Modernize and Transform Your End-User Computing Strategy
IT needs to answer these questions:
- What types of computing devices, provisioning models, and operating systems should be offered to end users?
- How will IT support devices?
- What are the policies and governance surrounding how devices are used?
- What actions are we taking and when?
- How do end-user devices support larger corporate priorities and strategies?
Your answers need to balance choice, risk, and cost.
Our Advice
Critical Insight
- Even if a user has a prestigious tablet, if the apps aren’t built well, they can’t get support on it, or they can’t connect, then that device is useless. Focus on supportability, use cases, connection, and policy – and the device.
Impact and Result
- Identify desired benefits that align to IT and corporate priorities and strategies.
- Perform a persona analysis.
- Define a vision for end-user computing.
- Define the standard device and app offerings.
- Improve the supporting services surrounding devices.
- Develop a roadmap for implementing your strategy.
Modernize and Transform Your End-User Computing Strategy Research & Tools
Besides the small introduction, subscribers and consulting clients within this management domain have access to:
1. End-User Computing Strategy Deck – A step-by-step document to walk you through end-user computing trends and processes to improve customer satisfaction.
This storyboard will help you identify your goals, build standard offerings for users, define governance and policies around offerings, and develop a roadmap for your EUC program.
- Modernize and Transform Your End-User Computing Strategy – Phases 1-3
2. End-User Computing Strategy Template – A repository for your current-state and persona analysis to identify technology requirements for each user group.
Use these templates to document your end-user computing strategy. Follow the guidelines in the blueprint and record activity results in the template. The findings will be presented to the management team.
- End-User Computing Strategy Template
- User Group Analysis Workbook
3. End-User Computing Ideas Catalog and Standard Offering Guide – Templates that guide you to document the outcome from persona analysis to define standard offerings and policies.
The Ideas Catalog introduces provisioning models, form factors, and supported operating systems. Use the Standard Offering Template to document provisioning models and define computing devices along with apps and peripherals according to the outcome of the user group analysis.
- Standard End-User Entitlements and Offerings Template
- End-User Computing Ideas Catalog
4. End-User Computing Policies – Policies that establish requirements for end-user computing.
Use these policy templates to communicate the purposes behind each end-user computing decision and establish company standards, guidelines, and procedures for the purchase of technologies. The policies will ensure purchasing, reimbursement, security, and remote wiping enforcements are consistent and in alignment with the company strategy.
- Mobile Device Connectivity & Allowance Policy
- Purchasing Policy
- Mobile Device Reimbursement Agreement
- Mobile Device Reimbursement Policy
- BYOD Acceptable Use Policy
- Mobile Device Remote Wipe Waiver Template
- General Security – User Acceptable Use Policy
- Device Entitlement Policy Template
Infographic
Workshop: Modernize and Transform Your End-User Computing Strategy
Workshops offer an easy way to accelerate your project. If you are unable to do the project yourself, and a Guided Implementation isn't enough, we offer low-cost delivery of our project workshops. We take you through every phase of your project and ensure that you have a roadmap in place to complete your project successfully.
1 Set the Direction
The Purpose
Dig into the current state and build user persona.
Key Benefits Achieved
Determine your challenges and strengths.
Delineate user IT requirements.
Activities
1.1 Assess the current state of end-user computing.
1.2 Perform SWOT analysis.
1.3 Map benefits to stakeholder drivers and priorities.
1.4 Identify user groups.
1.5 Identify supporting technology.
1.6 Identify opportunities to provide value.
Outputs
SWOT analysis of current state
Goals cascade
Persona analysis
2 Define the Offering
The Purpose
Define your EUC vision and standard offerings.
Key Benefits Achieved
Brainstorm EUC vision and mission.
Find out the standard offerings.
Set the direction for end-user computing to support shift-left enablement.
Activities
2.1 Prioritize benefits.
2.2 Craft a vision and mission statement.
2.3 Identify goals.
2.4 Define guiding principles for your strategy.
2.5 Select a provisioning model for each persona.
2.6 Define the standard device offerings.
2.7 Document each persona's entitlements.
Outputs
Vision statement, mission statement, and guiding principles
Goals and indicators
End-user device entitlements standard
3 Support the Offering
The Purpose
Outline supporting practices and define policies for each use case.
Key Benefits Achieved
Document supporting practices.
Document EUC policies.
Activities
3.1 Define device management tools and approach.
3.2 Identify groups involved in supporting practices.
3.3 Identify opportunities to improve customer service.
3.4 Define acceptable use.
3.5 Define BYOD policies.
3.6 Define procurement and entitlement policies.
3.7 Define security policies.
Outputs
List of management tools for end-user computing
Roles and responsibilities for maintaining the end-user computing environment
Opportunities to improve customer service
End-user computing policy templates
4 Bridge the Gap and Create the Roadmap
The Purpose
Build a user migration roadmap.
Key Benefits Achieved
Make the project a reality by documenting initiatives and building a roadmap.
Activities
4.1 Identify the gaps in devices, user support, use cases, policy & governance, and fitness for use.
4.2 Plan the deployment and user migration journey.
4.3 Document initiatives in the roadmap.
Outputs
Initiatives mapped to practice areas
User migration journey map
Further reading
Modernize and Transform Your End-User Computing Strategy
Support the workforce of the future.
EXECUTIVE BRIEF
Analyst Perspective
Focus beyond the device
It’s easy to think that if we give end users nice devices, then they will be more engaged and they will be happy with IT. If only it were that easy.
Info-Tech Research Group has surveyed over 119,000 people through its CIO Business Vision diagnostic. The results show that a good device is necessary but not enough for high satisfaction with IT. Once a user has a decent device, the other aspects of the user’s experience has a higher impact on their satisfaction with IT.
After all, if a person is trying to run apps designed in the 1990s, if they are struggling to access resources through an underperforming VPN connection, or if they can’t get help when their devices and apps aren’t working, then it doesn’t matter that you gave them a state-of-the-art MacBook or Microsoft Surface.
As you build out your end-user computing strategy to reflect the new reality of today’s workforce, ensure you focus on shifting user support left, modernizing apps to support how users need to work, and ensuring that your network and collaboration tools can support the increased demands. End-user computing teams need to focus beyond the device.
Ken Weston, ITIL MP, PMP, Cert.APM, SMC
Research Director, Infrastructure and Operations Info-Tech Research Group
Mahmoud Ramin, PhD
Senior Research Analyst, Infrastructure and Operations Info-Tech Research Group
Executive Summary
Your Challenge
IT needs to answer these questions:
- What types of computing devices, provisioning models, and operating systems (OSes) should be offered to end users?
- How will IT support devices?
- What are the policies and governance surrounding how devices are used?
- What actions are we taking and when?
- How do end-user devices support larger corporate priorities and strategies?
Your answers need to balance choice, risk, and cost.
Common Obstacles
Management paradigms have shifted:
- OSes, device management, and IT asset management (ITAM) practices have changed.
- Users expect full capabilities on any personal device.
- Virtual desktops are switching to the cloud.
- Low-code/no-code platforms allow the business to manage their own apps or comanage with IT.
- Work-from-anywhere is the default.
- Users have higher customer service expectations.
Take end-user computing beyond the OS.
Info-Tech's Approach
This blueprint will help you:
- Identify desired benefits that align to IT and corporate priorities and strategies.
- Perform a persona analysis.
- Define a vision for end-user computing.
- Define the standard device and app offerings.
- Improve the supporting services surrounding devices.
- Develop a roadmap for implementing your strategy.
A good device is necessary for satisfaction with IT but it’s not enough.
If a user has a prestigious tablet but the apps aren’t built well, they can’t get support on it, or they can’t connect to the internet, then that device is useless. Focus on supportability, use cases, connection, policy – and device.
Your challenge
This blueprint will help you build a strategy that answers these questions:
- What types of computing devices should be offered to end users?
- What provisioning models will be used?
- What operating systems are supported?
- How will IT support devices?
- What are the policies and governance surrounding how devices are used?
- What actions are we taking and when?
- How do end-user devices support larger corporate priorities and strategies?
Definition: End-User Computing (EUC)
End-user computing (EUC) is the domain of information and technology that deals with the devices used by workers to do their jobs. EUC has five focus areas: devices, user support, use cases, policy & governance, and fitness for use.
A good end-user computing strategy will effectively balance:
User Choice
Cost
Risk
The right balance will be unique for every organization.
Strike the right balance
The discussion is larger than desktop support
If IT is an influencer, then you get to drive this conversation. If IT is not an influencer, then you need to support whatever option the business wants.
| Cost | Risk | Choice | Result | |
|---|---|---|---|---|
| Higher Education | High importance | Low importance | High importance | Full BYOD for professors. Standardized offerings for administration. |
| Software Development Firms | Low importance | Medium/High importance | High importance | Standardized offerings for developers. Virtual desktops for users on BYOD. |
| Legal Firm | Medium importance | High importance | Low importance | Partners offered prestigious devices. Everyone else uses Windows PCs. Virtual desktops and apps for remote access. |
|
Healthcare |
High importance | High importance | Low importance | Nurses, janitors, and other frontline staff use shared tablets. Doctors are provisioned their own tablet. Admin staff and doctors are provisioned virtual desktops to maintain security and compliance. |
| Government | High importance | High importance | Low importance | Standardized PC offerings for all employees. MacBooks are provided with justification. Devices managed with Intune and ConfigMgr. |
Good devices are necessary for overall IT satisfaction
BUT
Good devices are not enough for high satisfaction
A bad device can ruin a person’s satisfaction with IT
Info-Tech’s CIO Business Vision has shown that when someone is dissatisfied with their device, their satisfaction with IT overall is only 40.92% on average.
When a person is satisfied with their device, their average satisfaction increases by approximately 30 percentage points to 70.22%. (Info-Tech Research Group, CIO Business Vision, 2021; N=119,383)
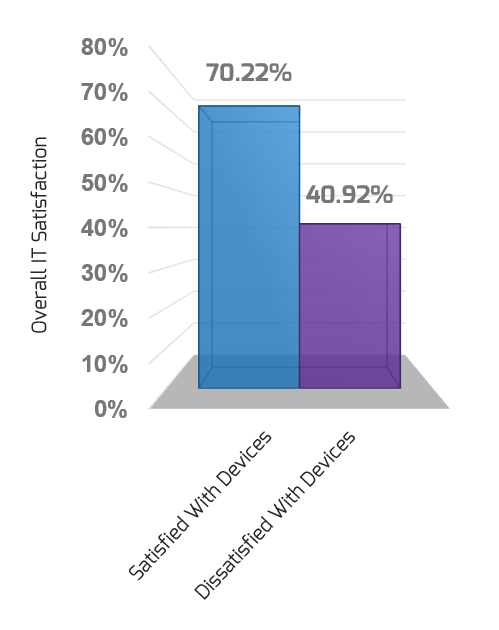
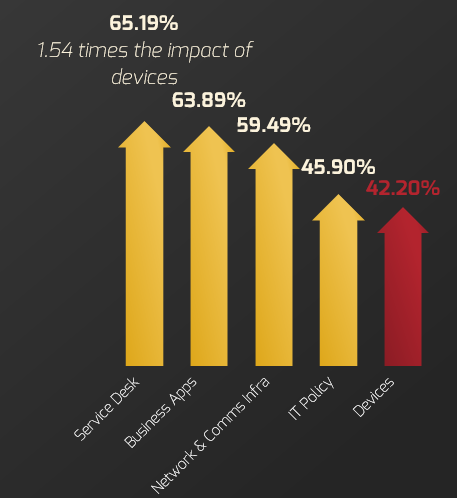
Improvements in the service desk, business apps, networks and communication infrastructure, and IT policy all have a higher impact on increasing satisfaction.
