Passwordless Authentication

- Stakeholders believe that passwords are still good enough.
- You don’t know how the vendor products match to the capabilities you need to offer.
- What do you need to test when you prototype these new technologies?
- What associated processes/IT domains will be impacted or need to be considered?
Our Advice
Critical Insight
Passwordless is the right direction even if it’s not your final destination.
Impact and Result
- Be able to handle objections from those who believe passwords are still “fine.”
- Prioritize the capabilities you need to offer the enterprise, and match them to products/features you can buy from vendors.
- Integrate passwordless initiatives with other key functions (cloud, IDaM, app rationalization, etc.).
Passwordless Authentication Research & Tools
Besides the small introduction, subscribers and consulting clients within this management domain have access to:
1. Passwordless Authentication – Know when you’ve been beaten!
Back in 2004 we were promised "the end of passwords" – why, then, are we still struggling with them today?
- Passwordless Authentication Storyboard
Further reading
Passwordless Authentication
Know when you've been beaten!
Executive Summary
Your Challenge
- The IT world is an increasingly dangerous place.
- Every year literally billions of credentials are compromised and exposed on the internet.
- The average employee has between 27 and 191 passwords to manage.
- The line between business persona and personal persona has been blurred into irrelevancy.
- You need a method of authenticating users that is up to these challenges
Common Obstacles
- Legacy systems aside (wouldn't that be nice) this still won't be easy.
- Social inertia – passwords worked before, so surely, they can still work today! Besides, users don't want to change.
- Analysis paralysis – I don't want to get this wrong! How do I choose something that is going to be at the core of my infrastructure for the next 10 years?
- Identity management – how can you fix authentication when people have multiple usernames?
Info-Tech's Approach
- Inaction is not an option.
- Most commercial, off-the-shelf apps are moving to a SaaS model, so start your efforts with them.
- Your existing vendors already have technologies you are underusing or ignoring – stop that!
- Your users want this change – they just might not know it yet…
- Much like zero trust network access, the journey is more important than the destination. Incremental steps on the path toward passwordless authentication will still yield significant benefits.
Info-Tech Insight
Users have been burdened with unrealistic expectations when it comes to their part in maintaining enterprise security. Given the massive rise in the threat landscape, it is time for Infrastructure to adopt a user-experience-based approach if we want to move the needle on improving security posture.
Password Security Fallacy
"If you buy the premise…you buy the bit."
Johnny Carson
We've had plenty of time to see this coming.
Why haven't we done something?
- Passwords are a 1970s construct.
- End-users are complexity averse.
- Credentials are leaked all the time.
- New technologies will defeat even the most complex passwords.
Build the case, both to business stakeholders and end users, that "password" is not a synonym for "security."
Be ready for some objection handling!

RSA Conference, 2004
San Francisco, CA
"There is no doubt that over time, people are going to rely less and less on passwords. People use the same password on different systems, they write them down and they just don't meet the challenge for anything you really want to secure."
Bill Gates
What about "strong" passwords?
There has been a password arms race going on since 1988
A massive worm attack against ARPANET prompted the initial research into password strength
Password strength can be expressed as a function of randomness or entropy. The greater the entropy the harder for an attacker to guess the password.
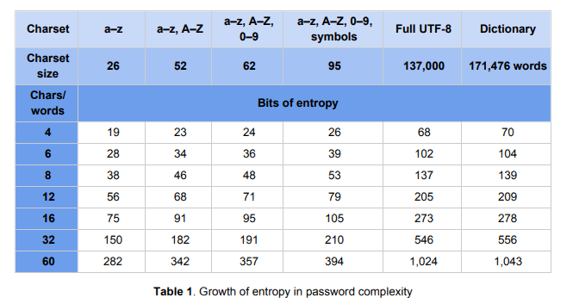
Table: Modern password security for users
Ian Maddox and Kyle Moschetto, Google Cloud Solutions Architects
From this research, increasing password complexity (length, special characters, etc.) became the "best practice" to secure critical systems.
How many passwords??
XKCD Comic #936 (published in 2011)
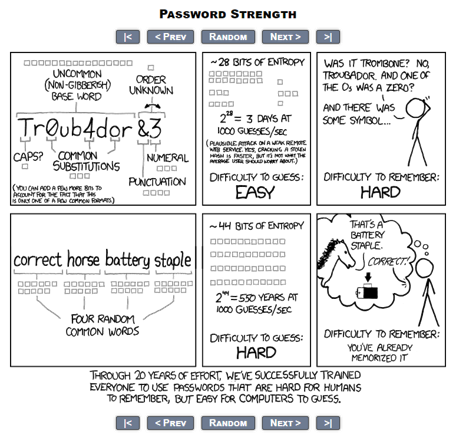
Image courtesy of Randall Munroe XKCD Comics (CC BY-NC 2.5)
It turns out that humans however are really bad at remembering complex passwords.
