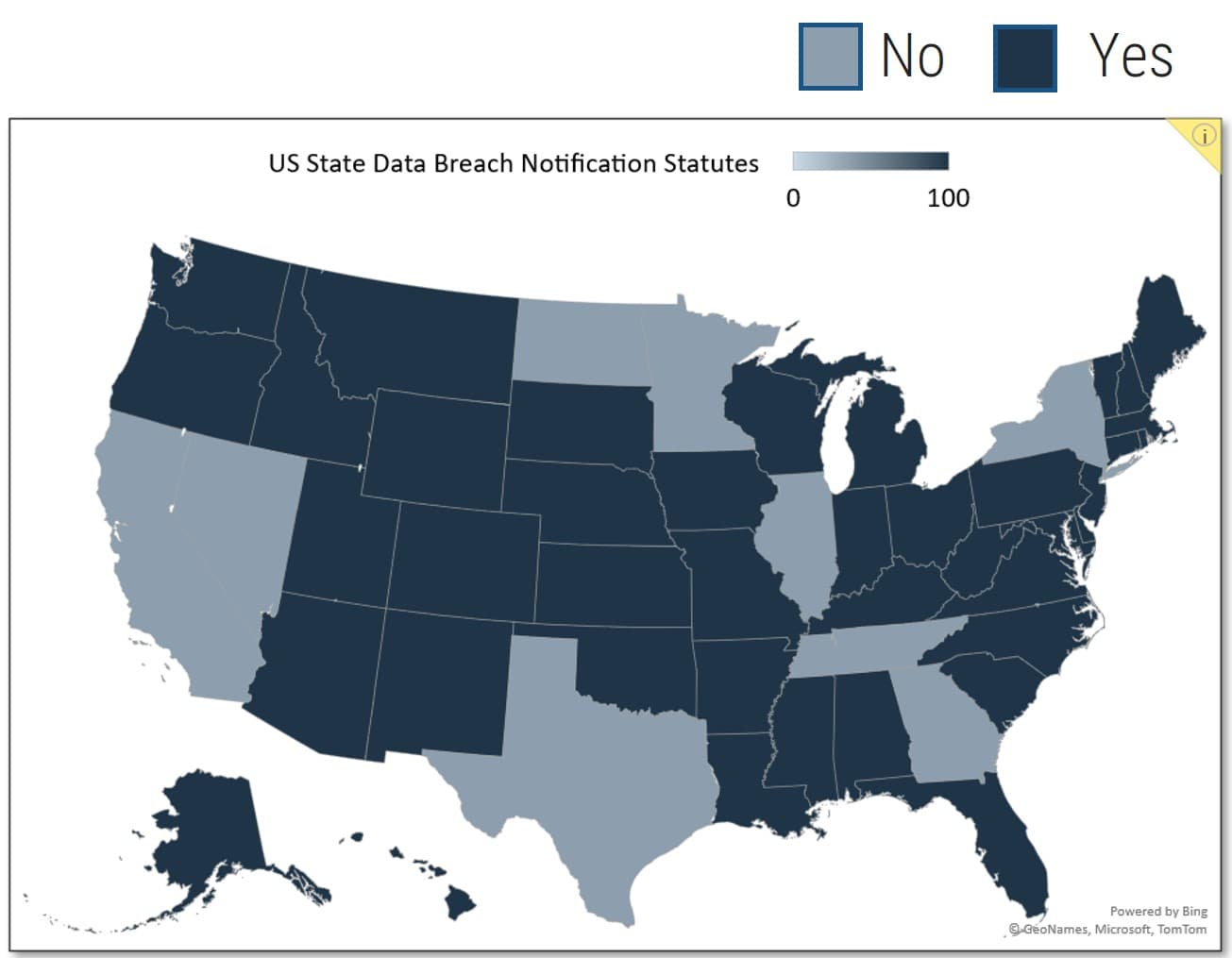
Source: Davis Wright Tremaine
3.3.6 Identify data breach notification obligations
1-2 hours
- Identify jurisdictions that your organization is operating in and that impose different obligations for data breach reporting.
- Document the notification obligations for various business scenarios, such as controller to DPA, controller to data subject, and processor to controller.