For every one-point increase in satisfaction in those areas, respondents’ overall satisfaction with IT increased by the respective percentage of a point. (Info-Tech Research Group, CIO Business Vision, 2021; N=119,409)
End-User Paradigms Have Shifted
Take end-user computing beyond the device
Operating System - OS
Only Windows
- More choices than ever before
Endpoint Management System - UEM
Group Policy & Client Management
- Modern & Unified Endpoint Management
Personal Devices - BYOD
Limited to email on phones
- Full capabilities on any device
IT Asset Management - ITAM
Hands-on with images
- Zero-touch with provisioning packages
Virtual Desktops - DaaS
Virtual Desktop Infrastructure in the Data Center
- Desktop-as-a-Service in the cloud
Business-Managed Apps - BMA
Performed by IT
- Performed by the Business and IT
Work-From-Anywhere - WFA
Rare
- Default
Customer Satisfaction - C Sat
Phone calls and transactional interactions
- Self-serve & managing entire experience
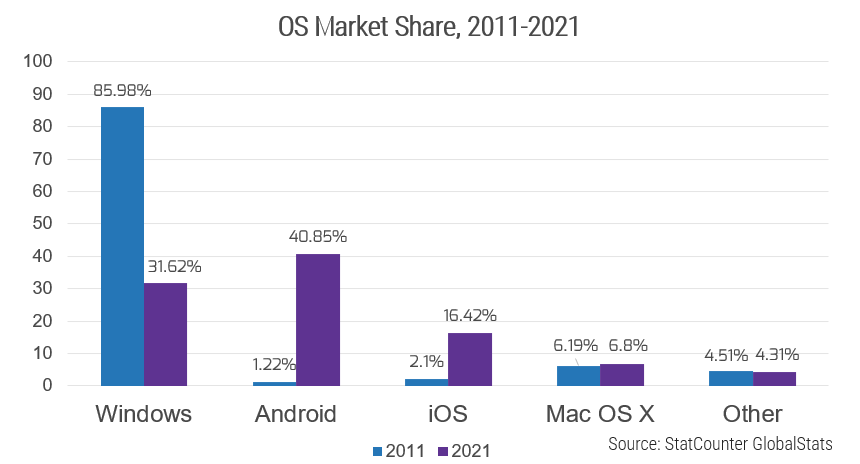
Don’t limit your focus to only Windows and Macs
Android is the OS with the largest market share
Users and IT have more choices than ever before
Operating System - OS
Only Windows
- More choices than ever before
Microsoft is still the dominant player in end-user computing, but Windows has only a fraction of the share it once had.
IT needs to revisit their device management practices. Modern management tools such as unified endpoint management (UEM) tools are better suited than traditional client management tools (CMT) for a cross-platform world.
IT must also revisit their application portfolios. Are business apps supported on Android and iOS or are they only supported on Windows? Is there an opportunity to offer more options to end users? Are end users already running apps and handling sensitive data on Android and iOS through software-as-a-service and bring-your-own-device (BYOD) capabilities in Office 365 and Google apps?
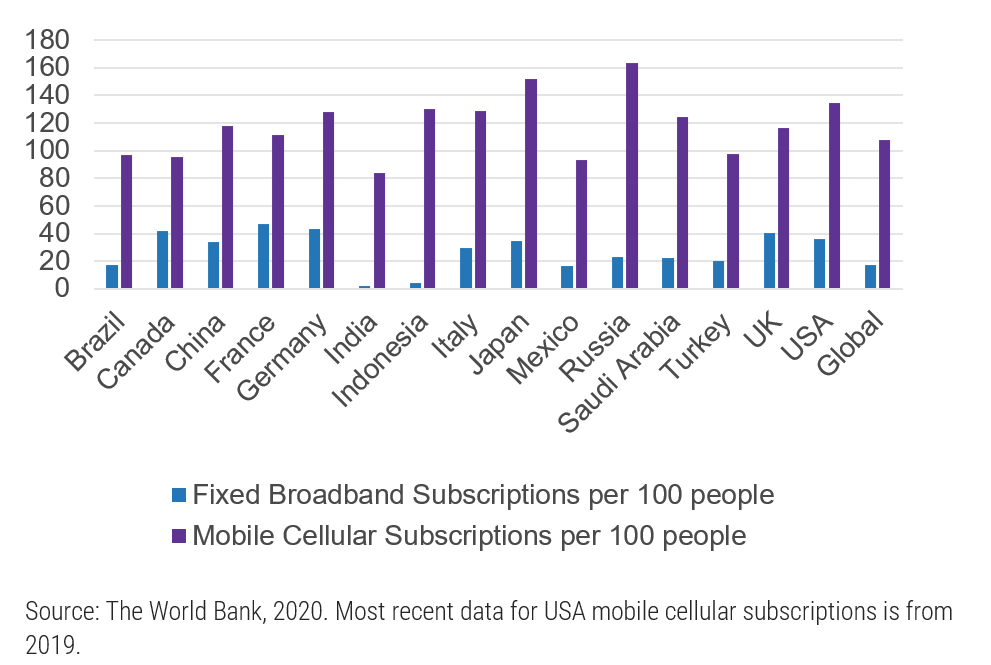
OS market share is partly driven by the digital divide
If someone must choose between a smartphone and a computer, they go with a smartphone
IT can’t expect everyone to be fluent on Windows and Mac, have a computer at home, or even have home broadband.
Of US adults aged 18-29:
- 96% have a smartphone (the rest have cellphones).
- Only 70% of US adults aged 18-29 have a home broadband connection.
Further, only 59% of US adults making less than $30,000/year have a laptop or desktop. (“Mobile Technology” and “Digital Divide,” Pew Research, 2021.)
Globally, people are likelier to have a cell subscription than they are to have access to broadband.
Embrace new device management paradigms
Endpoint Management System - UEM
Group Policy & Client Management
- Modern & Unified Endpoint Management
Evaluate enterprise mobility management and unified endpoint management to better support a remote-first, cross-platform reality.
Client Management Tool (CMT)
CMTs such as Microsoft Endpoint Configuration Manager (ConfigMgr, aka SCCM) can be used to distribute apps, apply patches, and enforce group policy.
Enterprise Mobility Management (EMM)
EMM tools allow you to manage multiple device platforms through mobile device management (MDM) protocols. These tools enforce security settings, allow you to push apps to managed devices, and monitor patch compliance through reporting.
EMM tools often support mobile application management (MAM) and mobile content management (MCM). Most EMM tools can manage devices running Windows, Mac OS, iOS, and Android, although there are exceptions.
Unified Endpoint Management (UEM)
UEM solutions combine CMT and EMM for better control of remote computers running Windows or Macs. Examples include:
- Windows devices comanaged by Intune and ConfigMgr.
- Mac devices managed by Jamf Pro.
- Mac devices comanaged by Jamf Pro and Intune.
Most UEM tools can manage devices running Windows, Mac OS, iOS, and Android, allowing IT to manage all end-user devices from a unified tool set (although there are exceptions).
Mobile Application Management (MAM)
MAM provides the ability to package an app with security settings, distribute app updates, and enforce app updates. Some capabilities do not require apps to be enrolled in an EMM or UEM solution.
Mobile Content Management (MCM)
MCM tools distribute files to remote devices. Many MCM solutions allow for security settings to be applied, such as encrypting the files or prohibiting data from leaving the secure container. Examples include OneDrive, Box, and Citrix ShareFile.
Adopt modern management with EMM and UEM – better toolsets for today’s state of EUC
Sacrifice your Group Policy Objects to better manage Windows computers
| Windows Management Features | Traditional CMT | Hybrid UEM | Cloud-Based EMM |
|---|---|---|---|
| Group Policy | ✔ Primary management approach | ✔ Available alongside configuration service providers | X Replaced by configuration service providers |
| Manage remote devices without VPN | X | X | ✔ |
| No longer manage and maintain images | X | ✔ Images are still available | ✔ Images replaced by provisioning packages |
| Secure and support BYOD | X (Certain tools may offer limited MDM capabilities) | ✔ | ✔ |
| Support remote zero-touch provisioning | X (Only available via PXE boot) | ✔ | ✔ |
| App, patch, update deployments | Via defined distribution points | Via defined distribution points or MAM | Via MAM |
IT asset management practices are shifting
IT Asset Management - ITAM
Hands-on with images
- Zero-touch with provisioning packages
Supply chain issues are making computers longer to procure, meaning users are waiting longer for computers (Cision, 2021). The resulting silicon chip shortage is expected to last until at least 2023 (Light Reading, 2021).
IT departments are delaying purchases, delaying refreshes, and/or purchasing more to reserve devices before they need them.
Remote work has increased by 159% over the past 12 years (NorthOne, 2021). New hires and existing users can’t always go into the office to get a new computer.
IT departments are paying vendors to hold onto computers and then drop-ship them directly to the end user. The devices are provisioned using zero touch (e.g. Autopilot, Apple Device Manager, or another tool). Since zero-touch provisioning tools do not support images, teams have had to switch to provisioning packages.
The pandemic saw an increase in spending on virtual desktops
Virtual desktops offered powerful tools for supporting remote devices and personal computers without compromising sensitive data
Virtual Desktops - DaaS
Virtual Desktop Infrastructure in the Data Center
- Desktop-as-a-Service in the cloud
The pandemic helped cloud-based virtual desktop infrastructure (VDI)
Citrix saw subscription revenue increase 71% year over year in 2020 (Citrix 2020 Annual Report, p. 4). VMware saw subscription and SaaS revenue increase 38% from January 2020 to 2021 – while on-premises licensing revenue decreased by 5% (VMware Annual Report 2021, p. 40).
IT no longer needs to manage the underlying infrastructure
Microsoft and AWS are offering desktops as a service (i.e. cloud-based virtual desktops). IT needs to manage only the device, not the underlying virtual desktop infrastructure. This is in addition to Citrix’s and VMware’s cloud offerings, where IT doesn’t need to manage the underlying infrastructure that supports VDI.
Visit the blueprint Implement Desktop Virtualization and Transition to Everything as a Service to get started.
Work-from-anywhere (WFA) is now the default
COVID-19 forced this shift
Work-From-Anywhere - WFA
Rare
- Default
Be prepared to support a hybrid workforce, where people are sometimes working remotely and sometimes working in the office.
- Device provisioning and deployment need to be rethought. In-person deployment is not always possible. IT should evaluate tools such as zero-touch provisioning.
- Service desks need better monitoring and management tools. End-user experience management (EUEM) can allow you to better identify where network issues are occurring – in your data center, at the user’s house, in the cloud, or somewhere in between. Remote control tools can then allow your tier 1 to remediate issues on the user’s device.
- Apps and devices need to be usable from anywhere. Environments that rely on desktops and on-premises apps need to be rearchitected for a remote-first workforce.
- Users are living inside video conferencing tools. With the impact of the COVID-19 pandemic, there are about 145 million daily users of Microsoft Teams, almost twice the number of users in 2020 (MUO, 2021). Ensure they have the training and expertise to effectively use these tools.
“More technical troubleshooting due to users working from home a lot more. It can be more difficult to talk users through fixes when they are off site if you cannot remotely assist so more emphasis on the communication skill which was already important.” (Service Desk Institute, 2021)
Visit the Hybrid Workplace Research Center to better support a hybrid workforce.
BYOD fully includes personal computers
It’s no longer about whether IT will allow BYOD
Stop pretending BYOD doesn’t happen
Personal Devices - BYOD
Limited to email on phones
- Full capabilities on any device
- BYOD (including BYOPC) is turned on by default. SaaS tools like Office 365 are built to be used on multiple devices, including multiple computers. Further, the pandemic saw 47% of organizations significantly increase their use of BYOD (Cybersecurity Insiders, 2021; N=271).
- BYOD can boost productivity. When employees can use smartphones for work, they report that it increases their productivity by 34 percent (Samsung Insights, 2016).
- BYOD is hard to support, so most organizations don’t. Only 22% of organizations provide full support for mobile devices, while 20% provide no support, 25% provide ad hoc support, and 26% provide limited support (Cybersecurity Insiders, 2021). If smartphones and tablets are heavily ingrained in business processes, then migrating to BYOD can overload the service desk.
- Securely enable employees. Mobile application management (MAM), mobile content management (MCM), and Office 365 have gotten smarter at protecting corporate data.
Action Item: Identify how IT can provide more support to personally owned computers, tablets, and smartphones.
