Design and Implement a Business-Aligned Security Program
- You need to build a security program that enables business services and secures the technology that makes them possible.
- Building an effective, business-aligned security program requires that you coordinate many components, including technologies, processes, organizational structures, information flows, and behaviors.
- The program must prioritize the right capabilities, and support its implementation with clear accountabilities, roles, and responsibilities.
Our Advice
Critical Insight
- Common security frameworks focus on operational controls rather than business value creation, are difficult to convey to stakeholders, and provide little implementation guidance.
- A security strategy can provide a snapshot of your program, but it won’t help you modernize or transform it, or align it to meet emerging business requirements.
- There is no unique, one-size-fits-all security program. Each organization has a distinct character and profile and differs from others in several critical respects.
Impact and Result
Tailor your security program according to what makes your organization unique.
- Analyze critical design factors to determine and refine the scope of your security program and prioritize core program capabilities.
- Identify program accountabilities, roles, and responsibilities.
- Build an implementation roadmap to ensure its components work together in a systematic way to meet business requirements.
Design and Implement a Business-Aligned Security Program Research & Tools
Besides the small introduction, subscribers and consulting clients within this management domain have access to:
1. Design and Implement a Business-Aligned Security Strategy – A step-by-step guide on how to understand what makes your organization unique and design a security program with capabilities that create business value.
This storyboard will help you lay foundations for your security program that will inform future security program decisions and give your leadership team the information they need to support your success. You will evaluate design factors that make your organization unique, prioritize the security capabilities to suit, and assess the maturity of key security program components including security governance, security strategy, security architecture, service design, and service metrics.
- Design and Implement a Business-Aligned Security Program Storyboard
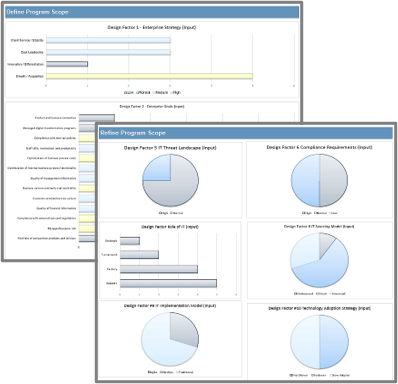
2. Security Program Design Tool – Tailor the security program to what makes your organization unique to ensure business-alignment.
Use this Excel workbook to evaluate your security program against ten key design factors. The tool will produce a goals cascade that shows the relationship between business and security goals, a prioritized list of security capabilities that align to business requirements, and a list of program accountabilities.
- Security Program Design Tool
3. Security Program Design and Implementation Plan – Assess the current state of different security program components, plan next steps, and communicate the outcome to stakeholders.
This second Excel workbook will help you conduct a gap analysis on key security program components and identify improvement initiatives. You can then use the Security Program Design and Implementation Plan to collect results from the design and implementation tools and draft a communication deck.
- Security Program Implementation Tool
- Security Program Design and Implementation Plan
Infographic

Workshop: Design and Implement a Business-Aligned Security Program
Workshops offer an easy way to accelerate your project. If you are unable to do the project yourself, and a Guided Implementation isn't enough, we offer low-cost delivery of our project workshops. We take you through every phase of your project and ensure that you have a roadmap in place to complete your project successfully.
1 Initial Security Program Design
The Purpose
Determine the initial design of your security program.
Key Benefits Achieved
An initial prioritized list of security capabilities that aligns with enterprise strategy and goals.
Activities
1.1 Review Info-Tech diagnostic results.
1.2 Identify project context.
1.3 Identify enterprise strategy.
1.4 Identify enterprise goals.
1.5 Build a goal cascade.
1.6 Assess the risk profile.
1.7 Identify IT-related issues.
1.8 Evaluate initial program design.
Outputs
Stakeholder satisfaction with program
Situation, challenges, opportunities
Initial set of prioritized security capabilities
Initial set of prioritized security capabilities
Initial set of prioritized security capabilities
Initial set of prioritized security capabilities
Initial set of prioritized security capabilities
Initial set of prioritized security capabilities
2 Refine Security Program Capabilities
The Purpose
Refine the design of your security program.
Key Benefits Achieved
A refined, prioritized list of security capabilities that reflects what makes your organization unique.