- Record your data breach obligations in the table below.
| Region | Regulation/Standard | Reporting Obligation |
|---|---|---|
Input | Output |
|
|
Materials | Participants |
|
|
Download the Guidelines for Compliance With Local Security and Privacy Laws Template
3.3.7 Integrate data breach notification into incident response
1-2 hours
- Integrate breach notification obligations into the security incident response process. Understand the security incident management framework.
- All incident runbooks follow the same process: detection, analysis, containment, eradication, recovery, and post-incident activity.
- The table below provides a basic checklist for you to consider when implementing your data breach and incident handling process.
| # | Phase | Considerations | Status | Notes |
|---|---|---|---|---|
| 1 | Prepare | Ensure the appropriate resources are available to best handle an incident. | ||
| 2 | Detect | Leverage monitoring controls to actively detect threats. | ||
| 3 | Analyze | Distill real events from false positives. | ||
| 4 | Contain | Isolate the threat before it can cause additional damage. | ||
| 5 | Eradicate | Eliminate the threat from your operating environment. | ||
| 6 | Recover | Restore impacted systems to a normal state of operations. | ||
| 7 | Report | Report data breaches to relevant regulators and data subjects if required. | ||
| 8 | Post-Incident Activities | Conduct a lessons-learned post-mortem analysis. |
| Input | Output |
|
|
| Materials | Participants |
|
|
Download the Guidelines for Compliance With Local Security and Privacy Laws Template
Compliance with local obligations
Likelihood: High
Impact: Medium to High
Third-Party Risk
Gap Controls
- Build an end-to-end third-party security and privacy risk management process.
- Perform internal due diligence prior to selecting a service provider.
- Stipulate the security and privacy protection obligations of the third party in a legally binding document such as contract or data processing agreement, etc.
End-to-End Third-Party Security and Privacy Risk Management
- Pre-Contract
- Due diligence check
- Data processing agreement
- Continuous monitoring
- Regular check or audit
- Data deletion
- Access deprovisioning
Examples of Vendor Security Management Requirements
|
Region |
Law/Standard |
Section |
|---|---|---|
|
EU |
General Data Protection Regulation (GDPR) |
Article 28 (1) |
|
Article 46 (1) |
||
| US |
Health Insurance Portability and Accountability Act (HIPAA) |
§164.308(b)(1) |
| US |
New York Department of Financial Services Cybersecurity Requirements |
500.11(a) |
|
Global |
ISO 27002:2013 |
15.1.1 |
|
15.1.2 |
||
|
15.1.3 |
||
|
15.2.1 |
||
|
15.2.2 |
||
| US |
NIST 800-53 |
SA-12 |
|
SA-12 (2) |
||
| US |
NIST Cybersecurity Framework |
ID-SC-1 |
|
ID-SC-2 |
||
|
ID-SC-3 |
||
|
ID-SC-4 |
||
| Canada |
OSFI Cybersecurity Guidelines |
4.25 |
|
4.26 |
3.3.8 Identify vendor security and data protection requirements
1-2 hours
- Effective vendor security risk management is an end-to-end process that includes assessment, risk mitigation, and periodic reassessments.
- An efficient and effective assessment process can only be achieved when all stakeholders are participating.
- Identify and document your vendor security and data protection requirements in the table below.
| Region | Law/Standard | Section | Requirements |
|---|---|---|---|
Input | Output |
|
|
Materials | Participants |
|
|
Download the Guidelines for Compliance With Local Security and Privacy Laws Template
3.3.9 Build due diligence questionnaire
1-2 hours
Perform internal due diligence prior to selecting a service provider.
- Build and right-size your vendor security questionnaire by leveraging Info-Tech’s Vendor Security Questionnaire template.
- Document your vendor security questionnaire in the table below.
| # | Question | Vendor Request | Vendor Comments |
|---|---|---|---|
| 1 | Document Requests | ||
| 2 | Asset Management | ||
| 3 | Governance | ||
| 4 | Supply Chain Risk Management | ||
| 5 | Identify Management, Authentication, and Access Control |
| Input | Output |
|
|
| Materials | Participants |
|
|
Download the Guidelines for Compliance With Local Security and Privacy Laws Template
3.3.10 Build appropriate data processing agreement
1-2 hours
- Stipulate the security and privacy protection obligations of the third party in a legally binding document such as contract or data processing agreement, etc.