58% of working Americans say their work devices are “awful to work on." (PCMag, 2021)
But only 22% of organizations provide full support to BYOD. (Cybersecurity Insiders, 2021)
IT must either provide better devices or start fully supporting users on personal PCs.
Build governance practices for low-code development platforms
Managing 1,000 different apps built out on low-code business process management platforms is hard, but it’s not nearly as hard as managing 1,000 unique SaaS apps or access databases
Business-Managed Apps - BMA
Performed by IT
- Performed by the Business and IT
Pros - Opportunities
- Offers DIY to users
- Business can build them quickly
- IT has central visibility
- IT can focus on the platform
Cons - Threats
- Sensitive data can get exposed
- Users may have issues with continuity and backup
- Responding to platform changes will be potentially challenging
- Support may be difficult after the app creator leaves
Action Item: Build a governance framework that describes the roles and responsibilities involved in business-owned apps. Identify the user’s role and end-user computing’s role in supporting low-code apps.
Visit the blueprint Embrace Business-Managed Apps to learn how to build a governance framework for low-code development platforms.
Visit the Low-Code Business Process Management SoftwareReviews category to compare different platforms.
Update your customer service practices
End users expect self-service and help from tier 1
Re-evaluate how you support both corporate-issued and personal-owned computers and mobile devices
Customer Satisfaction - C Sat
Phone calls and transactional interactions
- Self-serve & managing entire experience
Microsoft’s 2019 “Global State of Customer Service” report shows that people have high expectations:
- 31% of people expect call agents to have a “deep understanding of the caller’s relationship with the company”
- 11% expect self-service capabilities
End users have the same expectations of IT, the service desk, and end-user computing teams:
- Users expect any IT person with whom they are talking to have a deep understanding of their devices, apps, open tickets, and closed tickets.
- Users expect tier 1 to be able to resolve their incidents and requests without escalating to tier 2 or tier 3 end-user computing specialists.
Most Important Aspects of Customer Service
Resolving issue in one interaction - 35%
Knowledgeable agent - 31%
Finding information myself - 11%
Not repeating information - 20%
(Microsoft, 2019)
Desktop engineering needs to shift left
Revisit what work can only be done by tier 2 and tier 3 teams
Shifting left involves shifting resolution of incidents and service requests down from more costly resources to the first line of support and to end users themselves through self-service options
- Tier 1 needs up-to-date information on the end users’ devices and open tickets.
- Users should be able to request apps and download those apps through a self-service portal, a software catalog, or an app store.
- Tier 1 needs to be empowered to remote wipe devices, see troubleshooting and diagnostics information, and resolve incidents without needing to escalate.
Action Item: Apply shift-left enablement to train tier 1 agents on troubleshooting more incidents and fulfilling more service requests. Build top-notch self-service capabilities for end users.
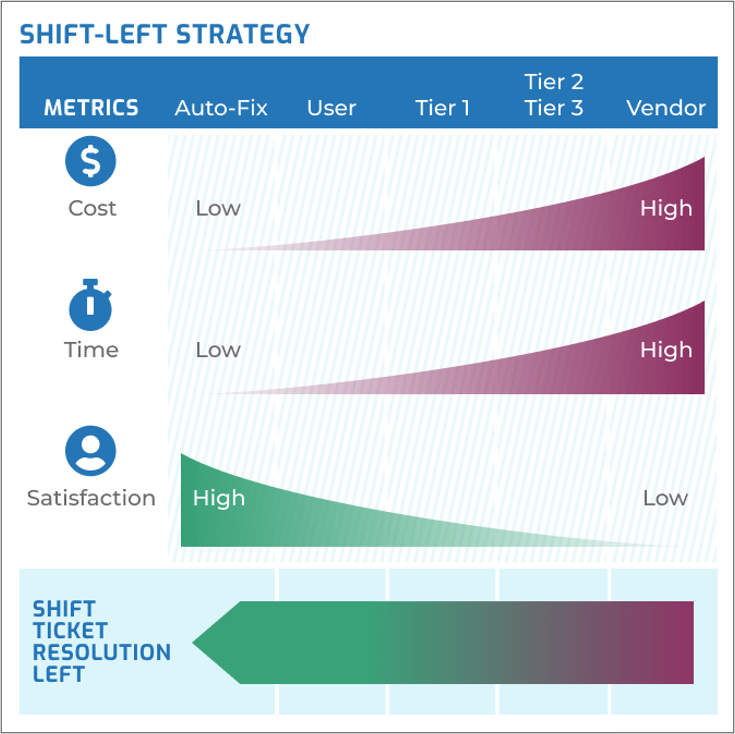
Work with your service desk on the blueprint Optimize the Service Desk with a Shift-Left Strategy.
Windows 11 is coming
Prepare to make the jump
The sooner you start, the easier the migration will be
- Begin planning hardware refreshes. Old computers that do not have a TPM 2.0 chip are not currently supported on Windows 11 (“Enable TPM 2.0,” Microsoft, 2021). If you have old computers that will not support the jump to Windows 11– especially given the supply chain disruptions and silicon chip shortages – it is time to consider computer upgrades.
- The end of Windows 10 is coming. Windows 10’s retirement date is currently October 14, 2025 (“Windows 10 Home and Pro,” Microsoft, 2021). If you want to continue running Windows 10 on older computers beyond that time, you will need to pay for extended support or risk those computers being more easily breached.
- Begin testing your apps internally. Run Windows 11 within IT and test whether your apps will work on Windows 11.
- Pilot Windows 11 with IT-friendlies. Find users that are excited for Windows 11 and will not mind a bit of short-term pain.
- What is your risk appetite? Risk-averse organizations will want to wait until Microsoft, DISA, and/or Center for Internet Security have published security configuration best practices.
Info-Tech’s approach
Master the ever-expanding puzzle of end-user computing
User Group Analysis
Supported Devices and Apps
Fitness for Use
Device Support
The Info-Tech difference:
- Balance user choice, risk mitigation, and cost optimization. The right balance will be unique for every organization.
- Standardize the nonstandard. Anticipate your users’ needs by having power options and prestigious options ready to offer.
- Consider multiple personas when building your standards, training, and migrations. Early Adopters, Late Adopters, VIP Users, Road Warriors, and Hoarders – these five personas will exist in one form or another throughout your user groups.
Modernize and Transform Your End-User Computing Strategy
Focus on the Big Picture
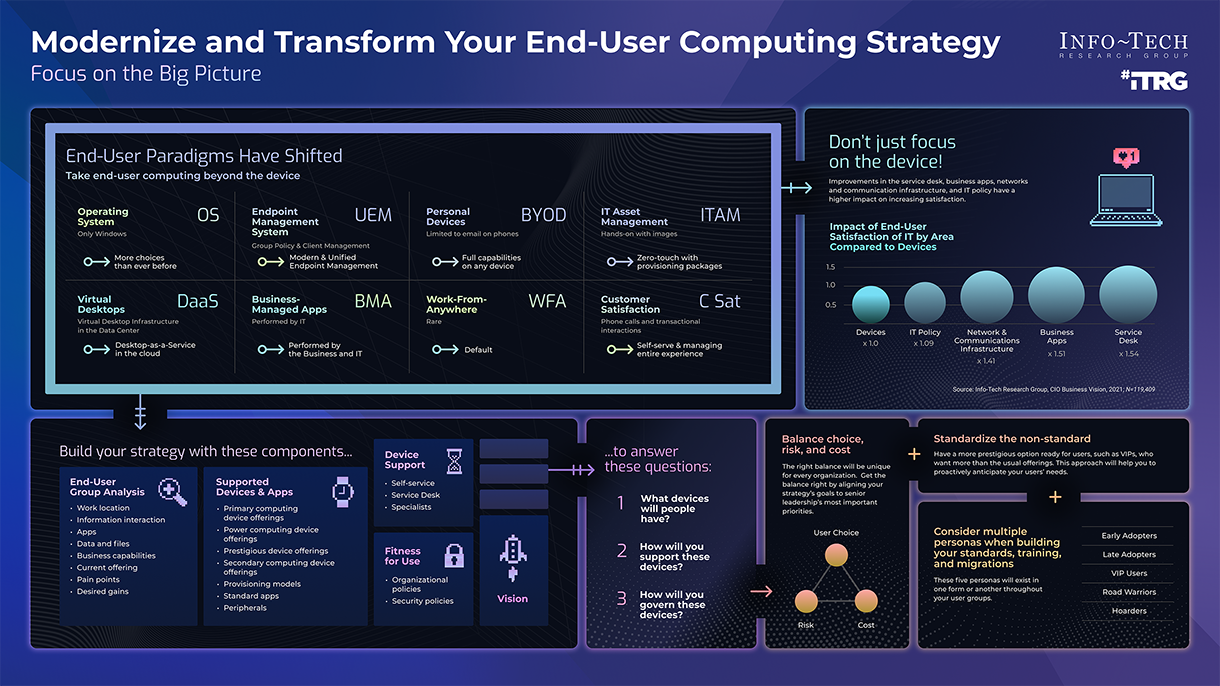
End-User Paradigms Have Shifted
Take end-user computing beyond the device
Operating System - OS
Only Windows
- More choices than ever before
Endpoint Management System - UEM
Group Policy & Client Management
- Modern & Unified Endpoint Management
Personal Devices - BYOD
Limited to email on phones
- Full capabilities on any device
IT Asset Management - ITAM
Hands-on with images
- Zero-touch with provisioning packages
Virtual Desktops - DaaS
Virtual Desktop Infrastructure in the Data Center
- Desktop-as-a-Service in the cloud
Business-Managed Apps - BMA
Performed by IT
- Performed by the Business and IT
Work-From-Anywhere - WFA
Rare
- Default
Customer Satisfaction - C Sat
Phone calls and transactional interactions
- Self-serve & managing entire experience
Don't just focus on the device!
Improvements in the service desk, business apps, networks and communication infrastructure, and IT policy have a higher impact on increasing satisfaction.
Impact of End-User Satisfaction of IT by Area Compared to Devices
Devices (x1.0)
IT Policy (x1.09)
Network & Communications Infrastructure (x1.41)
Business Apps (x1.51)
Service Desk (x1.54)
(Info-Tech Research Group, CIO Business Vision, 2021; n=119,409)
Build your strategy with these components...
End-User Group Analysis
- Work location
- Information interactions
- Apps
- Data and files
- Business capabilities
- Current offering
- Pain points
- Desired gains
Supported Devices & Apps
- Primary computing device offerings
- Power computing device offering
- Prestigious device offerings
- Secondary computing device offerings
- Provisioning models
- Standard apps
- Peripherals
Device Support
- Self-service
- Service Desk
- Specialists
Fitness for Use
- Organizational policies
- Security policies
Vision
...to answer these questions:
- What devices will people have?
- How will you support these devices?
- How will you govern these devices?
Balance choice, risk, and cost
The right balance will be unique for every organization. Get the balance right by aligning your strategy's goals to senior leadership’s most important priorities.
- User choice
- Risk
- Cost
+ Standardize the non-standard
Have a more prestigious option ready for users, such as VIPs, who want more than the usual offerings. This approach will help you to proactively anticipate your users' needs.
+Consider multiple personas when building your standards, training, and migrations
These five personas will exist in one form or another throughout your user groups.
- Early Adopters
- Late Adopters
- VIP Users
- Road Warriors
- Hoarders
Use our approach to answer these questions:
What computers will people have?
Types of computing devices
- Power desktop
- Power laptop
- Desktop
- Laptop
- Virtual Desktop
- Thin Client Device
- Pro Tablet
- Tablet
- Smartphone
Corporate-Issued Approaches
- Kiosk – Shared, Single Purpose
- Pooled – Shared, Multipurpose
- Persistent – Individual
- Personally Owned
Supported Operating Systems
- Windows
- Mac
- Chrome OS
- Linux
- iOS/iPad OS
- Android
How will you support these devices?
Device Management
- Manual
- CMT
- EMM
- UEM
- Pooled Virtual Desktop Manager
Supporting Practices
- Self-Service
- Tier 1 Support
- Specialist Support
How will you govern these devices?