Activities
2.1 Gauge threat landscape.
2.2 Identify compliance requirements.
2.3 Categorize the role of IT.
2.4 Identify the sourcing model.
2.5 Identify the IT implementation model.
2.6 Identify the tech adoption strategy.
2.7 Refine the scope of the program.
Outputs
Refined set of prioritized security capabilities
Refined set of prioritized security capabilities
Refined set of prioritized security capabilities
Refined set of prioritized security capabilities
Refined set of prioritized security capabilities
Refined set of prioritized security capabilities
Refined set of prioritized security capabilities
3 Security Program Gap Analysis
The Purpose
Finalize security program design.
Key Benefits Achieved
Key accountabilities to support the security program
Gap analysis to produce an improvement plan
Activities
3.1 Identify program accountabilities.
3.2 Conduct program gap analysis.
3.3 Prioritize initiatives.
Outputs
Documented program accountabilities.
Security program gap analysis
Security program gap analysis
4 Roadmap and Implementation Plan
The Purpose
Create and communicate an improvement roadmap for the security program.
Key Benefits Achieved
Security program design and implementation plan to organize and communicate program improvements.
Activities
4.1 Build program roadmap
4.2 Finalize implementation plan
4.3 Sponsor check-in
Outputs
Roadmap of program improvement initiatives
Roadmap of program improvement initiatives
Communication deck for program design and implementation
Further reading
Design a Business-Aligned Security Program
Focus on business value first.
EXECUTIVE BRIEF
Analyst Perspective
Business alignment is no accident.
 |
Security leaders often tout their choice of technical security framework as the first and most important program decision they make. While the right framework can help you take a snapshot of the maturity of your program and produce a quick strategy and roadmap, it won’t help you align, modernize, or transform your program to meet emerging business requirements. Common technical security frameworks focus on operational controls rather than business services and value creation. They are difficult to convey to business stakeholders and provide little program management or implementation guidance. Focus on business value first, and the security services that enable it. Your organization has its own distinct character and profile. Understand what makes your organization unique, then design and refine the design of your security program to ensure it supports the right capabilities. Next, collaborate with stakeholders to ensure the right accountabilities, roles, and responsibilities are in place to support the implementation of the security program. |
Michel Hébert |
Executive Summary
Your Challenge |
Common Obstacles |
Info-Tech’s Approach |
|---|---|---|
|
|
Tailor your security program according to what makes your organization unique.
|
Info-Tech Insight
You are a business leader who supports business goals and mitigates risk. Focus first on business value and the security services that enable it, not security controls.
Your challenge
The need for a solid and responsive security program has never been greater.
- You need to build a security program that enables business services and secures the technology that makes them possible.
- Building an effective, business-aligned security program requires that you coordinate many components, including technologies, processes, organizational structures, information flows, and behaviors.
- The program must prioritize the right capabilities, and support its implementation with clear accountabilities, roles, and responsibilities.
- You must communicate effectively with stakeholders to describe the risks the organization faces, their likely impact on organizational goals, and how the security program will mitigate those risks and support the creation of business value.
- Ransomware is a persistent threat to organizations worldwide across all industries.
Cybercriminals deploying ransomware are evolving into a growing and sophisticated criminal ecosystem that will continue to adapt to maximize its profits.
- Critical infrastructure is increasingly at risk.
Malicious agents continue to target critical infrastructure to harm industrial processes and the customers they serve State-sponsored actors are expected to continue to target critical infrastructure to collect information through espionage, pre-position in case of future hostilities, and project state power.
- Disruptive technologies bring new threats.
Malicious actors increasingly deceive or exploit cryptocurrencies, machine learning, and artificial intelligence technologies to support their activities.
Sources: CCCS (2023), CISA (2023), ENISA (2023)
Your challenge
Most security programs are not aligned with the overall business strategy.
50% Only half of leaders are framing the impact of security threats as a business risk.
49% Less than half of leaders align security program cost and risk reduction targets with the business.
57% Most leaders still don’t regularly review security program performance of the business.
Source: Tenable, 2021
Common obstacles
Misalignment is hurting your security program and making you less influential.
Organizations with misaligned security programs have 48% more security incidents...
…and the cost of their data breaches are 40% higher than those with aligned programs.
37% of stakeholders still lack confidence in their security program.
54% of senior leaders still doubt security gets the goals of the organization.
Source: Frost & Sullivan, 2019
Source: Ponemon, 2023
Common obstacles
Common security frameworks won’t help you align your program.
- Common security frameworks focus on operational controls rather than business value creation, are difficult to convey to stakeholders, and provide little implementation guidance.