- Leverage Info-Tech’s Data Processing Agreement Template to put the language into your legally binding document.
- Use the table below to check whether core components of a typical DPA are covered in your document.
| # | Core Components | Status | Note |
|---|---|---|---|
| 1 | Processing of personal data | ||
| 2 | Scope of application and responsibilities | ||
| 3 | Processor's obligations | ||
| 4 |
Controller's obligations |
||
| 5 | Data subject requests | ||
| 6 | Right to audit and inspection | ||
| 7 | Subprocessing | ||
| 8 | Data breach management | ||
| 9 | Security controls | ||
| 10 | Transfer of personal data | ||
| 11 | Duty of confidentiality | ||
| 12 | Compliance with applicable laws | ||
| 13 | Service termination | ||
| 14 | Liability and damages |
| Input | Output |
|
|
| Materials | Participants |
|
|
Download the Guidelines for Compliance With Local Security and Privacy Laws Template
Summary of Accomplishment
Problem Solved
By following Info-Tech’s methodology for securing global operations, you have:
- Evaluated the security context of your organization’s global operations.
- Identified security risks scenarios unique to high-risk jurisdictions and assessed the exposure of critical assets.
- Planned and executed a response.
You have gone through a deeper analysis of two key risk scenarios that affect global operations:
- Travel to high-risk jurisdictions.
- Compliance risk.
If you would like additional support, have our analysts guide you through an Info-Tech workshop or Guided Implementation.
Contact your account representative for more information.
workshop@infotech.com1-888-670-8889
Additional Support
If you would like additional support, have our analysts guide you through other phases as part of an Info-Tech Workshop.
Contact your account representative for more information.
workshops@infotech.com 1-888-670-8889
To accelerate this project, engage your IT team in an Info-Tech workshop with an Info-Tech analyst team. Info-Tech analysts will join you and your team at your location or welcome you to Info-Tech’s historic Toronto office to participate in an innovative onsite workshop.
The following are sample activities that will be conducted by Info-Tech analysts with your team:
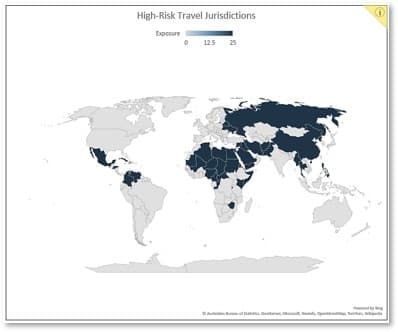
Identify High-Risk Jurisdictions
Develop requirements to identify high-risk jurisdictions.
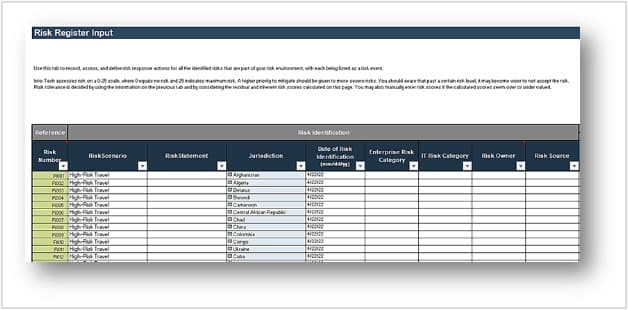
Build Risk Scenarios
Build risk scenarios to capture assets, vulnerabilities, threats, and the potential effect of a compromise.
External Research Contributors
Ken Muir
CISO
LMC Security
Premchand Kurup
CEO
Paramount Computer Systems
Preeti Dhawan
Manager, Security Governance
Payments Canada
Scott Wiggins
Information Risk and Governance
CDPHP
Fritz Y. Jean Louis
CISO
Globe and Mail
Eric Gervais
CIO
Ovivo Water
David Morrish
CEO
MBS Techservices
Evan Garland
Manager, IT Security
Camosun College
Jacopo Fumagalli
CISO
Axpo
Dennis Leon
Governance and Security Manager
CPA Canada
Tero Lehtinen
CIO
Planmeca Oy
Related Info-Tech Research
Build an IT Risk Management Program
- Build a program to identify, evaluate, assess, and treat IT risks.