Corporate Policies
- Personal Use Allowed?
- Management and Security Policies
- Personal Device Use Allowed?
- Supported Apps and Use Cases
- Who Is Allowed to Purchase?
- Prohibited Apps and Use Cases
- Device Entitlement
- Stipends and/or Reimbursement to Users
Use our blueprint to improve your EUC practices
- Devices
- Corporate-issued devices
- Standard offerings
- User Support
- Self-service
- Tier 1 support
- Use Cases
- Providing value
- Business apps
- Policy & Governance
- Personal device use
- IT policy
- Fitness for Use
- Securing devices
- Patching
Info-Tech’s methodology for end-user computing strategy
| 1. Set the Direction | 2. Define the Offering | 3. Build the Roadmap | |
|---|---|---|---|
| Phase Steps |
1.1 Identify Desired Benefits 1.2 Perform a User Group Analysis 1.3 Define the Vision |
2.1 Define the Standard Offerings 2.2 Outline Supporting Services 2.3 Define Governance and Policies |
3.1 Develop Initiatives |
| Phase Outcomes |
Current-State Assessment Goals Cascade User Group Assessment Vision Statement Mission Statement Guiding Principles |
Standard Offerings by User Group Device Management Model Technical Support Model Device Entitlement Policy Acceptable Use Policy Remote Wipe Policy & Waiver Personal Device Reimbursement Policy |
End-User Migration Journey Map Strategy and Roadmap |
Insight summary
Once users are satisfied with devices, focus on the bigger picture
If end users are dissatisfied with devices, they will also be dissatisfied with IT. But if you don’t also focus on apps and supportability, then giving users better devices will only marginally increase satisfaction with IT.
Bring it back to stakeholder priorities
Before you build your vision statement, make sure it resonates with the business by identifying senior leadership’s priorities and aligning your own goals to them.
Balance choice, risk, and cost
The balance of user choice, risk mitigation, and cost optimization is unique for each company. Get the balance right by aligning your strategy’s goals to senior leadership’s most important priorities.
Communicate early and often with users
Expect users to become anxious when you start targeting their devices. Address this anxiety by bringing them into the conversation early in the planning – they will see that their concerns are being addressed and may even feel a sense of ownership over the strategy.
Standardize the nonstandard
When users such as VIP users want more than the standard offering, have a more prestigious option available. This approach will help you to proactively anticipate your users’ needs.
Consider multiple personas when building your standards, training, and migrations
Early Adopters, Late Adopters, VIP Users, Road Warriors, and Hoarders – these five personas will exist in one form or another throughout your user groups.
Blueprint deliverables
Each step of this blueprint is accompanied by supporting deliverables to help you accomplish your goals:
User Group Analysis Workbook
Use these worksheets to guide your analysis.
End-User Computing Ideas Catalog
Compare options for your end-user computing environment.
Standard End-User Entitlements and Offerings
Define your supported offerings and publish this document in your service catalog.
Policy Templates
Use these templates as a starting point for addressing policy gaps.
Key deliverable:
End-User Computing Strategy
Document your strategy using this boardroom-ready template.
Blueprint benefits
IT Benefits
- Deliver immediate value to end users.
- Provide the best service based on the user persona.
- Provide better device coverage.
- Use fewer tools to manage a less diverse but equally effective array of end-user computing devices.
- Provide more managed devices that will help to limit risk.
- Have better visibility into the end-user computing devices and apps.
Business Benefits
- Conduct corporate business under one broad strategy.
- Provide support to IT for specific applications and devices.
- Take advantage of more scalable economies for providing more advantageous technologies.
- Experience less friction between end users and the business and higher end-user satisfaction.
Measure the value of this blueprint
Your end-user computing strategy is an investment
Track the returns on your investment, even if those returns are soft benefits and not cost reductions
User Satisfaction
- Satisfaction with device
- Satisfaction with business apps
- Satisfaction with service desk timeliness
- Satisfaction with service desk effectiveness
- Satisfaction with IT Employee engagement
Total Cost
- Spend on each type of device
- Cost of licenses for management tools, operating systems, and apps
- Cost of support agreements # of support tickets per device per employee
- Time spent supporting devices per tier or support team
- Time spent per OS/app release
Risk Mitigation
- # of devices that are end-of-life
- % of devices in compliance
- # of unmanaged devices
- # of devices that have not checked in to management tool
Info-Tech offers various levels of support to best suit your needs
DIY Toolkit
"Our team has already made this critical project a priority, and we have the time and capability, but some guidance along the way would be helpful."
Guided Implementation
"Our team knows that we need to fix a process, but we need assistance to determine where to focus. Some check-ins along the way would help keep us on track."
Workshop
"We need to hit the ground running and get this project kicked off immediately. Our team has the ability to take this over once we get a framework and strategy in place."
Consulting
"Our team does not have the time or the knowledge to take this project on. We need assistance through the entirety of this project."
Diagnostics and consistent frameworks are used throughout all four options.
Guided Implementation
What does a typical GI on this topic look like?
A Guided Implementation (GI) is a series of calls with an Info-Tech analyst to help implement our best practices in your organization.
A typical GI is 8 to 10 calls over the course of 4 to 6 months.
Phase 1: Set the Direction
- Call #1: Review trends in end-user computing and discuss your current state.
- Call #2: Perform a user group analysis.
- Call #3: Identify desired benefits and map to stakeholder drivers.
Phase 2: Define the Offering
- Call #4: Define standard offerings.
- Call #5: Select provisioning models.
- Call #6: Outline supporting services and opportunities to shift end-user computing support left.
- Call #7: Identify gaps in governance and policies.
Phase 3: Build the Roadmap
- Call #8: Develop initiatives.
- Call #9: Plan migration and build roadmap.
EUC Strategy Workshop Overview
Contact your account representative for more information.
workshops@infotech.com 1-888-670-8889
| Day 1 | Day 2 | Day 3 | Day 4 | Day 5 | |
|---|---|---|---|---|---|
| Set the Direction | Define the Offering | Support the Offering | Bridge the Gap and Create the Roadmap | Next Steps and Wrap-Up (offsite) | |
| Activities |
1.1 Identify desired benefits. 1.1.1 Assess the current state of end-user computing. 1.1.2 Perform a SWOT analysis. 1.1.3 Map benefits to stakeholder drivers and priorities. 1.2 Analyze user groups. 1.2.1 Identify user groups. 1.2.2 Identify supporting technology. 1.2.3 Record use cases. 1.2.4 Identify opportunities to provide value. |
1.3 Define the vision. 1.3.1 Prioritize benefits. 1.3.2 Craft a vision and mission statement. 1.3.3 Identify goals. 1.3.4 Define guiding principles for your strategy. 2.1 Define the standard offerings. 2.1.1 Select a provisioning model for each persona. 2.1.2 Define the standard device offerings. 2.1.3 Document each personas’ entitlements. |
2.2 Outline supporting practices. 2.2.1 Define device management tools and approach. 2.2.2 Identify groups involved in supporting practices. 2.2.4 Identify opportunities to improve customer service. 2.3 Define policies. 2.3.1 Define acceptable use. 2.3.2 Define BYOD policies. 2.3.3 Define procurement and entitlement policies. 2.3.4 Define security policies. |
3.1 Develop initiatives. 3.1.1 Identify the gaps in devices, user support, use cases, policy & governance, and fitness for use. 3.1.2 Plan the deployment and user migration journey. 3.1.3 Document initiatives in the roadmap . |
5.1 Complete in-progress deliverables from previous four days. 5.2 Set up time to review workshop deliverables and discuss next steps |
| Deliverables |
|
|
|
|
|
Phase 1
Set the Direction
Set the Direction
1.1 Identify Desired Benefits
1.2 Perform a User Group Analysis
1.3 Define the Vision
Define the Offering
2.1 Define the Standard Offerings
2.2 Outline Supporting Services
2.3 Define Governance and Policies
Build the Roadmap
3.1 Develop Initiatives
This phase will walk you through the following activities:
- Current-state analysis
- Goals cascade
- Persona analysis
This phase involves the following participants:
- End-User Computing Team
- IT Leadership
Set a direction that will create value for IT, stakeholders, and end users
Use your insights to build your strategy
Start by downloading Info-Tech’s End-User Computing Strategy Template
- Perform a stop-start-continue exercise for how IT supports end-user devices.
- Perform a goals cascade to identify how the end-user computing strategy can align with and support senior leaders’ priorities and strategic objectives.
- Perform a user group analysis to identify what IT can do to provide additional value to end users.
- Use the results to define a vision for your end-user computing strategy and in-scope benefits.
Download the End-User Computing Strategy Template.
Step 1.1
Identify Desired Benefits
Activities
1.1.1 Assess the current state of end-user computing
1.1.2 Perform a SWOT analysis
1.1.3 Map benefits to stakeholder drivers and priorities
Optional: Identify current total cost of ownership
This step requires the following inputs:
- Current approach for end-user computing
- List of strengths and weaknesses of the current approach
This step involves the following participants:
- CIO
- End-User Computing Team
- IT Leadership
- End-User Computing Manager
Outcomes of this step
- Defined success metrics that are tied to business value
- Vision statement, mission statement, and guiding principles
Review your current state for each end-user computing practice
- Devices
- Corporate-issued devices
- Standard offerings
- User Support
- Self-service
- Tier 1 support
- Use Cases
- Providing value
- Business apps
- Policy & Governance
- Personal device use
- IT policy
- Fitness for Use
- Securing devices
- Patching
1.1.1 Assess the current state of end-user computing
Discuss IT’s strengths and challenges
Review your success in responding to the trends highlighted in the executive brief.
- Start by reviewing the trends in the executive brief. Identify which trends you would like to focus on.
- Review the domains below. Discuss:
- Your current approach
- Strengths about this approach
- Challenges faced with this approach
- Document the results in the “Current-State Assessment” section of your End-User Computing Strategy.
- Devices
- Corporate-issued devices
- Standard offerings
- User Support
- Self-service
- Tier 1 support
- Use Cases
- Providing value
- Business apps
- Policy & Governance
- Personal device use
- IT policy
- Fitness for Use
- Securing devices
- Patching
Download the End-User Computing Strategy Template.
Consider these aspects of end-user computing in your assessment
Devices: As shown in the executive brief, devices are necessary for satisfaction in IT. In your current-state assessment, outline the principal means by which users are provided with a desktop and computing.
- Corporate-issued devices: Document the types of devices (e.g. laptops, desktops, smartphones) and operating systems that IT currently supports.
- Strengths: Highlight user satisfaction with your current offerings by referencing recent relationship surveys.
- Challenges: Document corporate-issued devices where stakeholders and users are not satisfied, platforms that stakeholders would like IT to support, etc.
- Standard offerings: Name the high-level categories of devices that you offer to end users (e.g. standard device, power device).
- Strengths: Outline steps that IT has taken to improve the portfolio of standard offerings and to communicate the offerings.
- Challenges: Identify areas to improve the standard offerings.
User support: Examine how the end-user computing team enables a high-quality customer service experience. Especially consider self-service and tier 1 support.
- Self-service: Describe the current state of your self-service capabilities (e.g. name of the self-service portal, number of apps in the app store).
- Strengths: Outline successes with your self-service capabilities (e.g. use of self-service tools, recently deployed tools, newly supported platforms).
- Challenges: Identify gaps in self-service capabilities.
- Tier 1 support: Document the number of end-user computing incidents and service requests that are resolved at tier 1 as well as the number of incidents and service requests that are resolvable without escalation.
- Strengths: Identify technologies that make first contact resolution possible. Outline other items that support tier 1 resolution of end-user computing tickets, such as knowledgebase articles and training programs.
- Challenges: Document areas in which tier 1 resolution of end-user computing tickets is not feasible.
Considerations (cont’d.)
Use cases: Reflect on how IT and end-user computing supports users’ most important use cases. Consider these aspects:
- Providing value: Identify the number of user groups for which you have completed a user group analysis. Outline your major approaches for capturing feedback, such as relationship surveys.
- Strengths: Document any successful initiatives around stakeholder relationships and requirements gathering. You can also highlight successful metrics, such as high satisfaction scores from a team, department, or division.