An Intel study (2016) suggested that the average enterprise employee needed to remember 27 passwords. A more recent study from LastPass puts that number closer to 191.
PEBKAC
Problem Exists Between Keyboard and Chair
Increasing entropy is the wrong way to fight this battle – which is good because we'd lose anyway.
Over the course of a single year, researchers at the University of California, Berkeley identified and tracked nearly 2 billion compromised credentials.
3.8 million were obtained via social engineering, another 788K from keyloggers. That's approx. 250,000 clear text credentials harvested every week!
The entirety of the password ecosystem has significant vulnerabilities in multiple areas:
- Unencrypted server- and client-side storage
- Sharing
- Reuse
- Phishing
- Keylogging
- Question-based resets
Even the 36M encrypted credentials compromised every week are just going to be stored and cracked later.
Source: Google, University of California, Berkeley, International Computer Science Institute
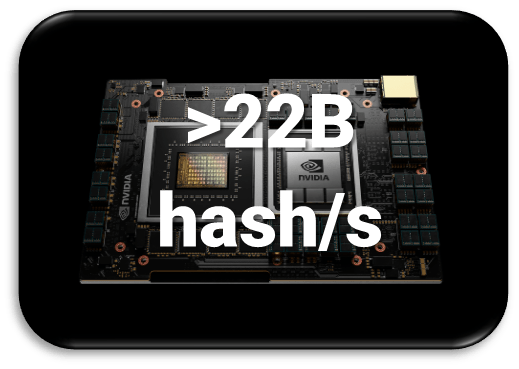
Image courtesy of NVIDIA, NVIDIA Grace |
|
Image: IBM Quantum System One (CES 2020) by IBM Research is licensed under CC BY-ND 2.0 |
|
Enabling Technologies
"Give me a place to stand, and a lever long enough, and I will move the world."
Archimedes
Technology gives us (too many) options
The time to prototype is NOW!
Chances are you are already paying for one or more of these technologies from a current vendor:
- SSO, password managers
- Conditional access
- Multifactor
- Hardware tokens
- Biometrics
- PINs
Address all three factors of authentication
- Something the user knows
- Something the user has
- Something the user is
Global Market of $12.8B
~16.7% CAGR
Source: Report Linker, 2022.
Focus your prototype efforts in four key testing areas
- Deployment
- User adoption/training
- Architecture (points of failure)
- Disaster recovery
Three factors for positive identification
Passwordless technologies focus on alternate authentication factors to supplement or replace shared secrets.
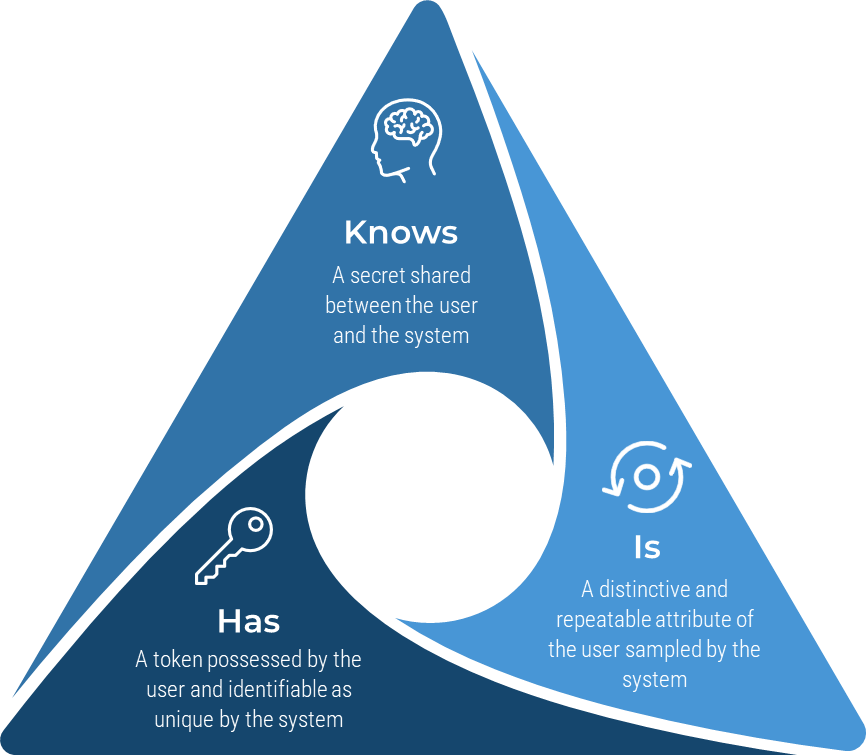 |
Something you knowShared secrets have well-known significant modern-day problems, but only when used in isolation. For end users, consider time-limited single use options, password managers, rate-limited login attempts, and reset rather than retrieval requests. On the system side, never forget strong cryptographic hashing along with a side of salt and pepper when storing passwords. Something you haveA token (now known as a cryptographic identification device) such as a pass card, fob, smartphone, or USB key that is expected to be physically under the control of the user and is uniquely identifiable by the system. Easily decoupled in the event the token is lost, but potentially expensive and time-consuming to reprovision. Something you are or doCommonly referred to as biometrics, there are two primary classes. The first is measurable physical characteristics of the user such as a fingerprint, facial image, or retinal scan. The second class is a series of behavioral traits such as expected location, time of day, or device. These traits can be linked together in a conditional access policy. Unlike other authentication factors, biometrics DO NOT provide for exact matches and instead rely on a confidence interval. A balance must be struck against the user experience of false negatives and the security risk of a false positive. |
Prototype testing criteria
Deployment
Does the solution support the full variety of end-user devices you have in use?