- Monitor and communicate risks effectively to support business decision making.
Combine Security Risk Management Components Into One Program
- Develop a program focused on assessing and managing information system risks.
- Build a governance structure that integrates security risks within the organization’s broader approach to risk management.
Build an Information Security Strategy
- Build a holistic, risk-aware strategy that aligns to business goals.
- Develop a roadmap of prioritized initiatives to implement the strategy over 18 to 36 months.
Bibliography
2022 Cost of Insider Threats Global Report.” Ponemon Institute, NOVIPRO, 9 Feb. 2022. Accessed 25 May 22.
“Allianz Risk Barometer 2022.” Allianz Global Corporate & Specialty, Jan. 2022. Accessed 25 May 22.
Bickley, Shaun. “Security Risk Management: a basic guide for smaller NGOs”. European Interagency Security Forum (EISF), 2017. Web.
“Biden Administration Warns against spyware targeting dissidents.” New York Times, 7 Jan 22. Accessed 20 Jan 2022.
Boehm, Jim, et al. “The risk-based approach to cybersecurity.” McKinsey & Company, October 2019. Web.
“Cost of a Data Breach Report 2021.” IBM Security, July 2021. Web.
“Cyber Risk in Asia-Pacific: The Case for Greater Transparency.” Marsh & McLennan Companies, 2017. Web.
“Cyber Risk Index.” NordVPN, 2020. Accessed 25 May 22
Dawson, Maurice. “Applying a holistic cybersecurity framework for global IT organizations.” Business Information Review, vol. 35, no. 2, 2018, pp. 60-67.
“Framework for improving critical infrastructure cybersecurity.” National Institute of Standards and Technology, 16 Apr 2018. Web.
“Global Cybersecurity Index 2020.” International Telecommunication Union (ITU), 2021. Accessed 25 May 22.
“Global Risk Survey 2022.” Control Risks, 2022. Accessed 25 May 22.
“International Travel Guidance for Government Mobile Devices.” Federal Mobility Group (FMG), Aug. 2021. Accessed 18 Nov 2021.
Kaffenberger, Lincoln, and Emanuel Kopp. “Cyber Risk Scenarios, the Financial System, and Systemic Risk Assessment.” Carnegie Endowment for International Peace, September 2019. Accessed 11 Jan 2022.
Koehler, Thomas R. Understanding Cyber Risk. Routledge, 2018.
Owens, Brian. “Cybersecurity for the travelling scientist.” Nature, vol. 548, 3 Aug 2017. Accessed 19 Jan. 2022.
Parsons, Fintan J., et al. “Cybersecurity risks and recommendations for international travellers.” Journal of Travel Medicine, vol. 1, no. 4, 2021. Accessed 19 Jan 2022.
Quinn, Stephen, et al. “Identifying and estimating cybersecurity risk for enterprise risk management.” National Institute of Standards and Technology (NIST), Interagency or Internal Report (IR) 8286A, Nov. 2021.
Quinn, Stephen, et al. “Prioritizing cybersecurity risk for enterprise risk management.” NIST, IR 8286B, Sept. 2021.
“Remaining cyber safe while travelling security recommendations.” Government of Canada, 27 April 2022. Accessed 31 Jan 2022.
Stine, Kevin, et al. “Integrating cybersecurity and enterprise risk management.” NIST, IR 8286, Oct. 2020.
Tammineedi, Rama. “Integrating KRIs and KPIs for effective technology risk management.” ISACA Journal, vol. 4, 1 July 2018.
Tikk, Eneken, and Mika Kerttunen, editors. Routledge Handbook of International Cybersecurity. Routledge, 2020.
Voo, Julia, et al. “National Cyber Power Index 2020.” Belfer Center for Science and International Affairs, Harvard Kennedy School, Sept. 2020. Web.