- Challenges: Identify where there are dissatisfied stakeholders and gaps in product offerings and where additional work around value generation is required.
- Business apps: Outline your major business apps and your approach to improvement for these apps. If you need assistance gathering feedback from end users and stakeholders, you can use Info-Tech’s Application Portfolio Assessment.
- Strengths: Show the EUC team’s successes in supporting critical business apps (e.g. facilitating user acceptance testing, deploying via endpoint management tool).
- Challenges: Name business apps that are not meeting stakeholder needs. Consider if end users are dissatisfied with an app, if IT is unable to adequately monitor and support a business app, etc.
Policy and governance: Document the current state of policies governing the use of end-user computing devices, both corporate-issued and personally owned. Review Step 2.3 for a list of policy questions to address and for links to policy templates.
- Personal device use: Explain which users are allowed to use personally owned devices, what use cases are supported, and which types of devices are supported. Also, highlight explicit prohibitions.
- Strengths: Highlight major accomplishments with BYOD, utilization metrics, etc. Consider including any platforms or apps that support BYOD (e.g. Microsoft Office 365).
- Challenges: Identify where there are gaps in your support for personal devices. Examples can include insufficient management tools, lack of feedback from end users on BYOD support, undefined policies and governance, and inadequate support for personal devices.
Considerations (cont’d.)
IT policies: List your current policy documents. Include policies that relate to end-user computing, such as security policy documents; acceptable use policy documents; purchasing policies; documents governing entitlements to computers, tablets, smartphones, and prestigious devices; and employee monitoring policy documents.
- Strengths: Outline the effectiveness of these policies, user compliance to these policies, and your success in enforcing these policies.
- Challenges: Identify where you have gaps in user compliance, gaps in enforcing policies, many exceptions to a policy, etc.
Fitness for use: Reflect on your ability to secure users, enterprise data, and computers. Document your current capabilities to ensure devices are adequately secured and risks adequately mitigated.
- Securing devices: Describe your current approach to implementing security baselines, protecting data, and ensuring compliance.
- Strengths: Highlight your accomplishments with ensuring devices meet your security standards and are adequately managed.
- Challenges: Identify areas that are not adequately protected, where IT does not have enough visibility, and devices on which IT cannot enforce security standards.
- Patching: Describe your current approach to distributing OS patches, distributing app patches, and ensuring patch compliance.
- Strengths: Outline steps that IT has taken to improve release and deployment practices (e.g. user acceptance testing, deployment rings).
- Challenges: When is IT unable to push a patch to a device? Outline when devices cannot receive a patch, when IT is unable to ensure patches are installed, and when patches are disruptive to end users.
1.1.2 Perform a SWOT analysis
Summarize your current-state analysis
To build a good strategy, you need to clearly understand the challenges you face and opportunities you can leverage.
- Summarize IT’s strengths. These are positive aspects internal to IT.
- Summarize IT’s challenge. What internal IT weakness should the strategy address?
- Identify high-level opportunities. Summarize positive factors that are external to IT (e.g. within the larger organization, strong vendor relationships).
- Document threats. What external factors present a risk to the strategy?
Record your SWOT analysis in the “Current-State Assessment” section of your End-User Computing Strategy Template.
Download the End-User Computing Strategy Template.
1.1.3 Map benefits to stakeholder drivers and priorities
Use a goals cascade to identify benefits that will resonate with the business
Identify how end-user computing will support larger organizational strategies, drivers, and priorities
- Identify stakeholders. Focus on senior leaders – user groups will be addressed in Step 1.2.
- For each stakeholder, identify three to five drivers or strategic priorities. Use the drivers as a starting point to:
- Increase productivity
- Mitigate risks
- Optimize costs
- Map the benefits you brainstormed in Step 1.1 to the drivers. It’s okay to have benefits map to multiple drivers.
- Re-evaluate benefits that don’t map to any drivers. Consider removing them.
| Stakeholder | Drivers and Strategic Priorities | End-User Computing Benefits |
|---|---|---|
| CEO | Ensure service continuity with remote work |
|
| Respond to COVID-19 changes with agility |
|
|
| Reduce unnecessary costs |
|
|
| COO | Business continuity: being able to work from home |
|
Record this table on the “Goals Cascade” slide in the “Vision and Desired Benefits” section of your End-User Computing Strategy Template.
Use the CEO-CIO Alignment Program to identify which business benefits are most important.
Sample end-user computing benefits
| Business Goals | End-User Computing Benefits | |||
|---|---|---|---|---|
| Manage risk | Controls are effectively enforced on remote devices | Sensitive data is secured | Devices and data are accounted for | |
| Ensure service continuity | Business processes can still function with remote personnel | Customers can still be served by remote workers | Personnel can be productive from anywhere | IT practices can still operate remotely |
| Comply with external regulation | Improved ability to demonstrate compliance | |||
| Respond to change with agility | Personnel can be productive from anywhere | More business processes can be performed remotely | ||
| Improve operational efficiency | More efficient sales practices | More efficient customer service practices | Increased number of digitized business processes | Increased use of IT and HR self-service tools |
| Offer competitive products and services | Increased customer satisfaction with online services | Number of piloted new products | ||
| Manage people | Increased employee productivity | Increased employee engagement | Increased talent attraction | Increased workforce retention |
| Make data-driven decisions | Increased workforce retention | Improved understanding of customers | Access to accurate data on services and spending | Improved IT cost forecasting |
| Improve customer experience | Increased customer satisfaction with online services | Ability to scale up capacity to meet increased demand | Customers can still be served by remote workers | Improved customer self-service options |
| Maximize stakeholder value | Transition to OpEx spend and reduce CapEx investments | Access to accurate data on services and spending | Improved IT cost forecasting | |
Optional: Identify current total cost of ownership
Be mindful of hidden costs, such as those associated with supporting multiple devices and maintaining a small fleet of corporate devices to ensure business continuity with BYOD.
- Use the Hardware Asset Management Budgeting Tool to forecast spend on devices (and infrastructure) based on project needs and devices nearing end of life.
- Use the Mobile Strategy TCO Calculator to estimate the total cost of all the different aspects of your mobile strategy, including:
- Training
- Management platforms
- Custom app development
- Travel and roaming
- Stipends and taxes
- Support
- Revisit these calculators in Phase 2. Use the TCO calculator when considering different approaches to mobility and end-user computing.
Insert the results into your End-User Computing Strategy Template.
Download the HAM Budgeting Tool.
Download the Mobile Strategy TCO Calculator.
Step 1.2
Perform a User Group Analysis
Activities
1.2.1 Organize roles based on how they work
1.2.2 Organize users into groups
1.2.3 Document the current offerings
1.2.4 Brainstorm pain points and desired gains for each user group
This step requires the following inputs:
- List of roles and technologies
- User feedback
- List of personas
This step involves the following participants:
- End-User Computing Team
- IT Leadership
- End-User Computing Manager
Outcomes of this step
- List of user groups and use cases for each group
- List of current offerings for each user group
- Value analysis for each user group
Gather the information you need
Use the Application Portfolio Assessment to run a relationship survey.
Dive deeper with the blueprint Improve Requirements Gathering.
List of Roles and Technology
Organization chart: Consult with HR or department leaders to provide a list of the different roles that exist in each department.
Identity access management tools: You can consult tools like Active Directory, but only if the data is clean.
Apps and devices used: Run a report from your endpoint management tool to see what devices and apps are used by one another. Supplement this report with a report from a network management tool to identify software as a service that are in use and/or consult with department leaders.
User Feedback
Relationship surveys: Tools like the End-User Application Satisfaction Diagnostic allow you to assess overall satisfaction with IT.
Focus groups and interviews: Gather unstructured feedback from users about their apps and devices.
User shadowing: Observe people as they use technology to identify improvement opportunities (e.g. shadow meetings, review video call recordings).
Ticket data: Identify apps or systems that users submit the most incidents about as well as high-volume requests that could be automated.
1.2.1 Organize roles based on how they work
Start by organizing roles into categories based on where they work and how they interact with information.
- Define categories of where people work. Examples include:
- In office, at home, at client sites
- Stationary, sometimes mobile, always mobile
- Always in same location, sometimes in different locations, always in different locations within a site, mobile between sites
- Define categories of how people interact with information. Examples include:
- Reads information, reads and writes information, creates information
- Cases, projects, relationships
- Build a matrix. Use the location categories on one axis and the interaction categories on the other axis.
- Place unique job roles on the matrix. Review each functional group’s organizational chart. It is okay if you don’t fill every spot. See the diagram on this page for an example.
| Always Works in the Same Location | Sometimes Works in Different Locations | Always Works in Different Locations | |
|---|---|---|---|
| Predominantly Reads Information |
|
||
| Reads and Writes Information |
|
|
|
| Predominantly Creates Information |
|
1.2.2 Organize users into groups
Populate a user group worksheet for each in-scope group.
- Within each quadrant, group similar roles together into “User Groups.” Consider similarities such as:
- Applications they use
- Data and files with which they interact
- Business capabilities they support
- Document their high-level profile:
- Where they work
- Sensitivity of data they access
- Current device and app entitlements
- Document the resulting user groups. Record each user group on a separate worksheet in the User Group Analysis Workbook.
Download the User Group Analysis Workbook.
1.2.3 Document the current offerings
For each user group, document:
- Primary and secondary computing devices: Their most frequently used computing devices.
- Acceptable use: Whether corporate-issued devices are personally enabled.
- BYOD: Whether this persona is authorized to use their personal devices.
- Standard equipment provided: Equipment that is offered to everyone in this persona.
- Additional devices and equipment offered: Equipment that is offered to a subset of this user group. These items can include more prestigious computers, additional monitors, and office equipment for users allowed to work remotely. This category can include items that require approval from budget owners.
- Top apps: What apps are most commonly used by this user group? What common nonstandard apps are used by this user group?
Standardize the nonstandard
When users such as VIP users want more than the standard offering, have a more prestigious option available. This approach will help you to proactively anticipate your users’ needs.
1.2.4 Brainstorm pain points and desired gains for each user group
Don’t focus only on their experiences with technology
Reference the common personas listed on the next page to help you brainstorm additional pain points and desired gains.
- Brainstorm pain points. Answer these questions for each role:
- What do people find tedious about their day-to-day jobs?
- What takes the most effort for them to do?
- What about their current toolset makes this user frustrated?
- What makes working difficult? Consider their experiences working from a home office, attending meetings virtually or in person, and working in the office.
- What challenges does that role have with each process?
- Brainstorm desired gains from their technology. Answer these questions for each role:
- For your end-user computing vision to become a reality for this persona, what outcomes or benefits are required?
- What benefits will this persona expect an end-user computing strategy to have?
- What improvements does this role desire?
- What unexpected benefits or outcomes would surprise this role?
- What would make this role’s day-to-day easier?
- What location-specific benefits are there (e.g. outcomes specific to working in the office or at home)?
Record each user group’s pain points and desired gains on their respective worksheet.
For additional questions you can ask, visit this Strategyzer blog post by Alexander Osterwalder.
Info-Tech Insight
Identify out-of-scope benefits?
If that desired gain is required for the vision to be achieved for a specific role, you have two options:
- Bring the benefit in scope. Ensure your metrics are updated.
- Bring this user group out of scope. End-user computing improvements will not be valuable to this role without that benefit.
Forcing a user group to use an unsatisfactory tool will severely undermine your chance of success, especially in the project’s early stages.
Consider these common personas when brainstorming challenges and desired gains
What unique challenges will these personas face within each of your user groups? What improvements would each of these personas expect out of an end-user computing strategy?
Early Adopters
- Like trying new ways of working and using the latest technology.
- Very comfortable solving their own issues.
- Enjoy exploring and creating new ways of handling challenges.
Late Adopters
- Prefer consistent ways of working, be it tech or business processes.
- React to tech issues with anxiety and need assistance to get issues fixed.
VIP
- Has a prestigious job and would like to use technology that communicates their status.
- Does not like to resolve their own issues.
Road Warriors
- Always on the go, running between work meetings and appointments.