Can the solution be configured with your existing single sign-on or central identity broker?
User Experience
Users already want a better experience than passwords.
What new behavior are you expecting (compelling) from the user?
How often and under what conditions will that behavior occur?
Architecture
Where are the points of failure in the solution?
Consider technical elements like session thresholds for reauthorization, but also elements like automation and self-service.
Disaster Recovery
Understand the exact responsibilities Infra&Ops have in the event of a system or user failure.
As many solutions are based in the public cloud, manage stakeholder expectations accordingly.
Next Steps
"Move the goalposts…and declare victory."
Informal Fallacy (yet very effective…)
It is more a direction than a destination…
Get the easy wins in the bank and then lay the groundwork for the long campaign ahead.
You're not going to get to a passwordless world overnight. You might not even get there for many years. But an agile approach to the journey ensures you will realize value every step of the way:
- Start in the cloud:
- Choose a single sign-on platform such as Azure Active Directory, Okta, Auth0, AWS IAM, TruSONA, HYPR, or others. Document Your Cloud Strategy.
- Integrate the SaaS applications from your portfolio with your chosen platform.
- Establish visibility and rationalize identity management:
- Accounts with elevated privileges present the most risk – evaluate your authentication factors for these accounts first.
- There is elegance (and deployment success) in Simplifying Identity & Access Management.
- Pay your tech debt:
- Legacy apps that don't even support SAML are going to have to be upgraded or isolated.
- Recoding an application can easily take 6-12 months of work – prioritize this when Building an Application Rationalization Framework.
Fast IDentity Online (2) is now part of the web's DNA and is critical for digital transformation
- IoT
- Anywhere remote work
- Government identity services
- Digital wallets
Bibliography
"Backup Vs. Archiving: Know the Difference." Open-E. Accessed 05 Mar 2022.Web.
G, Denis. "How to Build Retention Policy." MSP360, Jan 3, 2020. Accessed 10 Mar 2022.
Ipsen, Adam. "Archive Vs. Backup: What's the Difference? A Definition Guide." BackupAssist, 28 Mar 2017. Accessed 04 Mar 2022.
Kang, Soo. "Mitigating the Expense of E-Discovery; Recognizing the Difference Between Back-Ups and Archived Data." Zasio Enterprises, 08 Oct 2015. Accessed 3 Mar 2022.
Mayer, Alex. "The 3-2-1 Backup Rule – An Efficient Data Protection Strategy." Naviko. Accessed 12 Mar 2022.
Steel, Amber. "LastPass Reveals 8 Truths about Passwords in the New Password Exposé." LastPass Blog, 1 Nov. 2017. Web.
"The Global Passwordless Authentication Market Size Is Estimated to Be USD 12.79 Billion in 2021 and Is Predicted to Reach USD 53.64 Billion by 2030 With a CAGR of 16.7% From 2022-2030." Report Linker, 9 June 2022. Web.
"What Is Data-Archiving?" Proofpoint. Accessed 07 Mar 2022.
Buying Options
Passwordless Authentication
IT Risk Management · IT Leadership & Strategy implementation · Operational Management · Service Delivery · Organizational Management · Process Improvements · ITIL, CORM, Agile · Cost Control · Business Process Analysis · Technology Development · Project Implementation · International Coordination · In & Outsourcing · Customer Care · Multilingual: Dutch, English, French, German, Japanese · Entrepreneur
Tymans Group is a brand by Gert Taeymans BV
Gert Taeymans bv
Europe: Koning Albertstraat 136, 2070 Burcht, Belgium — VAT No: BE0685.974.694 — phone: +32 (0) 468.142.754
USA: 4023 KENNETT PIKE, SUITE 751, GREENVILLE, DE 19807 — Phone: 1-917-473-8669
Copyright 2017-2022 Gert Taeymans BV
 22B hash/s">
22B hash/s">