Zhang, Fang. “Navigating cybersecurity risks in international trade.” Harvard Business Review, Dec 2021. Accessed 31 Jan 22.
Appendix
Insider Threat
Key Risk Scenario
Likelihood: Medium to High
Impact: High
Gap Controls
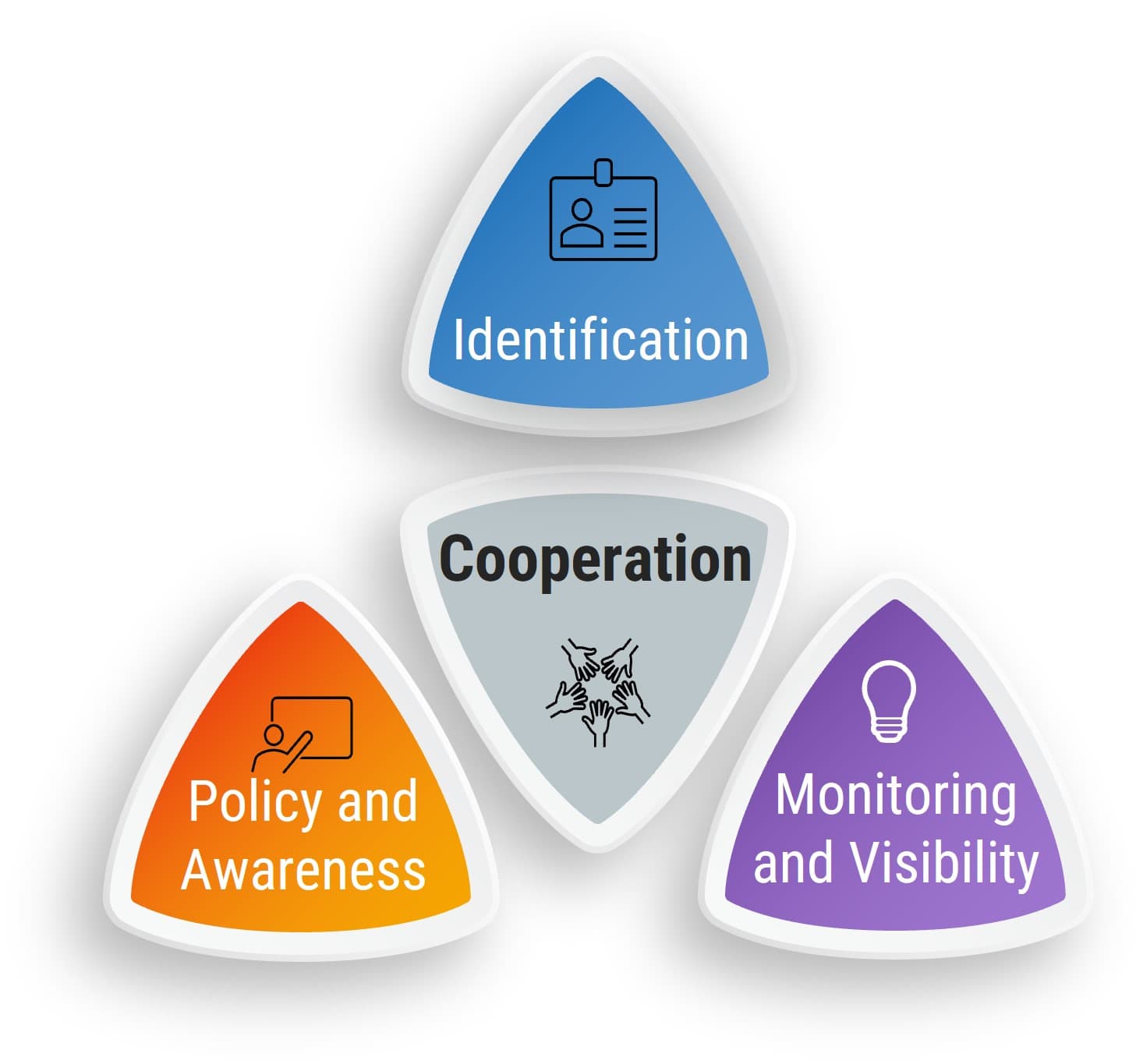
- Identification: Effective and efficient management of insider threats begins with a threat and risk assessment to establish which assets and which employees to consider, especially in jurisdictions associated with sensitive or critical data. You need to pay extra attention to employees who are working in satellite offices in jurisdictions with loose security and privacy laws.