- Value flexibility and want devices, apps, and tech support that can be used anywhere at any time.
Hoarders
- Want to keep all their devices, data, and apps.
- Will stall when they need to migrate devices or uninstall apps and become unresponsive any time there is a risk of losing something.
Step 1.3
Define the Vision
Activities
1.3.1 Prioritize which benefits you want to achieve
1.3.2 Identify how you will track performance
1.3.3 Craft a vision statement that demonstrates what you’re trying to create
1.3.4 Craft a mission statement for your end-user computing team
1.3.5 Define guiding principles
This step requires the following inputs:
- Goals cascade
- List of benefits
- List of critical success factors (CSFs)
This step involves the following participants:
- End-User Computing Manager
- CIO
- Help Desk Manager
- Infrastructure Manager
Outcomes of this step
- End-User computing KPIs and metrics
- Vision statement
- Mission statement
1.3.1 Prioritize which benefits you want to achieve
Use the MoSCoW sorting technique
Select benefits that appear multiple times in the goals cascade from Activity 1.1.3 as well as your challenges from your current-state assessment.
- Record which benefits are “Must Haves.” Select benefits that are most important to your highest-priority stakeholders.
- Record which benefits are “Should Haves.” These benefits are important but not critical.
- Record which benefits are “Could Haves.” These are low-priority benefits.
- Record the remaining benefits under “Won’t Have.” These benefits are out-of-scope but can be revisited in the future.
Record the output in your End-User Computing Strategy Template under “Benefit Prioritization” in the “Vision and Desired Benefits” section.
Sample output:
| Must Have | Should Have | Could Have | Won't Have |
|---|---|---|---|
|
|
|
|
1.3.2 Identify how you will track performance
- List each unique high-priority benefit from Activity 1.3.1 as a critical success factor (CSF).
- For each CSF, identify key performance indicators (KPIs) that you can use to track how well you’re progressing on the CSF.
- Articulate that KPI as a SMART goal (specific, measurable, achievable, realistic, and timebound).
- For each KPI, identify the metrics you will use to calculate it.
- Identify how and when you will:
- Capture the current state of these metrics.
- Update changes to the metrics.
- Re-evaluate the CSFs.
- Communicate the progress to the project team and to stakeholders.
Record this information in your End-User Computing Strategy Template.
Sample output:
| Critical Success Factor | Key Performance Indicator | Metrics |
|---|---|---|
| Improve remote worker productivity | Increase employee engagement by 10% in two years |
|
| Integrate relevant information sources into one spot for sales | Integrate three information sources that will be useful to sales in one year |
|
| Reduce real-estate costs | Reduce office space by 50% in two cities over three years |
|
| Securely deliver all apps, information, and data to any device, anywhere, at any time | Build the apps and information sources into a digital workspace for three business processes over one year |
|
1.3.3 Craft a vision statement that demonstrates what you’re trying to create
The vision statement communicates a desired future state of the IT organization. The statement is expressed in the present tense. It seeks to articulate the desired role of IT and how IT will be perceived.
Strong IT vision statements have the following characteristics:
- Describes a desired future
- Focuses on ends, not means
- Communicates promise
- Is:
- Concise; no unnecessary words
- Compelling
- Achievable
- Inspirational
- Memorable
Sample IT Vision Statements:
- To support an exceptional employee experience by providing best-in-class end-user devices.
- Securely enable access to corporate apps and data from anywhere, at any time, on any device.
- Enable business and digital transformation through secure and powerful virtualization technology.
- IT is a cohesive, proactive, and disciplined team that delivers innovative technology solutions while demonstrating a strong customer-oriented mindset.
1.3.4 Craft a mission statement for your end-user computing team
The IT mission statement specifies the function’s purpose or reason for being. The mission should guide each day’s activities and decisions. The mission statement should use simple and concise terminology and speak loudly and clearly, generating enthusiasm for the organization.
Strong IT mission statements have the following characteristics:
- Articulate the IT function’s purpose and reason for existence
- Describe what the IT function does to achieve its vision
- Define the customers of the IT function
- Can be described as:
- Compelling
- Easy to grasp
- Sharply focused
- Inspirational
- Memorable
- Concise
Sample IT Mission Statements:
- To provide infrastructure, support, and innovation in the delivery of secure, enterprise-grade information technology products and services that enable and empower the workforce at [Company Name].
- To help fulfill organizational goals, the IT department is committed to empowering business stakeholders with technology and services that facilitate effective processes, collaboration, and communication.
- The mission of the information technology (IT) department is to build a solid, comprehensive technology infrastructure; to maintain an efficient, effective operations environment; and to deliver high-quality, timely services that support the business goals and objectives of [Company Name].
- The IT group is customer-centered and driven by its commitment to management and staff. It oversees services in computing, telecommunications, networking, administrative computing, and technology training.
1.3.5 Define guiding principles
Select principles that align with your stakeholders’ goals and objectives
Use these examples as a starting point:
| IT Principle Name | IT Principle Statement |
|---|---|
| 1. Enterprise value focus | We aim to provide maximum long-term benefits to the enterprise as a whole while optimizing total costs of ownership and risks. |
| 2. Fit for purpose | We maintain capability levels and create solutions that are fit for purpose without over-engineering them. |
| 3. Simplicity | We choose the simplest solutions and aim to reduce operational complexity of the enterprise. |
| 4. Reuse > buy > build | We maximize reuse of existing assets. If we can’t reuse, we procure externally. As a last resort, we build custom solutions. |
| 5. Managed data | We handle data creation, modification, and use enterprise-wide in compliance with our data governance policy. |
| 6. Controlled technical diversity | We control the variety of technology platforms we use. |
| 7. Managed security | We manage, support, and assist in the implementation of security enterprise-wide in collaboration with our security governance team. |
| 8. Compliance to laws and regulations | We operate in compliance with all applicable laws and regulations. |
| 9. Innovation | We seek innovative ways to use technology for business advantage. |
| 10. Customer centricity | We deliver best experiences to our end users by aligning to customer service best practices. |
Phase 2
Define the Offering
Set the Direction
1.1 Identify Desired Benefits
1.2 Perform a User Group Analysis
1.3 Define the Vision
Define the Offering
2.1 Define the Standard Offerings
2.2 Outline Supporting Services
2.3 Define Governance and Policies
Build the Roadmap
3.1 Develop Initiatives
This phase will walk you through the following activities:
- Defining standard device entitlements and provisioning models for end-user devices and equipment
- Shifting end-user computing support left
- Identifying policy gaps
This phase involves the following participants:
- End-User Computing Team
- IT Leadership
Step 2.1
Define the Standard Offerings
Activities
2.1.1 Identify the provisioning models for each user group
2.1.2 Define the standard device offerings
2.1.3 Document each user group’s entitlements
This step requires the following inputs:
- Standard End-User Entitlements and Offerings Template
- List of persona groups
- Primary computing devices
- Secondary computing devices
- Supporting operating systems
- Applications and office equipment
This step involves the following participants:
- End-User Computing Manager
- CIO
- Help Desk Manager
- Infrastructure Manager
Outcomes of this step
- End-user device entitlements and offerings standard
This step will walk you through defining standard offerings
You will define the base offering for all users in each user group as well as additional items that users can request (but that require additional approvals).
- Primary Computing Device
- The main device used by a worker to complete their job (e.g. laptop for knowledge workers, kiosk or shared tablet for frontline workers).
- Secondary Computing Devices
- Additional devices that supports a worker (e.g. a smartphone, tablet, personal computer).
- Provisioning Models
- Whether the equipment is corporate-issued versus personally owned and whether personal use of corporate resources is allowed.
- Apps
- The software used by the worker. Apps can be locally installed, cloud-based (e.g. SaaS), and/or virtualized and running remotely.
- Peripherals
- Additional equipment provisioned to the end user (e.g. monitors, docking station, mice, keyboards).
There is always a challenge of determining who gets what and when
The goal is balancing cost, risk, and employee engagement
The right balance will be different for every organization
- IT can’t always say no to new ideas from the business. For example, if the organization wants to adopt Macs, rather than resisting IT should focus on identifying how Macs can be safely implemented.
- Smartphones may not be necessary for a job, but they can be a valid employee perk. Not every employee may be entitled to the perk. There may be resentment between employees of the same level if one of the employees has a corporate-issued, business-only phone for their job function.
- The same laptop model may not work for everyone. Some employees may need more powerful computers. Some employees may want more prestigious devices. Other employees may require a suite of apps that is only available on non-Windows operating systems.
Action Item: Provide a defined set of standard options to the business to proactively address different needs.
A good end-user computing strategy will effectively balance:
- User Choice
- Risk
- Cost
Your standard offerings need to strike the right balance for your organization.
Review the End-User Computing Ideas Catalog
Compare pros and cons of computing devices and operating systems for better decision making
The catalog provides information about choices in:
- Provisioning models
- Operating systems
- Device form factors
Review the catalog to learn about items that can help your organization to achieve the desired vision from Phase 1.
As you review the catalog, think about these questions:
- What primary and secondary devices can you provide?
- What operating systems do these devices support?
- What are the provisioning models you will use, considering each model’s weaknesses and strengths?
- How can you more effectively balance user choice, risk, and cost?
Download the End-User Computing Ideas Catalog.
2.1.1 Identify the provisioning models for each user group
- Review the definitions in the End-User Computing Ideas Catalog.
- Build a table. List the major user groups along the top of the table and applications down the rows.
- Brainstorm provisioning models that will be used for primary and secondary devices for each persona group.
- Record your provisioning models in the Standard End-User Entitlements and Offerings Template.
Download the End-User Computing Ideas Catalog.
Download the Standard End-User Entitlements and Offerings Template.
| Persona | Primary Computing Device | Secondary Laptops or Computers | Smartphone | Tablet |
|---|---|---|---|---|
| Sales | COPE | BYOD | BYOD | BYOD |
| Field Sales | CYOD | BYOD | COBO | COBO |
| Customer Service | COBO | None | None | None |
| Knowledge Worker | COPE | BYOD | BYOD | BYOD |
| App Dev | CYOPED | None | CYOD | CYOD |
| VIP | CYOPED | CYOPED | CYOPE | BYOD |
Identify multiple device options
Offer standard, power, and prestigious offerings
Prioritize offering models and align them with your user groups.
- Standard device: This offering will work for most end users.
- Power device: This offering will provide additional RAM, processor speed, storage, etc., for users that require it. It is usually offered as an additional option that requires approval.
- Prestigious device: This offering will be provided to VIP users.
- Portable device: This offering is for employees within a user group that moves around more often than others. This type of offering is optional – consider having a separate user group for these users that get a more portable laptop as their standard device.
Standardize the nonstandard
When users such as VIP users want more than the standard offering, have a more prestigious option ready to offer. This approach will help you to proactively anticipate your users’ needs.
Who approves?
Generally, if it is a supported device, then the budget owner determines whether to allow the user to receive a more powerful or more prestigious device.
This decision can be based on factors such as:
- Business need – does the user need the device to do their job?
- Perk or benefit – is the device being offered to the end user as a means of increasing their engagement?
If IT gets this answer wrong, then it can result in shadow IT
Document your answer in the Device Entitlement Policy Template.
2.1.2 Define the standard device offerings
Consider all devices and their supporting operating systems.
- On a flip chart or whiteboard, build a matrix of the supported form factors and operating systems.
- For each cell, document the supported vendor and device model.
- Identify where you will provide additional options.
| Windows | Mac OS | iOS | Android | |
|---|---|---|---|---|
| Laptops | Lenovo T15 Gen 2 | MacBook Pro 14” | N/A | N/A |
| Power Laptops | Lenovo ThinkPad X1 Carbon | MacBook Pro 16” | N/A | N/A |
| Prestigious Laptops | Lenovo ThinkPad X1 Yoga Gen 6 | MacBook Pro 16” | N/A | N/A |
| Tablets | Microsoft Surface | N/A | iPad Pro | Samsung Galaxy Tab |
| Smartphones | N/A | N/A | iPhone 13 | Samsung Galaxy S21 |
2.1.3 Document each user groups’ entitlements
Not every persona needs to be entitled to every supported option
Use the Standard End-User Entitlements and Offerings Template as a starting point.