- A security strategy based on the right framework can provide a snapshot of your program, but it won’t help you modernize, transform, or align your program to meet emerging business requirements.
- The lack of guidance leads to a lack of structure in the way security services are designed and managed, which reduces service quality, increases security friction, and reduces business satisfaction.
There is no unique, one-size-fits-all security program.
- Each organization has a distinct character and profile and differs from others in several critical respects. The security program for a cloud-first, DevOps environment must emphasize different capabilities and accountabilities than one for an on-premise environment and a traditional implementation model.
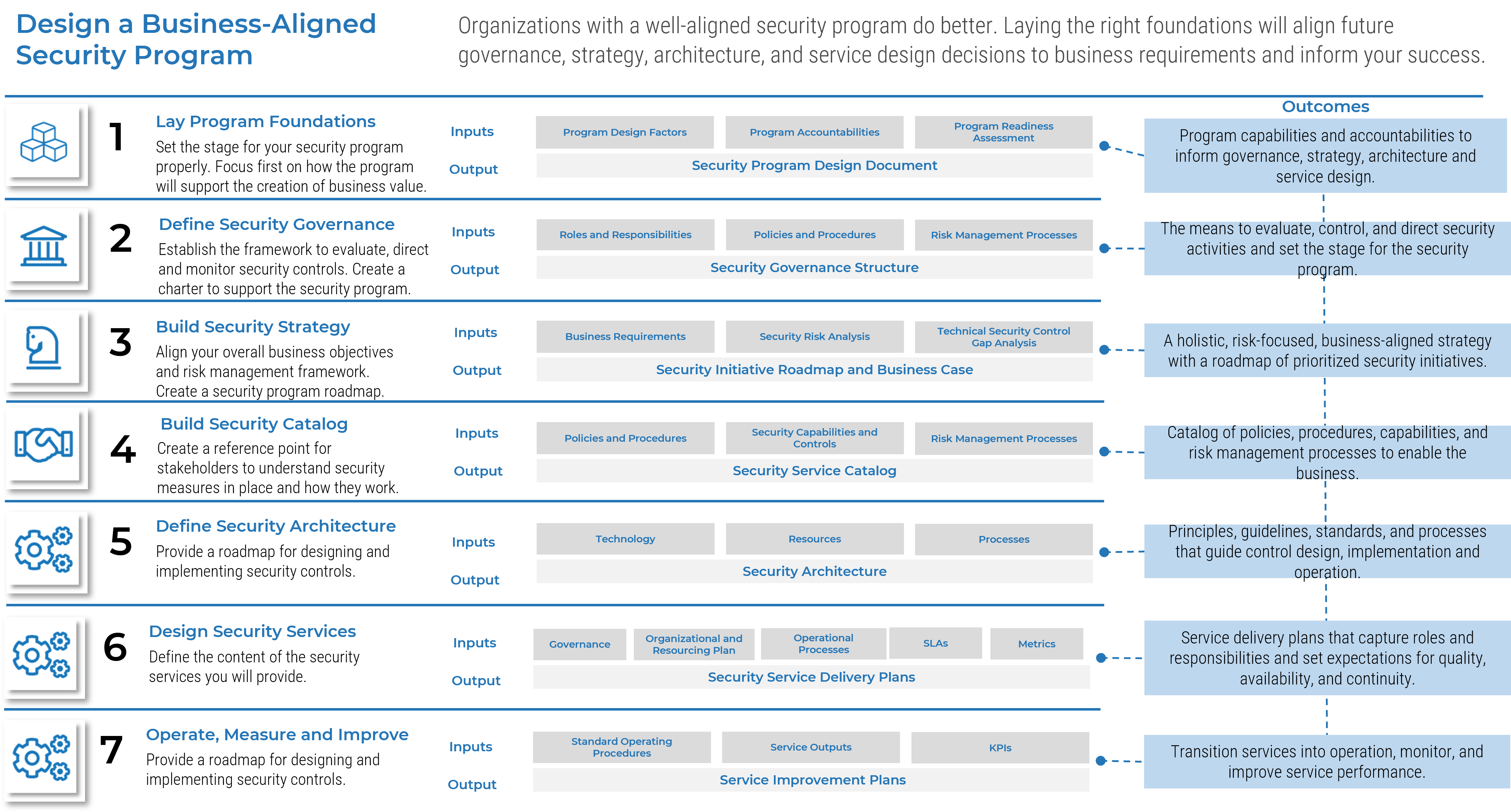
Info-Tech’s approach
You are a business leader who supports business goals and mitigates risk.