- Monitoring and Visibility: Organizations should monitor critical assets and groups with privileged access to defend against malicious behavior. Implement an insider threat management platform that provides your organization with the visibility and context into data movement, especially cross-border transfers that might cause security and privacy breaches.
- Policy and Awareness Training: Insider threats will persist without appropriate action and culture change. Training and consistent communication of best practices will mitigate vulnerabilities to accidental or negligent attacks. Customized training materials using local languages and role-based case studies might be needed for employees in high-risk jurisdictions.
- Cooperation: An effective insider threat management program should be built with cross-team functions such as Security, IT, Compliance and Legal, etc.
For more holistic approach, you can leverage our Reduce and Manage Your Organization’s Insider Threat Risk blueprint.
Info-Tech Insight
You can’t just throw tools at a human problem. While organizations should monitor critical assets and groups with privileged access to defend against malicious behavior, good management and supervision can help detect attacks and prevent them from happening in the first place.
Insider threats are not industry specific, but malicious insiders are
Industry | Actors | Risks | Tactics | Motives |
|---|---|---|---|---|
State and Local Government |
|
|
|
|
Information Technology |
|
|
|
|
Healthcare |
|
|
|
|
Finance and Insurance |
|
|
|
|
Source: Carnegie Mellon University Software Engineering Institute, 2019
Advanced Persistent Threat
Key Risk Scenario #4
Likelihood: Medium to High
Impact: High
Gap Controls
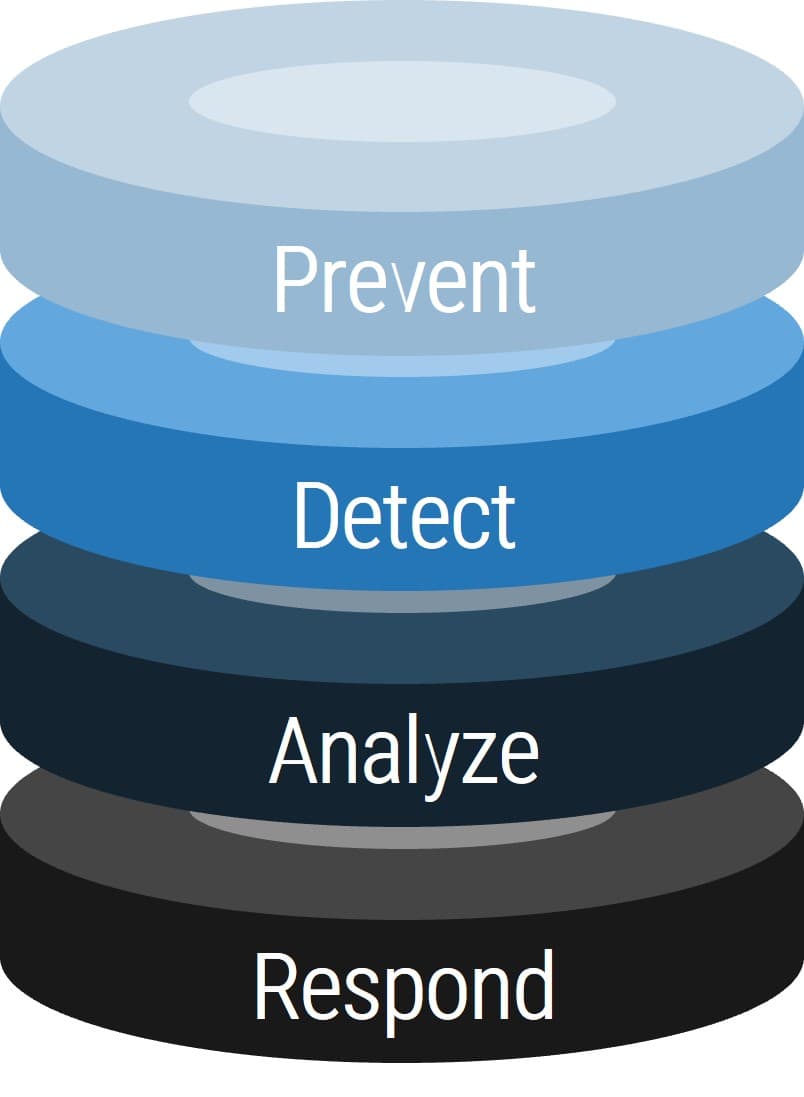
Prevent: Defense in depth is the best approach to protect against unknown and unpredictable attacks. Effective anti-malware, diligent patching and vulnerability management, and strong human-centric security are essential.