- Create a separate section in the document for each persona. Start by documenting the provisioning models for each type of device.
- Record the standard offering provided to members of each persona as well as additional items that can be provided with approval. Record this information for:
- Primary computing devices
- Secondary computing devices
- Optional: Document additional items that will be provided to members of each persona as well as additional items they can request, such as:
- Apps
- Office equipment
Download the Standard End-User Entitlements and Offerings Template.
Step 2.2
Outline Supporting Services
Activities
2.2.1 Review device management tools and capabilities
2.2.2 Identify common incidents and requests for devices
2.2.3 Record how you want to shift resolution
2.2.4 Define which IT groups are involved in supporting practices
Define the Offering
This step requires the following inputs:
- Standard End-User Entitlements and Offerings Template
- List of supporting devices
- Common incidents and requests
- List of supporting practices
This step involves the following participants:
- End-User Computing Manager
- CIO
- Help Desk Manager
- Infrastructure Manager
Outcomes of this step
- List of IT groups who are involved in supporting devices
- Responsibilities of each group for requests and incidents
2.2.1 Review device management tools and capabilities
Document the tools that you use to manage each OS and identify gaps
If there are different approaches to managing the same OS (e.g. Windows devices that are co-managed versus Windows devices that are only managed by Intune), then list those approaches on separate rows.
| Provision | Protect from loss/theft | Deploy/update apps | Backup & protect | Protect from injections | Complies with policies | Track | Decommission | |
|---|---|---|---|---|---|---|---|---|
| Windows 10 & 11 (co-managed) | Autopilot | Gap | ConfigMgr | Gap | Windows Security | ConfigMgr | ConfigMgr Intune | Intune and Autopilot |
| Windows 10 & 11 (Intune) | Autopilot | Intune (remote wipe) | Intune | OneDrive for Business | Windows Security | Microsoft Advanced Threat Protection | Intune | Intune and Autopilot |
| Mac OS | Jamf Pro | Intune (remote wipe) | Jamf Pro | OneDrive for Business | Gap | Jamf Pro | Intune | Jamf Pro |
Document the results on the “IT Management Tools” slide in the “IT Support” section of your End-User Computing Strategy Template.
2.2.2 Identify common incidents and requests for devices
Analyze your service desk ticket data. Look for the following information:
- The most common incidents and service requests around end-user devices and business apps
- Incident categories and service requests that almost always involve escalations
Record the level at which these tickets can be resolved today. Ensure you include these groups:
- Tier 0 (i.e. end-user self-service)
- Tier 1 (i.e. user’s first point of contact at the service desk)
- Desk-side support and field-support groups
- End-user computing specialist teams (e.g. desktop engineering, mobile device management teams)
- Other specialist teams (e.g. security, enterprise applications, DevOps)
Record the desired state. For each incident and request, to where do you want to shift resolution?
Record this chart on the “Current State of IT Support” slide in the “IT Support” section of your End-User Computing Strategy Template.
| Most Common Incidents & Requests | Self-Service | Service Desk Tier 1 | Desk-Side or Field Support | End-User Computing |
|---|---|---|---|---|
| Connect/fix a printer | X | |||
| Web conferencing issue | X | |||
| Bluetooth issues | X | |||
| Outlook issues | X | |||
| Install standard app | X | |||
| Install app requiring approval | X | |||
| Install nonstandard app | X | |||
| Enroll personal iOS/Android device | X | |||
| Enroll personal Mac/Windows computer | X | |||
| Perform a factory reset on a lost or stolen device | X | |||
| Unenroll device | X |
2.2.3 Record how you want to shift resolution
Identify opportunities to improve self-service and first contact resolution.
Starting with the chart you created in Activity 2.2.2, record the desired state. For each incident and request, to where do you want to shift resolution?
- Identify quick wins. Where will it take low effort to shift resolution? Denote these items with a “QW” for quick win.
- Identify high-value, high-effort shifts. Where do you want to prioritize shifting resolution? Base this decision on the desired benefits, guiding principles, and vision statement built in Phase 1. Denote these items with an “H” for high.
- Identify low-value areas. Where would shifting provide low value to end users and/or would have low alignment to the benefits identified in Phase 1? Denote these items with an “L” for low.
- Identify where no shift can occur. Some items cannot be shifted to self-service or to tier 1 due to governance considerations, security factors, or technical complexity. Denote these items with an “OoS” for out of scope.
Use the “Opportunities to Provide Self-Service and Articles” and “Desired State” slides in the “IT Support” section of your End-User Computing Strategy Template to document quick wins and high-value, high-effort shifts.
| Most Common Incidents & Requests | Self-Service | Service Desk Tier 1 | Desk-Side or Field Support | End-User Computing |
|---|---|---|---|---|
| Connect/fix a printer | H | QW | X | |
| Web conferencing issue | H | X | ||
| Bluetooth issues | L | X | ||
| Outlook issues | H | H | X | |
| Install standard app | X | |||
| Install app requiring approval | H | X | ||
| Install nonstandard app | OoS | X | ||
| Enroll personal iOS/Android device | QW | QW | X | |
| Enroll personal Mac/Windows computer | QW | QW | X | |
| Perform a factory reset on a lost or stolen device | QW | QW | X | |
| Unenroll device | QW | QW | X |
2.2.4 Define which IT groups are involved in supporting practices
Repeat activities 2.2.2 and 2.2.3 with the following list of tasks
IT Asset Management
- Purchasing devices
- Purchasing software licenses
- Imaging devices
- Deploying devices
- Deploying software
- Recovering devices
- Recovering software
Release Management
- Testing patches
- Testing app updates
- Testing OS updates
- User acceptance testing
Managing Service Catalogs
- Defining standard device offerings
- Defining standard software offerings
- Defining device and software entitlements
- Updating published catalog entries
Knowledge Management
- Writing internal KB articles
- Writing user-facing articles
- Training specialists
- Training service desk agents
- Training users
Portfolio Management
- Prioritizing app upgrades or migrations
- Prioritizing OS migrations
- Prioritizing end-user computing projects
Step 2.3
Define Governance and Policies
Activities
2.3.1 Answer these organizational policy questions
2.3.2 Answer these security policy questions
Define the Offering
This step requires the following inputs:
- List of supporting devices
- List of persona groups
- List of use cases
This step involves the following participants:
- End-User Computing Manager
- CIO
- Help Desk Manager
- Infrastructure Manager
Outcomes of this step
- End-user computing organizational and security policies
Focus on organizational policies and enforcement
Policies set expectations and limits for mobile employees
Enforcement refers to settings on the devices, management and security tools, and process steps.
- Policies define what should and should not be done with user-facing technology. These policies define expectations about user and IT behavior.
- Enforcement ensures that policies are followed. User policies must often be enforced through human intervention, while technology policies are often enforced directly through infrastructure before any people get involved.
Use the “Policies” section in the End-User Computing Strategy Template to document the answers in this section. Activities 2.3.2 and 2.3.3 present links to policy templates. Use these templates to help address any gaps in your current policy suite.
2.3.1 Answer these organizational policy questions
Identify if there are different expectations for certain user groups, where exceptions are allowed, and how these policies will be enforced.
Entitlements
- Who is entitled to receive and use prestigious computers?
- Who is entitled to receive and use a smartphone?
- What users are entitled to a stipend for personal device use?
Personal Device Use
- What use cases are supported and are not supported on personal devices?
- What level of visibility and control does IT need over personal devices?
Acceptable Use
- Are people allowed to use corporate resources for personal use?
- What are the guidelines around personal use?
- Are users allowed to install personal apps on their corporate-issued computers and/or mobile devices?
Purchasing and Reimbursement
- Who is allowed to purchase devices? Apps?
- When can users file a reimbursement request?
Employee Monitoring
- What user information is monitored?
- When can that information be used and when can it not be used?
Use the “Policies” section of the End-User Computing Strategy Template to document these answers.
Identify organizational policy gaps
Use these templates as a starting point
Entitlements
Download the Mobile Device Connectivity & Allowance Policy template.
Purchasing & Reimbursement
Download the Purchasing Policy template.
Download the Mobile Device Reimbursement Policy template.
Download the Mobile Device Reimbursement Agreement template.
Acceptable Use
Download the General Security – User Acceptable Use Policy template.
Personal Device Use
Download the BYOD Acceptable Use Policy template.
Download the Mobile Device Remote Wipe Waiver template.
Employee Monitoring
Download the General Security – User Acceptable Use Policy template.
Visit the Reduce and Manage Your Organization’s Insider Threat Risk blueprint to address this gap.
2.3.2 Answer these security policy questions
Identify if there are different expectations for certain user groups, where exceptions are allowed, and how these policies will be enforced.
Use Cases
- What data and use cases are subject to stricter security measures?
- Are certain use cases or data prohibited on personal devices?
- Are there restrictions around where certain use cases are performed and by whom?
Patching
- Are users expected to apply OS and app updates and patches? Or does IT automate patching?
Physical Security
- What does the user need to do to secure their equipment?
- If a device is lost or stolen, who does the user contact to report the lost or stolen device?
Cybersecurity
- How will IT enforce security configuration baselines?
- What does the user need to do (or not do) to secure their device?
- Are certain users allowed to have local admin rights?
- What happens when a device doesn’t comply with the required security configuration baseline?
Use the “Policies” section of the End-User Computing Strategy Template to document these answers.
Identify security policy gaps
Use these templates as a starting point
Use Cases
Download the General Security – User Acceptable Use Policy template.
Visit the Discover and Classify Your Data blueprint to address this gap.
Patching
Download the General Security – User Acceptable Use Policy template.
Physical and Cyber Security
Download the General Security – User Acceptable Use Policy template.
Visit the Develop and Deploy Security Policies blueprint to address this gap.
For help defining your own security configuration baselines for each operating system, reference best practice documentation such as:
National Institute of Standards and Technology’s National Checklist Program.
Center for Internet Security’s solutions.
Microsoft’s security baseline settings for Windows 10 and 11 Configuration Service Providers.
Phase 3
Build the Roadmap
Set the Direction
1.1 Identify Desired Benefits
1.2 Perform a User Group Analysis
1.3 Define the Vision
Define the Offering
2.1 Define the Standard Offerings
2.2 Outline Supporting Services
2.3 Define Governance and Policies
Build the Roadmap
3.1 Develop Initiatives
This phase will walk you through the following activities:
- Defining initiatives for each EUC domain
- Building a customer journey map for any end-user computing migrations
- Building a roadmap for EUC initiatives
This phase involves the following participants:
- End-User Computing Team
Step 3.1
Develop Initiatives
Activities
3.1.1 Identify initiatives for each EUC practice
3.1.2 Build out the user’s migration journey map
3.1.3 Build out a list of initiatives
Build the Roadmap
This step requires the following inputs:
- User group workbook
- Migration initiatives
This step involves the following participants:
- Infrastructure Director
- Head of End-User Computing
- End-User Computing Team
- Project Manager (if applicable)
Outcomes of this step
- End-user computing roadmap
- Migration plan
3.1.1 Identify the gaps in each EUC area
Build a high-level profile of the changes you want to make
For each of the five areas, build a profile for the changes you want to implement. Record:
- The owner of the area
- The objective that you want to accomplish
- The desired benefits from focusing on that area
- Any dependencies to the work
- Risks that can cause the objective and benefits to not be achieved
Identify the initiatives involved in each area.
Document these profiles and initiatives in the “Roadmap” section of your End-User Computing Strategy Template.
- Devices
- Corporate-issued devices
- Standard offerings
- User Support
- Self-service
- Tier 1 support
- Use Cases
- Providing value
- Business apps
- Policy & Governance
- Personal device use
- IT policy
- Fitness for Use
- Securing devices
- Patching
Your initiatives may require a user migration
Plan the user’s migration journey
Consider each user group’s and each persona’s unique needs and challenges throughout the migration.
- Preparing to migrate: The user may need to schedule the migration with IT and back up files.