- Understand what makes your organization unique, then design and refine a security program with capabilities that create business value.
- Next, collaborate with stakeholders to ensure the right accountabilities, roles, and responsibilities are in place, and build an implementation roadmap to ensure its components work together over time.
Security needs to evolve as a business strategy.
- Laying the right foundations for your security program will inform future security program decisions and give your leadership team the information they need to support your success. You can do it in two steps:
- Evaluate the design factors that make your organization unique and prioritize the security capabilities to suit. Info-Tech’s approach is based on the design process embedded in the latest COBIT framework.
- Review the key components of your security program, including security governance, security strategy, security architecture, service design, and service metrics.
If you build it, they will come
“There's so much focus on better risk management that every leadership team in every organization wants to be part of the solution.
If you can give them good data about what things they really need to do, they will work to understand it and help you solve the problem.”
Dan Bowden, CISO, Sentara Healthcare (Tenable)
Design a Business-Aligned Security Program
Choose your own adventure
This blueprint is ideal for new CISOs and for program modernization initiatives.
1. New CISO
“I need to understand the business, prioritize core security capabilities, and identify program accountabilities quickly.”
2. Program Renewal
“The business is changing, and the threat landscape is shifting. I am concerned the program is getting stale.”
Use this blueprint to understand what makes your organization unique:
- Prioritize security capabilities.
- Identify program accountabilities.
- Plan program implementation.
If you need a deep dive into governance, move on to a security governance and management initiative.
3. Program Update
“I am happy with the fundamentals of my security program. I need to assess and improve our security posture.”
Move on to our guidance on how to Build an Information Security Strategy instead.
Info-Tech’s methodology for security program design
Define Scope of |
Refine Scope of |
Finalize Security |
|
|---|---|---|---|
Phase steps |
1.1 Identify enterprise strategy 1.2 Identify enterprise goals 1.3 Assess the risk profile 1.4 Identify IT-related issues 1.5 Define initial program design |
2.1 Gage threats and compliance 2.2 Assess IT role and sourcing 2.3 Assess IT implementation model 2.4 Assess tech adoption strategy 2.5 Refine program design |
3.1 Identify program accountabilities 3.2 Define program target state 3.3 Build program roadmap |
Phase outcomes |
|
|
|
Tools |
Insight Map
You are a business leader first and a security leader second
Technical security frameworks are static and focused on operational controls and standards. They belong in your program’s solar system but not at its center. Design your security program with business value and the security services that enable it in mind, not security controls.
There is no one-size-fits-all security program
Tailor your security program to your organization’s distinct profile to ensure the program generates value.
Lay the right foundations to increase engagement
Map out accountabilities, roles, and responsibilities to ensure the components of your security program work together over time to secure and enable business services.
If you build it, they will come
Your executive team wants to be part of the solution. If you give them reliable data for the things they really need to do, they will work to understand and help you solve the problem.
Blueprint deliverables
Info-Tech supports project and workshop activities with deliverables to help you accomplish your goals and accelerate your success.
Security Program Design Tool
Tailor the security program to what makes your organization unique to ensure alignment.
Security Program Implementation Tool
Assess the current state of different security program components and plan next steps.
SecurityProgram Design and Implementation Plan
Communicate capabilities, accountabilities, and implementation initiatives.
Key deliverable
Security Program Design and Implementation Plan
The design and implementation plan captures the key insights your work will generate, including:
- A prioritized set of security capabilities aligned to business requirements.
- Security program accountabilities.
- Security program implementation initiatives.
Blueprint benefits
IT Benefits |
Business Benefits |
|---|---|
|
|
Measure the value of using Info-Tech’s approach
Assess the effectiveness of your security program with a risk-based approach.
Deliverable |
Challenge |
|
|---|---|---|
Security Program Design |
|
|
Program Assessment and Implementation Plan |
|
|
Measured Value |
|
Measure the impact of your project
Use Info-Tech diagnostics before and after the engagement to measure your progress.
- Info-Tech diagnostics are standardized surveys that produce historical and industry trends against which to benchmark your organization.
- Run the Security Business Satisfaction and Alignment diagnostic now, and again in twelve months to assess business satisfaction with the security program and measure the impact of your program improvements.
- Reach out to your account manager or follow the link to deploy the diagnostic and measure your success. Diagnostics are included in your membership.
Inform this step with Info-Tech diagnostic results
- Info-Tech diagnostics are standardized surveys that accelerate the process of gathering and analyzing pain point data.