Detect: There are two types of companies – those who have been breached and know it, and those who have been breached and don’t know it. Ensure that monitoring, logging, and event detection tools are in place and appropriate to your organizational needs.
Analyze: Raw data without interpretation cannot improve security and is a waste of time, money, and effort. Establish a tiered operational process that not only enriches data but also provides visibility into your threat landscape.
Respond: Organizations can’t rely on ad hoc response anymore – don’t wait until a state of panic. Formalize your response processes in a detailed incident runbook to reduce incident remediation time and effort.
Best practices moving forward
Defense in Depth
Lock down your organization. Among other tactics, control administrative privileges, leverage threat intelligence, use IP whitelisting, adopt endpoint protection and two-factor authentication, and formalize incident response measures.
Block Indicators
Information alone is not actionable. A successful threat intelligence program contextualizes threat data, aligns intelligence with business objectives, and then builds processes to satisfy those objectives. Actively block indicators and act upon gathered intelligence.
Drive Adoption
Create organizational situational awareness around security initiatives to drive adoption of foundational security measures: network hardening, threat intelligence, red-teaming exercises, and zero-day mitigation, policies, and procedures.
Supply Chain Security
Security extends beyond your organization. Ensure your organization has a comprehensive view of your organizational threat landscape and a clear understanding of the security posture of any managed service providers in your supply chain.
Awareness and Training
Conduct security awareness and training. Teach end users how to recognize current cyberattacks before they fall victim – this is a mandatory first line of defense.
Additional Resources
Follow only official sources of information to help you assess risk
As misinformation is a major attack vector for malicious actors, follow only reliable sources for cyberalerts and actionable intelligence. Aggregate information from these reliable sources.
Federal Cyber Agency Alerts
- CISA (US Cybersecurity & Infrastructure Security Agency) Alerts
- Canadian Centre for Cyber Security – Cyber threat bulletin: Cyber Centre reminds Canadian critical infrastructure operators to raise awareness and take mitigations against known Russian-backed cyber threat activity
- Australia Cyber Security Centre – 2022-02: Australian organisations should urgently adopt an enhanced cyber security posture
Informational Resources
- CISA Known Exploited Vulnerabilities Catalog
- SANS Internet Storm Center
- CISA Shields Up
- Computer Emergency Response Team of Ukraine (in Ukrainian)
- Understanding and Mitigating Russian State-Sponsored Cyber Threats to U.S. Critical Infrastructure
Info-Tech Insight
The CISA Shields Up site provides the latest cyber risk updates on the Russia-Ukraine conflict and should provide the most value in staying informed.
Buying Options
Secure Operations in High-Risk Jurisdictions
IT Risk Management · IT Leadership & Strategy implementation · Operational Management · Service Delivery · Organizational Management · Process Improvements · ITIL, CORM, Agile · Cost Control · Business Process Analysis · Technology Development · Project Implementation · International Coordination · In & Outsourcing · Customer Care · Multilingual: Dutch, English, French, German, Japanese · Entrepreneur
Tymans Group is a brand by Gert Taeymans BV
Gert Taeymans bv
Europe: Koning Albertstraat 136, 2070 Burcht, Belgium — VAT No: BE0685.974.694 — phone: +32 (0) 468.142.754
USA: 4023 KENNETT PIKE, SUITE 751, GREENVILLE, DE 19807 — Phone: 1-917-473-8669
Copyright 2017-2022 Gert Taeymans BV