- Migrating: IT executes the migration (e.g. updates the OS, changes management tools).
- Getting assistance: When a user experiences an error during the migration, how will they get help from IT?
- Post-migration: How will IT and the user know that the migration was successful one week later?
Understand the three migration approaches
Online
Users execute the migrate on their own (e.g. Microsoft’s consumer migration to Windows 10).
In person
Users come in person, select a device, and perform the migration with a specialist. If the device needs support, they return to the same place (e.g. buying a computer from a store).
Hybrid
Users select a device. When the device is ready, they can schedule time to pick up the device and perform the migration with a specialist (e.g. purchasing an iPhone in advance from Apple’s website with in-store pick-up).
Be prepared to support remotely
Migrations to the new tool may fail. IT should check in with the user to confirm that the device successfully made the migration.
3.1.2 Build out the user’s migration journey map
Contemplate a roadmap to plan for end-user computing initiatives
- As a group, brainstorm migration initiatives.
- For each of the four phases, identify:
- User activities: actions we need the user to do
- IT activities: actions and processes that IT will perform internally
- User touchpoints with IT: how the user will interact with the IT group
- Opportunities: ideas for how IT can provide additional value to the end user in this phase.
- Use the example in the End-User Computing Strategy Template as a starting point.
Download the End-User Computing Strategy Template.
Embed requirements gathering throughout your roadmap
Use a combination of surveys, focus groups, and interviews
You’re doing more than eliciting opinions – you’re performing organizational change management.
- Use surveys to profile the demand for specific requirements. When a project is announced, develop surveys to gauge what users consider must-have, should-have, and could-have requirements.
- Interviews should be used with high-value targets. Those who receive one-on-one face time can help generate good requirements and allow for effective communication around requirements.
- Focus groups are used to get input from multiple people in a similar role. This format allows you to ask a few open-ended questions to groups of about five people.
The benefits of interviews and focus groups:
- Foster direct engagement: IT is able to hear directly from stakeholders about what they are looking to do with a solution and the level of functionality that they expect from it.
- Offer greater detail: With interviews, greater insight can be gained by leveraging information that traditional surveys wouldn’t uncover. Face-to-face interactions provide thorough answers and context that helps inform requirements.
- Remove ambiguity: Face-to-face interactions allow opportunities to follow up on ambiguous answers. Clarify what stakeholders are looking for and expect in a project.
- Enable stakeholder management: Interviews are a direct line of communication with project stakeholders. They provide input and insight and help to maintain alignment, plan next steps, and increase awareness within the IT organization.
Activity instructions:
- Early requirements ideation: Identify who you want to interview through one-on-one meetings and focus groups.
- Requirements validation and prioritization: Identify which user groups you plan to survey and when.
- Usability testing: Plan to include usability testing during each phase. Build it into your release practices.
3.1.3 Build out a list of initiatives
Download a copy of the Roadmap Tool
On tab “1. Setup”:
- Update category 1 to be all the EUC areas (i.e. Devices, User Support).
- Update category 2 and category 3 with meaningful items (e.g. operating system, device model, persona group).
Use tab “2. Data Entry” to record your list of initiatives.
- Each initiative should have its own row. Write a high-level summary under “Roadmap Item” and include more detail under “Description and Rationale.”
- Enter each initiative’s effort, priority, and timeline for beginning. These are mandatory fields for tab “3. Roadmap” to work properly.
Use tab “3. Roadmap” to visualize your data. You will have to press “Refresh All” under Data in the ribbon for the PivotChart to update.
Copy the roadmap visual on tab “3. Roadmap” into your End-User Computing Strategy Template. You can also copy the list of initiatives over into the document.
Download the Roadmap Tool.
Summary of Accomplishment
Problem Solved
You built a strategy to improve the balance between user enablement, risk mitigation, and cost optimization. Throughout the blueprint, you identified opportunities to provide additional value to end users and stakeholders during these activities:
- Goals cascade
- User group analysis
- Definition of standard device types and platforms
- IT support shift-left analysis
- Policy gap analysis
- Roadmapping
If you would like additional support, have our analysts guide you through other phases as part of an Info-Tech workshop.
Contact your account representative for more information.
workshops@infotech.com
1-888-670-8889
Additional Support
If you would like additional support, have our analysts guide you through other phases as part of an Info-Tech Workshop.
Contact your account representative for more information.
workshops@infotech.com 1-888-670-8889
To accelerate this project, engage your IT team in an Info-Tech workshop with an Info-Tech analyst team.
Info-Tech analysts will join you and your team at your location or welcome you to Info-Tech’s historic Toronto office to participate in an innovative onsite workshop.
The following are sample activities that will be conducted by Info-Tech analysts with your team:
Identify User Groups
Identify each user group based on the business processes, tasks, and applications they use.
Define Standard Device Offerings
Record your provisioning models for each user group and the primary and secondary devices, apps, and peripherals that each group receives.
Related Info-Tech Research
Simplify Remote Deployment With Zero-Touch Provisioning
This project helps you align your zero-touch approach with stakeholder priorities and larger IT strategies. You will be able to build your zero-touch provisioning and patching plan from both the asset lifecycle and the end-user perspective to create a holistic approach that emphasizes customer service. Tailor deployment plans to more easily scope and resource deployment projects.
Implement Hardware Asset Management
This project will help you analyze the current state of your HAM program, define assets that will need to be managed, and build and involve the ITAM team from the beginning to help embed the change. It will also help you define standard policies, processes, and procedures for each stage of the hardware asset lifecycle, from procurement through to disposal.
Govern Office 365
This project will help you conduct a goals exercise and capability assessment for Office 365. You will be able to refine governance objectives, build out controls, formalize governance, build out one pagers, and finalize a communication plan.
Research Contributors and Experts
- Steve Fox, Deputy IT Director, Virginia State Corporation Commission
- Mazen Joukhadar, TransForm Shared Service Organization
- Nathan Schlaud, PMO Senior Director, RPC Inc.
- Rebecca Mountjoy, Infrastructure Systems Manager, BlueScope Buildings
- DJ Robins, Director of Information Technology, Mohawk MedBuy
- Jason Jenkins, Tech. Specialist, Michal Baker Corp.
- Brad Wells, IT Infrastructure Solutions Architect, London Police Service
- Danelle Peddell, Director, Project Management Office, Emco Corporation
- John Annand, Principal Research Director, Info-Tech Research Group
- Allison Kinnaird, Research Director and Research Lead, Info-Tech Research Group
- Sandi Conrad, Principal Research Director, Info-Tech Research Group
- Andrew Kum-Seun, Senior Research Analyst, Info-Tech Research Group
- Mark Tauschek, Vice President IT Infrastructure & Operations Research, Info-Tech Research Group
A special thank-you to 6 anonymous contributors
Bibliography
“2020 Annual Report and Proxy.” Citrix, 2020. Accessed Oct. 2021.
“2021 BYOD Security Report.” Cybersecurity Insiders, 2021. Web.
Anderson, Arabella. “12 Remote Work Statistics to Know in 2022.” NorthOne, 2021. Accessed Oct. 2021.
Bayes, Scarlett. “ITSM: 2021 & Beyond.” Service Desk Institute, 14 April 2021, p. 14. Web.
Belton, Padraig. “Intel: Chip shortage will extend to at least 2023.” Light Reading, 22 Oct. 2021. Web.
Beroe Inc. “Demand for PC Components Saw a Surge Due to COVID-19, Says Beroe Inc.” Cision PR Newswire, 2 Sept. 2021. Web.
Devaraj, Vivekananthan. “Reference Architecture: Remote PC Access.” Citrix, 2021. Accessed Aug. 2021.
“Elements of the Project Charter and Project Scope Statement.” A Guide to PMBOK, 7th edition, PMI, 2021. Accessed Sept. 2021.
Elliott, Christopher. “This Is How The Pandemic Improved Customer Service.” Forbes, 2021. Accessed Oct. 2021.
“Enable TMP 2.0 on your PC.” Microsoft, Support, Aug. 2021. Web.
“End User Computing Trends to Look Out for in 2021.” Stratodesk, 30 Oct. 2020. Accessed September 2021.
“Global State of Customer Service: The Transformation of Customer Service from 2015 to Present Day.” Microsoft, 2019. Web.
Goodman, Elizabeth et al. “Observing the User Experience” A Practitioner's Guide to User Research, 2nd edition. Elsevier, 2012. Accessed Sept. 2021.
Govindarajulu, Chittibabu. “An Instrument to Classify End-Users Based On the User Cube” Informing Science, June 2002. Accessed September 2021.
Griffith, Eric. “Remote Employees to Bosses: Our PCs Suck!” PCMag, 11 Oct. 2021. Web.
Hutchings, Jeffrey D., and Craig A. de Ridder. “Impact of Remote Working on End User Computing Solutions and Services.” Pillsbury, 2021. Accessed Sept. 2021
“ITIL4 Create, Deliver, and Support.” Axelos, 2020. Accessed Sept. 2021.
“ITIL4 Drive Stakeholder Value” Axelos, 2020. Accessed Sept. 2021.
Mcbride, Neil, and Trevor Wood-Harper. “Towards User-Oriented Control of End-User Computing in Large Organizations” Journal of Organizational and End User Computing, vol. 14, no. 1, pp. 33-41, 2002. Accessed September 2021.
““Microsoft Endpoint Configuration Manager Documentation.” Microsoft Docs, Microsoft, 2021. Accessed Sept. 2021.
“Microsoft Intune documentation.” Microsoft Docs, Microsoft. Accessed Sept. 2021.
“Mobile Cellular Subscriptions (per 100 People).” The World Bank, International Telecommunication Union (ITU) World Telecommunication/ICT Indicators Database, 2020. Web.
Morgan, Jacob. “The Employee Experience Advantage: How to Win the War for Talent by Giving Employees the Workspaces they Want, the Tools they Need, and a Culture They Can Celebrate.” Wiley, 2017. Accessed Sept. 2021.
Murphy, Anna. “How the pandemic has changed customer support forever.” Intercom, 2021. Accessed Sept. 2021.
“Operating System Market Share Worldwide, Jan 2021-Jan 2022.” StatCounter GlobalStats, 2022. Web.
“Operating System Market Share Worldwide, Jan-Dec 2011.” StatCounter GlobalStats, 2012. Web.
Pereira, Karla Susiane, et al. “A Taxonomy to Classify Risk End-User Profile in Interaction with the Computing Environment.” In: Tryfonas T. (eds.) Human Aspects of Information Security, Privacy, and Trust. HAS 2016. Lecture Notes in Computer Science, vol. 9750. Accessed Sept. 2021.
Perrin, Andrew. “Mobile Technology and Home Broadband 2020.” Pew Research Center, 3 June 2021. Web.
Quan-Haase, Anabel. “Technology and Society: Social Networks, Power, and Inequality” Oxford University Press, 2012. Accessed Aug. 2021.
Reed, Karin, and Joseph Allen. “Suddenly Virtual: Making Remote Meetings Work.” Wiley, 2021. Accessed Aug. 2021.
Rockart, John F., and Lauren S. Flannery. “The management of end user computing.” Communications of the ACM, vol. 26, no. 10, Oct. 1983. Accessed September 2021.
Turek, Melanie. “Employees Say Smartphones Boost Productivity by 34 Percent: Frost & Sullivan Research.” Samsung Insights, 3 Aug. 2016. Web.
Vladimirskiy, Vadim. “Windows 365 vs. Azure Virtual Desktop (AVD) – Comparing Two DaaS Products.” Nerdio, 2021. Accessed Aug. 2021.
“VMware 2021 Annual Report.” VMware, Financial Document Library, 2021. Web.
VMworld 2021, Oct. 2021.
Vogels, Emily A. “Digital divide persists even as americans with lower incomes make gains in tech adoption.” Pew Research Center, 22 June 2021. Web.
“What is End-User computing?” VMware, 2021. Accessed Aug. 2021.
“Windows 10 Home and Pro.” Microsoft, Docs, 2021. Web.
Zibreg, Christian. “Microsoft 365 Now Boasts Over 50 Million Subscribers.” MUD, 29 April 2021. Web.