- Diagnostics also produce historical and industry trends against which to benchmark your organization.
- Reach out to your account manager or follow the links to deploy some or all these diagnostics to validate your assumptions. Diagnostics are included in your membership.
Governance & Management Maturity Scorecard
Understand the maturity of your security program across eight domains.
Audience: Security Manager
Security Business Satisfaction and Alignment Report
Assess the organization’s satisfaction with the security program.
Audience: Business Leaders
CIO Business Vision
Assess the organization’s satisfaction with IT services and identify relevant challenges.
Audience: Business Leaders
Executive Brief Case Study
INDUSTRY: Higher Education
SOURCE: Interview
Building a business-aligned security program
Portland Community College (PCC) is the largest post-secondary institution in Oregon and serves more than 50,000 students each year. The college has a well-established information technology program, which supports its education mission in four main campuses and several smaller centers.
PCC launched a security program modernization effort to deal with the evolving threat landscape in higher education. The CISO studied the enterprise strategy and goals and reviewed the college’s risk profile and compliance requirements. The exercise helped the organization prioritize security capabilities for the renewal effort and informed the careful assessment of technical controls in the current security program.
Results
Laying the right foundations for the security program helped the security function understand how to provide the organization with a clear report of its security posture. The CISO now reports directly to the board of directors and works with stakeholders to align cost, performance, and risk reduction objectives with the needs of the college.
The security program modernization effort prioritized several critical design factors
- Enterprise Strategy
- Enterprise Goals
- IT Risk Profile
- IT-Related Issues
- IT Threat Landscape
- Compliance Requirements
Info-Tech offers various levels of support to best suit your needs
DIY Toolkit
“Our team has already made this critical project a priority, and we have the time and capability, but some guidance along the way would be helpful.”
Guided Implementation
“Our team knows that we need to fix a process, but we need assistance to determine where to focus. Some check-ins along the way would help keep us on track.”
Workshop
“We need to hit the ground running and get this project kicked off immediately. Our team has the ability to take this over once we get a framework and strategy in place.”
Consulting
“Our team does not have the time or the knowledge to take this project on. We need assistance through the entirety of this project.”
Diagnostics and consistent frameworks used throughout all four options
Guided Implementation
What does a typical GI on this topic look like?
| Phase 1 | Phase 2 | Phase 3 |
|---|---|---|
Call #1: Call #2: |
Call #3: Call #4: |
Call #5: Call #6: |
A Guided Implementation (GI) is a series of calls with an Info-Tech analyst to help implement our best practices in your organization.
A typical GI is 4 to 6 calls over the course of 6 months.
Workshop Overview
Contact your account representative for more information.
workshops@infotech.com 1-888-670-8889
| Day 1 | Day 2 | Day 3 | Day 4 | Day 5 | |
|---|---|---|---|---|---|
Initial Security |
Refine Security |
Security Program |
Roadmap and Implementation Plan |
Next Steps and |
|
Activities |
1.1.0 Review Info-Tech diagnostic results 1.1.1 Identify project context 1.1.2 Identify enterprise strategy 1.2.1 Identify enterprise goals 1.2.2 Build a goals cascade 1.3 Assess the risk profile 1.4 Identify IT-related issues 1.5 Evaluate initial program design |
2.1.1 Gauge threat landscape 2.1.2 Identify compliance requirements 2.2.1 Categorize the role of IT 2.2.2 Identify the sourcing model 2.3.1 Identify the IT implementation model 2.4.1 Identify the tech adoption strategy 2.5.1 Refine the design of the program |
3.1 Identify program accountabilities 3.2.1 Conduct program gap analysis 3.2.2 Prioritize initiatives |
3.3.1 Build program roadmap 3.3.2 Finalize implementation plan 3.3.3 Sponsor check-in |
4.1 Complete in-progress deliverables from previous four days 4.2 Set up review time for workshop deliverables and to discuss next steps |
Deliverables |
|
|
|
|
|
Customize your journey
The security design blueprint pairs well with security governance and security strategy.
- The prioritized set of security capabilities you develop during the program design project will inform efforts to develop other parts of your security program, like the security governance and management program and the security strategy.
- Work with your member services director, executive advisor, or technical counselor to scope the journey you need. They will work with you to align the subject matter experts to support your roadmap and workshops.
Workshop |
Workshop |
|---|---|
Security Program Design Factors |
Security Program Gap Analysis or |
